手动安全性关联
示例:配置手动 SA
此示例说明如何使用手册安全关联 (SA) 创建 IPsec 隧道,包含以下部分:
要求
此示例使用以下硬件和软件组件:
四台安装有多服务接口的 M Series、MX 系列 或 T Series 路由器。
Junos OS 9.4 及更高版本。
在配置此功能之前,不需要除设备初始化之外的特殊配置。
概述和拓扑
安全关联 (SA) 是一种单工连接,使两台主机能够通过 IPsec 安全地相互通信。SA 有两种类型:手册 SA 和动态 SA。此示例介绍了手册 SA 配置。
手动 SA 不需要协商;所有值(包括键)都是静态的,并在配置中指定。手动 SA 使用静态定义的安全参数索引 (SPI) 值、算法和密钥,并且需要在隧道的两端进行匹配的配置。每个对等方必须具有相同的配置选项才能进行通信。
手动 SA 最适合密钥分配、维护和跟踪难度不大的小型静态网络。
拓扑结构
图 1 显示了包含一组四台路由器的 IPsec 拓扑:路由器 1、2、3 和 4。
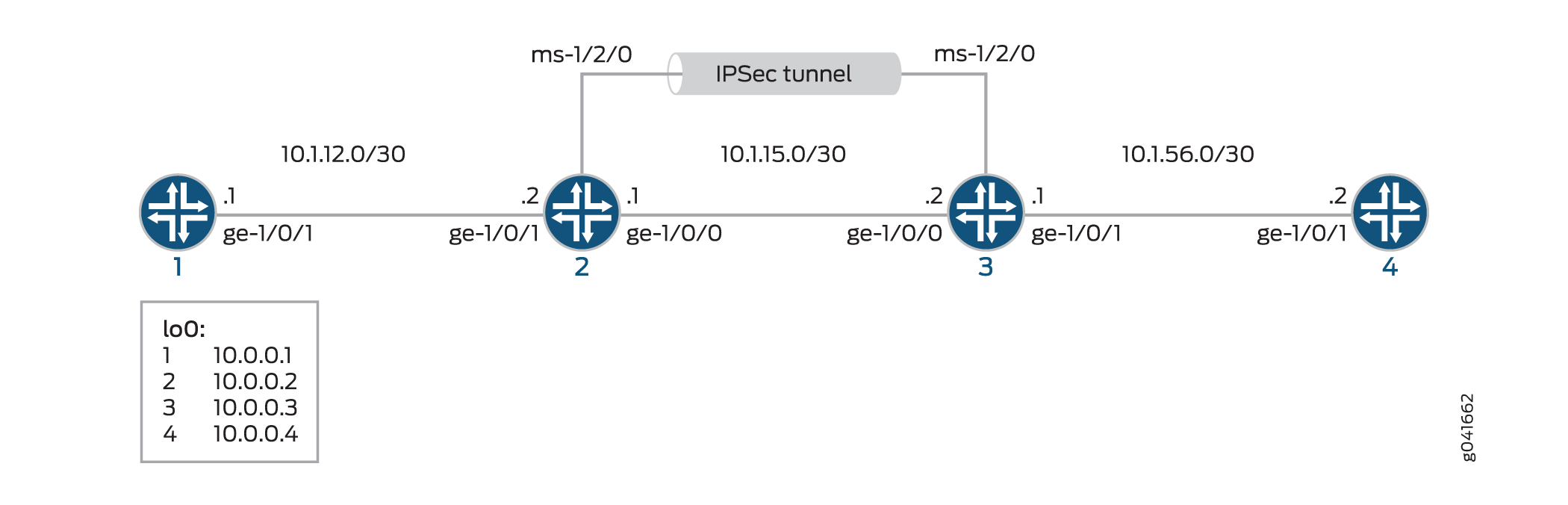
路由器 2 和 3 使用多服务 PIC 和手册 SA 设置建立 IPsec 隧道。路由器 1 和 4 提供基本连接,用于验证 IPsec 隧道是否正常运行。
配置
此示例使用四台路由器,涉及以下配置:
路由器 1 和 4 分别配置为与路由器 2 和 3 建立基本 OSPF 连接。
路由器 2 和 3 分别配置为与路由器 1 和 4 进行 OSPF 连接。路由器 2 和 3 还配置为使用手册 SA 在这两台路由器之间创建 IPsec 隧道。要通过多服务接口将流量引导至 IPsec 隧道,请在路由器 2 和 3 上配置下一跃点样式的服务集,并将配置为 IPsec 内部接口的多服务接口添加到相应路由器上的 OSPF 配置中。
此示例中显示的接口类型仅供参考。例如,您可以使用 so- 接口代替 ge- sp- ms-和 。
本节包含:
配置路由器 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,然后将命令复制并粘贴到路由器 1 的 [edit] 层级的 CLI 中。
set interfaces ge-1/0/1 description "to R2 ge-1/0/1" set interfaces ge-1/0/1 unit 0 family inet address 10.1.12.1/30 set interfaces lo0 unit 0 family inet address 10.0.0.1/32 set protocols ospf area 0.0.0.0 interface ge-1/0/1.0 set protocols ospf area 0.0.0.0 interface lo0.0 set routing-options router-id 10.0.0.1
分步程序
下面的示例要求您在各个配置层级中进行导航。有关导航 CLI 的信息,请参阅 《CLI 用户指南》中的在配置模式下使用 CLI 编辑器。
要配置路由器 1 以便与路由器 2 建立 OSPF 连接:
配置以太网接口和环路接口。
[edit interfaces] user@router1# set ge-1/0/1 description "to R2 ge-1/0/1" user@router1# set ge-1/0/1 unit 0 family inet address 10.1.12.1/30 user@router1# set lo0 unit 0 family inet address 10.0.0.1/32
指定 OSPF 区域,并将接口与 OSPF 区域相关联。
[edit protocols] user@router1# set ospf area 0.0.0.0 interface ge-1/0/1.0 user@router1# set ospf area 0.0.0.0 interface lo0.0
配置路由器 ID。
[edit routing-options] user@router1# set router-id 10.0.0.1
结果
在配置模式下,输入 show interfaces、 show protocols ospf和 show routing-options 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明以更正配置
user@router1# show interfaces
interfaces {
...
ge-1/0/1 {
description "to R2 ge-1/0/1";
unit 0 {
family inet {
address 10.1.12.1/30;
}
}
}
lo0 {
unit 0 {
family inet {
address 10.0.0.1/32;
}
}
}
...
}
user@router1# show protocols ospf
ospf {
area 0.0.0.0 {
interface ge-1/0/1.0;
interface lo0.0;
}
}
user@router1# show routing-options
routing-options {
router-id 10.0.0.1;
}
配置路由器 2
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,然后将命令复制并粘贴到路由器 2 层次结构级别的 CLI 中。
在路由器 2 上配置接口和 OSPF 连接(使用路由器 1 和路由器 3)
set interfaces ge-1/0/0 unit 0 description "to R3 ge-1/0/0" set interfaces ge-1/0/0 unit 0 family inet address 10.1.15.1/30 set interfaces ge-1/0/1 unit 0 description "to R1 ge-1/0/0" set interfaces ge-1/0/1 unit 0 family inet address 10.1.12.2/30 set interfaces ms-1/2/0 unit 0 family inet set interfaces ms-1/2/0 unit 1 family inet set interfaces ms-1/2/0 unit 1 service-domain inside set interfaces ms-1/2/0 unit 2 family inet set interfaces ms-1/2/0 unit 2 service-domain outside set interfaces lo0 unit 0 family inet address 10.0.0.2/32 set protocols ospf area 0.0.0.0 interface ge-1/0/1.0 set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface ms-1/2/0.1 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then remote-gateway 10.1.15.2 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional protocol esp set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional spi 261 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication algorithm hmac-sha1-96 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication key ascii-text demokeyipsecmanualsa set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption algorithm des-cbc set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption key ascii-text manualsa set services ipsec-vpn rule demo-rule-r1-manual-sa match-direction input set services service-set demo-ss-manual-sa next-hop-service inside-service-interface ms-1/2/0.1 set services service-set demo-ss-manual-sa next-hop-service outside-service-interface ms-1/2/0.2 set services service-set demo-ss-manual-sa ipsec-vpn-options local-gateway 10.1.15.1 set services service-set demo-ss-manual-sa ipsec-vpn-rules demo-rule-r1-manual-sa
分步程序
下面的示例要求您在各个配置层级中进行导航。有关导航 CLI 的信息,请参阅 《CLI 用户指南》中的在配置模式下使用 CLI 编辑器。
要在路由器 2 上配置 OSPF 连接和 IPsec 隧道参数:
配置接口属性。在此步骤中,您将配置两个以太网接口(ge-1/0/0 和 ge-1/0/1)、一个环路接口和一个多服务接口 (ms-1/2/0)。
[edit interfaces] user@router2# set ge-1/0/0 unit 0 description "to R3 ge-1/0/0" user@router2# set ge-1/0/0 unit 0 family inet address 10.1.15.1/30 user@router2# set ge-1/0/1 unit 0 description "to R1 ge-1/0/0" user@router2# set ge-1/0/1 unit 0 family inet address 10.1.12.2/30 user@router2# set ms-1/2/0 unit 0 family inet user@router2# set ms-1/2/0 unit 1 family inet user@router2# set ms-1/2/0 unit 1 service-domain inside user@router2# set ms-1/2/0 unit 2 family inet user@router2# set ms-1/2/0 unit 2 service-domain outside user@router2# set lo0 unit 0 family inet address 10.0.0.2/32
指定 OSPF 区域,并将接口与 OSPF 区域相关联。
[edit protocols] user@router2# set ospf area 0.0.0.0 interface ge-1/0/1.0 user@router2# set ospf area 0.0.0.0 interface lo0.0 user@router2# set ospf area 0.0.0.0 interface ms-1/2/0.1
配置路由器 ID。
[edit routing-options] user@router2# set router-ID 10.0.0.2
配置 IPsec 规则。在此步骤中,您将配置 IPsec 规则并指定手册 SA 参数,例如远程网关地址、身份验证和加密属性等。
[edit services ipsec-vpn] user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then remote-gateway 10.1.15.2 user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional protocol esp user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional spi 261 user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication algorithm hmac-sha1-96 user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication key ascii-text demokeyipsecmanualsa user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption algorithm des-cbc user@router2# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption key ascii-text manualsa user@router2# set rule demo-rule-r1-manual-sa match-direction input
配置下一跃点样式的服务集,指定本地网关地址,并将 IPsec VPN 规则与服务集相关联。
[edit services] user@router2# set service-set demo-ss-manual-sa next-hop-service inside-service-interface ms-1/2/0.1 user@router2# set service-set demo-ss-manual-sa next-hop-service outside-service-interface ms-1/2/0.2 user@router2# set service-set demo-ss-manual-sa ipsec-vpn-options local-gateway 10.1.15.1 user@router2# set service-set demo-ss-manual-sa ipsec-vpn-rules demo-rule-r1-manual-sa
提交配置。
[edit] user@router2# commit
结果
在配置模式下,输入 show interfaces、 show protocols ospf、 show routing-options和 show services 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明以更正配置
user@router1# show interfaces
interfaces {
...
ge-1/0/0 {
unit 0 {
description "to R3 ge-1/0/0";
family inet {
address 10.1.15.1/30;
}
}
}
ge-1/0/1 {
unit 0 {
description "to R1 ge-1/0/1";
family inet {
address 10.1.12.2/30;
}
}
}
ms-1/2/0 {
unit 0 {
family inet;
}
unit 1 {
family inet;
service-domain inside;
}
unit 2 {
family inet;
service-domain outside;
}
}
lo0 {
unit 0 {
family inet {
address 10.0.0.2/32;
}
}
}
...
}
user@router2# show protocols ospf
protocols {
ospf {
area 0.0.0.0 {
interfaces ge-1/0/1.0;
interface lo0;
interface ms-1/2/0;
}
}
}
user@router2# show routing-options
routing-options {
router-id 10.0.0.2;
}
user@router2# show services
services {
ipsec-vpn {
rule demo-rule-r1-manual-sa {
term demo-term-manual-sa {
then {
remote-gateway 10.1.15.2;
manual {
direction bidirectional {
protocol esp;
spi 261;
authentication {
algorithm hmac-sha1-96;
key ascii-text "$ABC1223"; ## SECRET-DATA
}
encryption {
algorithm des-cbc;
key ascii-text "$ABC123"; ## SECRET-DATA
}
}
}
}
}
match-direction input;
}
}
service-set demo-ss-manual-sa {
next-hop-service {
inside-service-interface ms-1/2/0.1;
outside-service-interface ms-1/2/0.2;
}
ipsec-vpn-options {
local-gateway 10.1.15.1;
}
ipsec-vpn-rules demo-rule-r1-manual-sa;
}
}
配置路由器 3
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,然后将命令复制并粘贴到路由器 3 的 [edit] 层级的 CLI 中。
set interfaces ge-1/0/1 unit 0 description "to R4 ge-1/0/1" set interfaces ge-1/0/0 unit 0 family inet address 10.1.56.1/30 set interfaces ge-1/0/0 unit 0 description "to R2 ge-1/0/0" set interfaces ge-1/0/0 unit 0 family inet address 10.1.15.2/30 set interfaces ms-1/2/0 unit 0 family inet set interfaces ms-1/2/0 unit 1 family inet set interfaces ms-1/2/0 unit 1 service-domain inside set interfaces ms-1/2/0 unit 2 family inet set interfaces ms-1/2/0 unit 2 service-domain outside set interfaces lo0 unit 0 family inet address 10.0.0.3/32 set protocols ospf area 0.0.0.0 interface ge-1/0/1.0 set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface ms-1/2/0.1 set routing-options router-id 10.0.0.3 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then remote-gateway 10.1.15.1 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional protocol esp set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional spi 261 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication algorithm hmac-sha1-96 set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication key ascii-text demokeyipsecmanualsa set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption algorithm des-cbc set services ipsec-vpn rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption key ascii-text manualsa set services ipsec-vpn rule demo-rule-r1-manual-sa match-direction input set services service-set demo-ss-manual-sa next-hop-service inside-service-interface ms-1/2/0.1 set services service-set demo-ss-manual-sa next-hop-service outside-service-interface ms-1/2/0.2 set services service-set demo-ss-manual-sa ipsec-vpn-options local-gateway 10.1.15.2 set services service-set demo-ss-manual-sa ipsec-vpn-rules demo-rule-r1-manual-sa
分步程序
下面的示例要求您在各个配置层级中进行导航。有关导航 CLI 的信息,请参阅 《CLI 用户指南》中的在配置模式下使用 CLI 编辑器。
要在路由器 3 上配置 OSPF 连接和 IPsec 隧道参数:
配置接口属性。在此步骤中,您将配置两个以太网接口(ge-1/0/0 和 ge-1/0/1)、一个环路接口和一个多服务接口 (ms-1/2/0)。
[edit interfaces] user@router3# set ge-1/0/0 unit 0 description "to R4 ge-1/0/0" user@router3# set ge-1/0/0 unit 0 family inet address 10.1.56.1/30 user@router3# set ge-1/0/1 unit 0 description "to R2 ge-1/0/1" user@router3# set ge-1/0/1 unit 0 family inet address 10.1.15.2/30 user@router3# set ms-1/2/0 unit 0 family inet user@router3# set ms-1/2/0 unit 1 family inet user@router3# set ms-1/2/0 unit 1 service-domain inside user@router3# set ms-1/2/0 unit 2 family inet user@router3# set ms-1/2/0 unit 2 service-domain outside user@router3# set lo0 unit 0 family inet address 10.0.0.3/32
指定 OSPF 区域,并将接口与 OSPF 区域相关联。
[edit protocols] user@router3# set ospf area 0.0.0.0 interface ge-1/0/1.0 user@router3# set ospf area 0.0.0.0 interface lo0.0 user@router3# set ospf area 0.0.0.0 interface ms-1/2/0.1
配置路由器 ID。
[edit routing-options] user@router3# set router-id 10.0.0.3
配置 IPsec 规则。在此步骤中,您将配置 IPsec 规则并指定手册 SA 参数,例如远程网关地址、身份验证和加密属性等。
[edit services ipsec-vpn] user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then remote-gateway 10.1.15.1 user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional protocol esp user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional spi 261 user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication algorithm hmac-sha1-96 user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional authentication key ascii-text demokeyipsecmanualsa user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption algorithm des-cbc user@router3# set rule demo-rule-r1-manual-sa term demo-term-manual-sa then manual direction bidirectional encryption key ascii-text manualsa user@router3# set rule demo-rule-r1-manual-sa match-direction input
配置下一跃点样式的服务集,指定本地网关地址,并将 IPsec VPN 规则与服务集相关联。
[edit services] user@router3# set service-set demo-ss-manual-sa next-hop-service inside-service-interface ms-1/2/0.1 user@router3# set service-set demo-ss-manual-sa next-hop-service outside-service-interface ms-1/2/0.2 user@router3# set service-set demo-ss-manual-sa ipsec-vpn-options local-gateway 10.1.15.2 user@router3# set service-set demo-ss-manual-sa ipsec-vpn-rules demo-rule-r1-manual-sa
提交配置。
[edit] user@router3# commit
结果
在配置模式下,输入 show interfaces、 show protocols ospf、 show routing-options和 show services 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明以更正配置
user@router3# show interfaces
interfaces {
ge-1/0/1 {
unit 0 {
description "to R4 ge-1/0/1";
family inet {
address 10.1.56.1/30;
}
}
}
ge-1/0/0 {
unit 0 {
description "to R2 ge-1/0/0";
family inet {
address 10.1.15.2/30;
}
}
}
ms-1/2/0 {
unit 0 {
family inet;
}
unit 1 {
family inet;
service-domain inside;
}
unit 2 {
family inet;
service-domain outside;
}
}
lo0 {
unit 0 {
family inet {
address 10.0.0.3/32;
}
}
}
}
user@router3# show protocols ospf
protocols {
ospf {
area 0.0.0.0 {
interface ge-1/0/1.0;
interface lo0.0;
interface ms-1/2/0.1;
}
}
}
user@router3# show routing-options
routing-options {
router-id 10.0.0.3;
}
user@router3# show services
services {
ipsec-vpn {
rule demo-rule-r1-manual-sa {
term demo-term-manual-sa {
then {
remote-gateway 10.1.15.1;
manual {
direction bidirectional {
protocol esp;
spi 261;
authentication {
algorithm hmac-sha1-96;
key ascii-text "$ABC123"; ## SECRET-DATA
}
encryption {
algorithm des-cbc;
key ascii-text "$ABC123"; ## SECRET-DATA
}
}
}
}
}
match-direction input;
}
}
service-set demo-ss-manual-sa {
next-hop-service {
inside-service-interface ms-1/2/0.1;
outside-service-interface ms-1/2/0.2;
}
ipsec-vpn-options {
local-gateway 10.1.15.2;
}
ipsec-vpn-rules demo-rule-r1-manual-sa;
}
}
配置路由器 4
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,然后将命令复制并粘贴到路由器 4 层次结构级别的 CLI 中。
set interfaces ge-1/0/1 description "to R3 ge-1/0/1" set interfaces ge-1/0/1 unit 0 family inet address 10.1.56.2/30 set interfaces lo0 unit 0 family inet address 10.0.0.4/32 set protocols ospf area 0.0.0.0 interface ge-1/0/1.0 set protocols ospf area 0.0.0.0 interface lo0.0 set routing-options router-id 10.0.0.4
分步程序
下面的示例要求您在各个配置层级中进行导航。有关导航 CLI 的信息,请参阅 《CLI 用户指南》中的在配置模式下使用 CLI 编辑器。
要设置与路由器 3 的 OSPF 连接
配置接口。在此步骤中,您将配置一个以太网接口 (ge-1/0/1) 和一个环路接口。
user@router4# set interfaces ge-1/0/1 description "to R3 ge-1/0/1" user@router4# set interfaces ge-1/0/1 unit 0 family inet address 10.1.56.2/30 user@router4# set interfaces lo0 unit 0 family inet address 10.0.0.4/32
指定 OSPF 区域,并将接口与 OSPF 区域相关联。
user@router4# set protocols ospf area 0.0.0.0 interface ge-1/0/1.0 user@router4# set protocols ospf area 0.0.0.0 interface lo0.0
配置路由器 ID。
[edit routing-options] user@router4# set router-id 10.0.0.4
提交配置。
[edit] user@router4# commit
结果
在配置模式下,输入 show interfaces、 show protocols ospf和 show routing-options 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明以更正配置
user@router4# show interfaces
interfaces {
ge-1/0/1 {
description "to R3 ge-1/0/1";
unit 0 {
family inet {
address 10.1.56.2/30;
}
}
}
lo0{
unit 0 {
family inet {
address 10.0.0.4/32;
}
}
}
}
user@router4# show routing-options
routing-options {
router-id 10.0.0.4;
}
user@router4# show protocols ospf
protocols {
ospf {
area 0.0.0.0 {
interface lo0.0;
interface ge-1/0/1.0;
}
}
}
验证
要确认手册 SA 配置工作正常,请执行以下任务:
验证通过 IPsec 隧道的流量
目的
验证 IPsec 隧道是否在路由器 1 和路由器 4 之间传输流量。
行动
ping从路由器 1 向lo0路由器 4 发出命令。
user@router1> ping 10.0.0.4 PING 10.0.0.4 (10.0.0.4): 56 data bytes 64 bytes from 10.0.0.4: icmp_seq=0 ttl=254 time=1.375 ms 64 bytes from 10.0.0.4: icmp_seq=1 ttl=254 time=18.375 ms 64 bytes from 10.0.0.4: icmp_seq=2 ttl=254 time=1.120 ms ^C --- 10.0.0.4 ping statistics --- 3 packets transmitted, 3 packets received, 0% packet loss round-trip min/avg/max/stddev = 1.120/6.957/18.375/8.075 ms
意义
输出显示路由器 1 能够通过 IPsec 隧道到达路由器 4。
验证路由器 2 上的安全性关联
目的
验证安全关联是否在路由器 2 上处于活动状态,以及流量是否正在通过 IPsec 隧道发送。
行动
要验证安全关联是否处于活动状态,请在路由器 2 上发出问题
show services ipsec-vpn ipsec security-associations detail。user@router2> show services ipsec-vpn ipsec security-associations detail Service set: demo-ss-manual-sa Rule: demo-rule-r1-manual-sa, Term: demo-term-manual-sa, Tunnel index: 1 Local gateway: 10.1.15.1, Remote gateway: 10.1.15.2 Local identity: ipv4_subnet(any:0,[0..7]=10.0.0.0/8) Remote identity: ipv4_subnet(any:0,[0..7]=0.0.0.0/0) Direction: inbound, SPI: 261, AUX-SPI: 0 Mode: tunnel, Type: manual, State: Installed Protocol: ESP, Authentication: hmac-sha1-96, Encryption: des-cbc Anti-replay service: Disabled Direction: outbound, SPI: 261, AUX-SPI: 0 Mode: tunnel, Type: manual, State: Installed Protocol: ESP, Authentication: hmac-sha1-96, Encryption: des-cbc Anti-replay service: Disabled
要验证流量是否通过双向 IPsec 隧道传输,请在路由器 2 上发出问题
show services ipsec-vpn ipsec statistics。user@router2> show services ipsec-vpn ipsec statistics PIC: ms-1/2/0, Service set: demo-ss-manual-sa sESP Statistics: Encrypted bytes: 1616 Decrypted bytes: 1560 Encrypted packets: 20 Decrypted packets: 19 AH Statistics: Input bytes: 0 Output bytes: 0 Input packets: 0 Output packets: 0 Errors: AH authentication failures: 0, Replay errors: 0 ESP authentication failures: 0, ESP decryption failures: 0 Bad headers: 0, Bad trailers: 0
意义
show services ipsec-vpn ipsec security-associations detail命令输出显示您配置的 SA 属性。
命令输出显示 show services ipsec-vpn ipsec statistics 通过 IPsec 隧道的流量。
验证路由器 3 上的安全性关联
目的
验证通过 IPsec 隧道的安全关联和流量。
行动
要验证安全关联是否处于活动状态,请在路由器 3 上发出问题
show services ipsec-vpn ipsec security-associations detail。user@router3> show services ipsec-vpn ipsec security-associations detail Service set: demo-ss-manual-sa Rule: demo-rule-r1-manual-sa, Term: demo-term-manual-sa, Tunnel index: 1 Local gateway: 10.1.15.2, Remote gateway: 10.1.15.1 Local identity: ipv4_subnet(any:0,[0..7]=10.0.0.0/8) Remote identity: ipv4_subnet(any:0,[0..7]=0.0.0.0/0) Direction: inbound, SPI: 261, AUX-SPI: 0 Mode: tunnel, Type: manual, State: Installed Protocol: ESP, Authentication: hmac-sha1-96, Encryption: des-cbc Anti-replay service: Disabled Direction: outbound, SPI: 261, AUX-SPI: 0 Mode: tunnel, Type: manual, State: Installed Protocol: ESP, Authentication: hmac-sha1-96, Encryption: des-cbc Anti-replay service: Disabled
要验证流量是否通过双向 IPsec 隧道传输,请在路由器 3 上发出问题
show services ipsec-vpn ipsec statistics。user@router3> show services ipsec-vpn ipsec statistics PIC: ms-1/2/0, Service set: demo-ss-manual-sa ESP Statistics: Encrypted bytes: 1560 Decrypted bytes: 1616 Encrypted packets: 19 Decrypted packets: 20 AH Statistics: Input bytes: 0 Output bytes: 0 Input packets: 0 Output packets: 0 Errors: AH authentication failures: 0, Replay errors: 0 ESP authentication failures: 0, ESP decryption failures: 0 Bad headers: 0, Bad trailers: 0
意义
show services ipsec-vpn ipsec security-associations detail命令输出显示您配置的 SA 属性。
命令输出显示 show services ipsec-vpn ipsec statistics 通过 IPsec 隧道的流量。
