Example: Creating Tenant Systems, Tenant System Administrators, and an Interconnect VPLS Switch
This example shows how to create tenant systems, tenant system administrators, and an interconnect VPLS switch. Only the primary administrator can create user login accounts for tenant system administrators and interconnect VPLS switch.
Requirements
This example uses the following hardware and software components:
-
SRX Series Firewall.
-
Junos OS Release 18.4R1 and later releases.
-
Before you begin creating the tenant systems, tenant system administrators, and an interconnect VPLS switch, read Tenant Systems Overview to understand how this task fits into the overall configuration process.
Overview
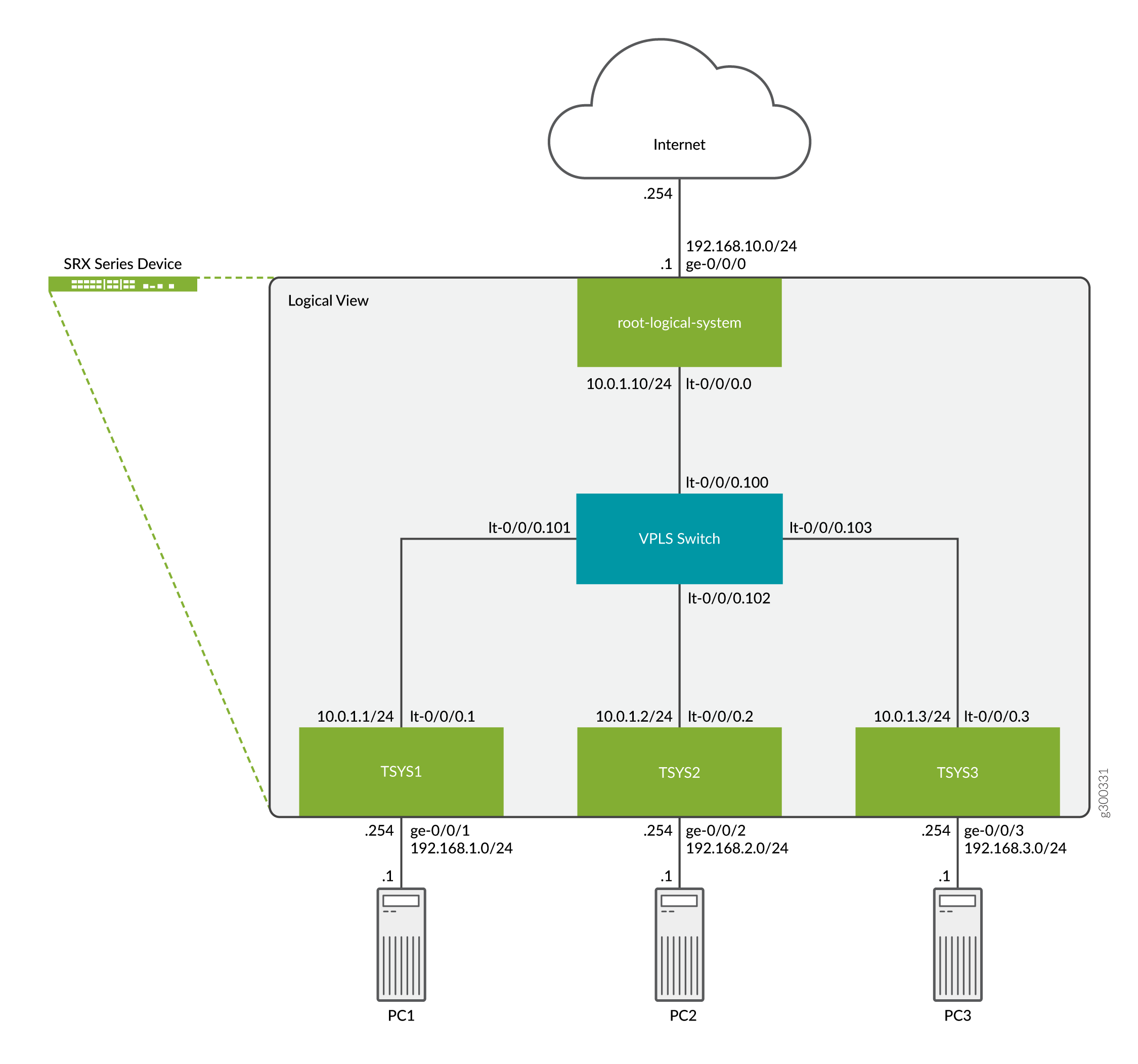
This example shows how to create the tenant systems TSYS1,
TSYS2, and TSYS3, and the tenant system
administrators for them. You can create multiple tenant system administrators for a
tenant system with different permission levels based on your requirements.
This topic also covers the interconnect virtual private LAN service (VPLS) switch connecting one tenant system to another on the same device. The VPLS switch enables both transit traffic and traffic terminated at a tenant system to pass between tenant systems. To allow traffic to pass between tenant systems, logical tunnel (lt-0/0/0) interfaces should be configured in the same subnet.
Topology
The Figure 1 shows an SRX Series Firewall deployed and configured for tenant systems. The configuration example uses static routing to allow the PCs to reach the Internet.
Full SRX Quick Configuration
Configuring Logical and Tenant Systems, and Interconnect VPLS Switch
CLI Quick Configuration
To quickly configure this example, copy the following commands, paste them
into a text file, remove any line breaks, and change any details necessary
to match your network configuration to include interfaces and user
passwords. Then copy and paste the commands into the CLI at the
[edit] hierarchy level, and enter
commit from configuration mode.
set system login class TSYS1admin1 tenant TSYS1 set system login class TSYS1admin1 permissions all set system login class TSYS2admin1 tenant TSYS2 set system login class TSYS2admin1 permissions all set system login class TSYS3admin1 tenant TSYS3 set system login class TSYS3admin1 permissions all set system login user TSYS1admin1 uid 2001 set system login user TSYS1admin1 class TSYS1admin1 set system login user TSYS1admin1 authentication encrypted-password "$ABC123" set system login user TSYS2admin1 uid 2003 set system login user TSYS2admin1 class TSYS2admin1 set system login user TSYS2admin1 authentication encrypted-password "$ABC123" set system login user TSYS3admin1 uid 2005 set system login user TSYS3admin1 class TSYS3admin1 set system login user TSYS3admin1 authentication encrypted-password "$ABC123" set system security-profile SP0 logical-system root-ls set system security-profile SP1 tenant TSYS1 set system security-profile SP2 tenant TSYS2 set system security-profile SP3 tenant TSYS3 set logical-systems root-ls interfaces ge-0/0/0 unit 0 family inet address 192.168.10.1/24 set logical-systems root-ls interfaces lt-0/0/0 unit 0 encapsulation ethernet set logical-systems root-ls interfaces lt-0/0/0 unit 0 peer-unit 100 set logical-systems root-ls interfaces lt-0/0/0 unit 0 family inet address 10.0.1.10/24 set logical-systems root-ls routing-options static route 192.168.1.0/24 next-hop 10.0.1.1 set logical-systems root-ls routing-options static route 192.168.2.0/24 next-hop 10.0.1.2 set logical-systems root-ls routing-options static route 192.168.3.0/24 next-hop 10.0.1.3 set logical-systems root-ls security address-book global address TSYS1 192.168.1.0/24 set logical-systems root-ls security address-book global address TSYS2 192.168.2.0/24 set logical-systems root-ls security address-book global address TSYS3 192.168.3.0/24 set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS1 set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS2 set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS3 set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match destination-address any set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match application any set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out then permit set logical-systems root-ls security zones security-zone trust host-inbound-traffic system-services ping set logical-systems root-ls security zones security-zone trust interfaces lt-0/0/0.0 set logical-systems root-ls security zones security-zone untrust host-inbound-traffic system-services ping set logical-systems root-ls security zones security-zone untrust interfaces ge-0/0/0.0 set interfaces lt-0/0/0 unit 1 encapsulation ethernet set interfaces lt-0/0/0 unit 1 peer-unit 101 set interfaces lt-0/0/0 unit 1 family inet address 10.0.1.1/24 set interfaces lt-0/0/0 unit 2 encapsulation ethernet set interfaces lt-0/0/0 unit 2 peer-unit 102 set interfaces lt-0/0/0 unit 2 family inet address 10.0.1.2/24 set interfaces lt-0/0/0 unit 3 encapsulation ethernet set interfaces lt-0/0/0 unit 3 peer-unit 103 set interfaces lt-0/0/0 unit 3 family inet address 10.0.1.3/24 set interfaces lt-0/0/0 unit 100 encapsulation ethernet-vpls set interfaces lt-0/0/0 unit 100 peer-unit 0 set interfaces lt-0/0/0 unit 101 encapsulation ethernet-vpls set interfaces lt-0/0/0 unit 101 peer-unit 1 set interfaces lt-0/0/0 unit 102 encapsulation ethernet-vpls set interfaces lt-0/0/0 unit 102 peer-unit 2 set interfaces lt-0/0/0 unit 103 encapsulation ethernet-vpls set interfaces lt-0/0/0 unit 103 peer-unit 3 set interfaces ge-0/0/1 unit 0 family inet address 192.168.1.254/24 set interfaces ge-0/0/2 unit 0 family inet address 192.168.2.254/24 set interfaces ge-0/0/3 unit 0 family inet address 192.168.3.254/24 set routing-instances VPLS instance-type vpls set routing-instances VPLS interface lt-0/0/0.100 set routing-instances VPLS interface lt-0/0/0.101 set routing-instances VPLS interface lt-0/0/0.102 set routing-instances VPLS interface lt-0/0/0.103 set tenants TSYS1 routing-instances vr1 instance-type virtual-router set tenants TSYS1 routing-instances vr1 routing-options static route 0.0.0.0/0 next-hop 10.0.1.10 set tenants TSYS1 routing-instances vr1 interface lt-0/0/0.1 set tenants TSYS1 routing-instances vr1 interface ge-0/0/1.0 set tenants TSYS1 security address-book global address PC1 192.168.1.0/24 set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match source-address PC1 set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match destination-address any set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match application any set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out then permit set tenants TSYS1 security zones security-zone PC1 host-inbound-traffic system-services ping set tenants TSYS1 security zones security-zone PC1 interfaces ge-0/0/1.0 set tenants TSYS1 security zones security-zone VPLS host-inbound-traffic system-services ping set tenants TSYS1 security zones security-zone VPLS interfaces lt-0/0/0.1 set tenants TSYS2 routing-instances vr2 instance-type virtual-router set tenants TSYS2 routing-instances vr2 routing-options static route 0.0.0.0/0 next-hop 10.0.1.10 set tenants TSYS2 routing-instances vr2 interface lt-0/0/0.2 set tenants TSYS2 routing-instances vr2 interface ge-0/0/2.0 set tenants TSYS2 security address-book global address PC2 192.168.2.0/24 set tenants TSYS2 security policies from-zone PC2 to-zone VPLS policy allow-out match source-address PC2 set tenants TSYS2 security policies from-zone PC2 to-zone VPLS policy allow-out match destination-address any set tenants TSYS2 security policies from-zone PC2 to-zone VPLS policy allow-out match application any set tenants TSYS2 security policies from-zone PC2 to-zone VPLS policy allow-out then permit set tenants TSYS2 security zones security-zone PC2 host-inbound-traffic system-services ping set tenants TSYS2 security zones security-zone PC2 interfaces ge-0/0/2.0 set tenants TSYS2 security zones security-zone VPLS host-inbound-traffic system-services ping set tenants TSYS2 security zones security-zone VPLS interfaces lt-0/0/0.2 set tenants TSYS3 routing-instances vr3 instance-type virtual-router set tenants TSYS3 routing-instances vr3 routing-options static route 0.0.0.0/0 next-hop 10.0.1.10 set tenants TSYS3 routing-instances vr3 interface lt-0/0/0.3 set tenants TSYS3 routing-instances vr3 interface ge-0/0/3.0 set tenants TSYS3 security address-book global address PC3 192.168.3.0/24 set tenants TSYS3 security policies from-zone PC3 to-zone VPLS policy allow-out match source-address PC3 set tenants TSYS3 security policies from-zone PC3 to-zone VPLS policy allow-out match destination-address any set tenants TSYS3 security policies from-zone PC3 to-zone VPLS policy allow-out match application any set tenants TSYS3 security policies from-zone PC3 to-zone VPLS policy allow-out then permit set tenants TSYS3 security zones security-zone PC3 host-inbound-traffic system-services ping set tenants TSYS3 security zones security-zone PC3 interfaces ge-0/0/3.0 set tenants TSYS3 security zones security-zone VPLS host-inbound-traffic system-services ping set tenants TSYS3 security zones security-zone VPLS interfaces lt-0/0/0.3
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For instructions on how to do that, see Using the CLI Editor in Configuration Mode in the CLI User Guide. We will only be covering the configuration of one tenant for the step-by-step procedure.
-
Create the login user accounts for each tenant. We will only show the steps for creating the tenant
TSYS1user account.-
Create the user login class and assign it to the tenant system.
[edit] user@SRX# set system login class TSYS1admin1 tenant TSYS1
-
Assign a permissions level to the login class, for this example we will use the level
allwhich allows full access to the tenant system administrator.[edit] user@SRX# set system login class TSYS1admin1 permissions all
-
Create a user account and assign it to the class from the previous steps. This will allow the user to login to the tenant system.
[edit] user@SRX# set system login user TSYS1admin1 class TSYS1admin1
-
Create a user login password for the user account.
[edit] user@SRX# set system login user TSYS1admin1 authentication plain-text-password New password: "$ABC123" Retype new password: "$ABC123"
-
-
Configure the VPLS switch. The VPLS switch enables both transit traffic and traffic terminated at a tenant system to pass between tenant systems with a single logical tunnel. Logical tunnel interfaces should be configured in the same subnet to allow traffic between tenant systems.
-
Configure the logical tunnel interfaces.
[edit] user@SRX# set interfaces lt-0/0/0 unit 100 encapsulation ethernet-vpls user@SRX# set interfaces lt-0/0/0 unit 100 peer-unit 0 user@SRX# set interfaces lt-0/0/0 unit 101 encapsulation ethernet-vpls user@SRX# set interfaces lt-0/0/0 unit 101 peer-unit 1 user@SRX# set interfaces lt-0/0/0 unit 102 encapsulation ethernet-vpls user@SRX# set interfaces lt-0/0/0 unit 102 peer-unit 2 user@SRX# set interfaces lt-0/0/0 unit 103 encapsulation ethernet-vpls user@SRX# set interfaces lt-0/0/0 unit 103 peer-unit 3
-
Configure a routing instance for the VPLS switch and assign the logical tunnel interfaces.
[edit] user@SRX# set routing-instances VPLS instance-type vpls user@SRX# set routing-instances VPLS interface lt-0/0/0.100 user@SRX# set routing-instances VPLS interface lt-0/0/0.101 user@SRX# set routing-instances VPLS interface lt-0/0/0.102 user@SRX# set routing-instances VPLS interface lt-0/0/0.103
-
-
Configure the tenant systems. We are only showing the configuration for one tenant.
-
Configure the interfaces associated with the tenant.
[edit] user@SRX# set interfaces lt-0/0/0 unit 1 encapsulation ethernet user@SRX# set interfaces lt-0/0/0 unit 1 peer-unit 101 user@SRX# set interfaces lt-0/0/0 unit 1 family inet address 10.0.1.1/24 user@SRX# set interfaces ge-0/0/1 unit 0 family inet address 192.168.1.254/24
-
Configure the tenant, routing instance, static routing and assign the interfaces.
[edit] user@SRX# set tenants TSYS1 routing-instances vr1 instance-type virtual-router user@SRX# set tenants TSYS1 routing-instances vr1 routing-options static route 0.0.0.0/0 next-hop 10.0.1.10 user@SRX# set tenants TSYS1 routing-instances vr1 interface lt-0/0/0.1 user@SRX# set tenants TSYS1 routing-instances vr1 interface ge-0/0/1.0
-
-
Configure the security profiles. We are only showing the minimal configuration needed to configure logical and tenant systems for this example.
[edit] user@SRX# set system security-profile SP0 logical-system root-ls user@SRX# set system security-profile SP1 tenant TSYS1 user@SRX# set system security-profile SP2 tenant TSYS2 user@SRX# set system security-profile SP3 tenant TSYS3
-
Configure the logical systems. This example using an interconnect VPLS switch requires a logical systems.
-
Configure the interfaces.
[edit] user@SRX# set logical-systems root-ls interfaces ge-0/0/0 unit 0 family inet address 192.168.10.1/24 user@SRX# set logical-systems root-ls interfaces lt-0/0/0 unit 0 encapsulation ethernet user@SRX# set logical-systems root-ls interfaces lt-0/0/0 unit 0 peer-unit 100 user@SRX# set logical-systems root-ls interfaces lt-0/0/0 unit 0 family inet address 10.0.1.10/24
-
Configure the static routes.
[edit] user@SRX# set logical-systems root-ls routing-options static route 192.168.1.0/24 next-hop 10.0.1.1 user@SRX# set logical-systems root-ls routing-options static route 192.168.2.0/24 next-hop 10.0.1.2 user@SRX# set logical-systems root-ls routing-options static route 192.168.3.0/24 next-hop 10.0.1.3
-
-
Configure security zones and policies in the logical systems to allow traffic flow from the tenants to the Internet. Additional security policies can be configured on both the logical and tenant systems to allow traffic between tenants.
-
Configure security zones.
[edit] user@SRX# set logical-systems root-ls security zones security-zone trust host-inbound-traffic system-services ping user@SRX# set logical-systems root-ls security zones security-zone trust interfaces lt-0/0/0.0 user@SRX# set logical-systems root-ls security zones security-zone untrust host-inbound-traffic system-services ping user@SRX# set logical-systems root-ls security zones security-zone untrust interfaces ge-0/0/0.0
-
Configure security policies.
[edit] user@SRX# set logical-systems root-ls security address-book global address TSYS1 192.168.1.0/24 user@SRX# set logical-systems root-ls security address-book global address TSYS2 192.168.2.0/24 user@SRX# set logical-systems root-ls security address-book global address TSYS3 192.168.3.0/24 user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS1 user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS2 user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match source-address TSYS3 user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match destination-address any user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out match application any user@SRX# set logical-systems root-ls security policies from-zone trust to-zone untrust policy allow-out then permit
-
-
Configure security zones and policies in each tenant systems to allow traffic flow to the Internet.
-
Configure security zones.
[edit] user@SRX# set tenants TSYS1 security zones security-zone PC1 host-inbound-traffic system-services ping user@SRX# set tenants TSYS1 security zones security-zone PC1 interfaces ge-0/0/1.0 user@SRX# set tenants TSYS1 security zones security-zone VPLS host-inbound-traffic system-services ping user@SRX# set tenants TSYS1 security zones security-zone VPLS interfaces lt-0/0/0.1
-
Configure security policies.
[edit] user@SRX# set tenants TSYS1 security address-book global address PC1 192.168.1.0/24 user@SRX# set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match source-address PC1 user@SRX# set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match destination-address any user@SRX# set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out match application any user@SRX# set tenants TSYS1 security policies from-zone PC1 to-zone VPLS policy allow-out then permit
-
Results
From configuration mode, confirm your configuration by entering the
show tenants TSYS1 command to verify that the tenant
system is created. Enter the show system login class
TSYS1admin1 command to view the permission level for each class
that you defined. To ensure that the tenant system administrators are
created, enter the show system login user TSYS1admin1
command. To ensure that the interfaces for interconnect VPLS switch are
created, enter the show interfaces command. Enter
show logical-systems to verify the root logical systems
configuration.
user@SRX# show tenants TSYS1
routing-instances {
vr1 {
instance-type virtual-router;
routing-options {
static {
route 0.0.0.0/0 next-hop 10.0.1.10;
}
}
interface lt-0/0/0.1;
interface ge-0/0/1.0;
}
}
security {
address-book {
global {
address PC1 192.168.1.0/24;
}
}
policies {
from-zone PC1 to-zone VPLS {
policy allow-out {
match {
source-address PC1;
destination-address any;
application any;
}
then {
permit;
}
}
}
}
zones {
security-zone PC1 {
host-inbound-traffic {
system-services {
ping;
}
}
interfaces {
ge-0/0/1.0;
}
}
security-zone VPLS {
host-inbound-traffic {
system-services {
ping;
}
}
interfaces {
lt-0/0/0.1;
}
}
}
}user@SRX# show system login class TSYS1admin1 tenant TSYS1; permissions all;
user@SRX# show system login user TSYS1admin1
uid 2001;
class TSYS1admin1;
authentication {
encrypted-password "$ABC123";
}user@SRX# show interfaces
lt-0/0/0 {
unit 1 {
encapsulation ethernet;
peer-unit 101;
family inet {
address 10.0.1.1/24;
}
}
unit 2 {
encapsulation ethernet;
peer-unit 102;
family inet {
address 10.0.1.2/24;
}
}
unit 3 {
encapsulation ethernet;
peer-unit 103;
family inet {
address 10.0.1.3/24;
}
}
unit 100 {
encapsulation ethernet-vpls;
peer-unit 0;
}
unit 101 {
encapsulation ethernet-vpls;
peer-unit 1;
}
unit 102 {
encapsulation ethernet-vpls;
peer-unit 2;
}
unit 103 {
encapsulation ethernet-vpls;
peer-unit 3;
}
}
ge-0/0/1 {
unit 0 {
family inet {
address 192.168.1.254/24;
}
}
}
ge-0/0/2 {
unit 0 {
family inet {
address 192.168.2.254/24;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 192.168.3.254/24;
}
}
}user@SRX# show logical-systems
root-ls {
interfaces {
ge-0/0/0 {
unit 0 {
family inet {
address 192.168.10.1/24;
}
}
}
lt-0/0/0 {
unit 0 {
encapsulation ethernet;
peer-unit 100;
family inet {
address 10.0.1.10/24;
}
}
}
}
routing-options {
static {
route 192.168.1.0/24 next-hop 10.0.1.1;
route 192.168.2.0/24 next-hop 10.0.1.2;
route 192.168.3.0/24 next-hop 10.0.1.3;
}
}
security {
address-book {
global {
address TSYS1 192.168.1.0/24;
address TSYS2 192.168.2.0/24;
address TSYS3 192.168.3.0/24;
}
}
policies {
from-zone trust to-zone untrust {
policy allow-out {
match {
source-address [ TSYS1 TSYS2 TSYS3 ];
destination-address any;
application any;
}
then {
permit;
}
}
}
}
zones {
security-zone trust {
host-inbound-traffic {
system-services {
ping;
}
}
interfaces {
lt-0/0/0.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
ping;
}
}
interfaces {
ge-0/0/0.0;
}
}
}
}
}If the output does not display the intended configuration, repeat the
configuration instructions in these examples to correct it. If you are done
configuring the device, enter commit from configuration
mode.
Verification
Confirm that the configuration is working properly.
- Verifying Tenant Systems and Login Configurations Using Primary Administrator
- Verifying Tenant Systems and Login Configurations Using SSH
- Verifying PC1 Connectivity to the Internet
Verifying Tenant Systems and Login Configurations Using Primary Administrator
Purpose
Verify that the tenant systems exist and you can enter them from root as the primary administrator. Return from the tenant system to the root.
Action
From operational mode, use the following command to enter the tenant systems
TSYS1:
user@SRX> set cli tenant TSYS1 Tenant: TSYS1 user@SRX:TSYS1>
Now you are entered to the tenant systems TSYS1. Use the
following command to exit from tenant systems TSYS1 to the
root:
user@SRX:TSYS1> clear cli tenant Cleared default tenants user@SRX>
Meaning
Tenant system exists and you can enter to the tenant system from the root as the primary administrator.
Verifying Tenant Systems and Login Configurations Using SSH
Purpose
Verify that the tenant systems you created exist, and that the administrator login IDs and passwords that you created are correct.
Action
Use SSH to log in to each user tenant system administrator.
-
Run SSH specifying the IP address of your SRX Series Firewall.
-
Enter the login ID and password for the tenant systems administrator that you created. After you log in, the prompt shows the tenant systems administrator name. Notice how this result differs from the result produced when you log in to the tenant system from the primary logical system at root. Repeat this procedure for all of your tenant systems.
login: TSYS1admin1 Password: "$ABC123" TSYS1admin1@SRX: TSYS1>
Meaning
Tenant system administrator TSYS1admin1 exists and you can
login as the tenant system administrator.
Verifying PC1 Connectivity to the Internet
Purpose
Verify end-to-end connectivity.
Action
Ping and run traceroute to the Internet from PC1. In our example the Internet is 192.168.10.254.
-
Run ping from PC1.
user@PC1> ping 192.168.10.254 count 2 PING 192.168.10.254 (192.168.10.254): 56 data bytes 64 bytes from 192.168.10.254: icmp_seq=0 ttl=62 time=3.178 ms 64 bytes from 192.168.10.254: icmp_seq=1 ttl=62 time=3.082 ms --- 192.168.10.254 ping statistics --- 2 packets transmitted, 2 packets received, 0% packet loss round-trip min/avg/max/stddev = 3.082/3.130/3.178/0.048 ms
-
Run traceroute from PC1.
user@PC1> traceroute 192.168.10.254 traceroute to 192.168.10.254 (192.168.10.254), 30 hops max, 52 byte packets 1 192.168.1.254 (192.168.1.254) 2.188 ms 1.779 ms 1.896 ms 2 10.0.1.10 (10.0.1.10) 1.888 ms 1.535 ms 1.661 ms 3 192.168.10.254 (192.168.10.254) 3.243 ms 15.077 ms 3.499 ms
Meaning
PC1 is able to reach the Internet.
