ON THIS PAGE
Configuring Colorless Ports on EX Series Switches with Aruba ClearPass Policy Manager and Cisco ISE
Starting from Junos OS Release 20.4R1, EX switches support Colorless ports. Colorless ports are used in conjunction with device profiling with any standards-based radius server, and convert an access port to a trunk port and allow the necessary VLANs with necessary tagging. In the case that some of the VLAN’s are missing on the switch, this feature helps in creating those missing VLANs dynamically on the switch.
MAC Auth Bypass (MAB), is commonly used as a fail-through for headless, non-802.1X capable and legacy devices as well as guest users. MAB is often combined with 802.1X and Captive Portal as part of a colorless port configuration supporting every user and device type with a single port configuration.
Aruba ClearPass is a multi-vendor product that leverages standards-based protocols and technologies along with the flexibility to support vendor-specific switch features for policy enforcement.
Radius IETF Attribute Egress-VLANID is used for vlans with tag functionality. Any standards based Radius server can send multiple tagged vlans using radius attribute Egress-VLANID or Egress-VLAN-Name for tagged packets as per RFC 4675.
The Egress-VLANID or Egress-VLAN-Name attribute contains two parts; the first part indicates if frames on the VLAN for this port are to be represented in tagged or untagged format, the second part is the VLAN name. For Example:
Egress-VLANID = 0x3100012D, here 0x31 represents tagged.
Egress-VLANID = 0x3200012D, here 0x32 represents untagged.
Egress-VLAN-Name is similar to the Egress-VLANID attribute, except that the VLAN-ID itself is not specified or known; rather, the VLAN name is used to identify the VLAN within the system.
Examples:
For attribute Egress-VLANID:
001094001177 Cleartext-Password := "001094001177“ Tunnel-Type = VLAN, Tunnel-Medium-Type = IEEE-802, Egress-VLANID += 0x3100033, <<= Here 0x31 for tagged vlan Egress-VLANID += 0x3200034, <<= Here 0x32 for untagged vlanFor attribute Egress-VLAN-Name:
001094001144 Cleartext-Password := "001094001144“ Tunnel-Type = VLAN, Tunnel-Medium-Type = IEEE-802, Egress-VLAN-Name += 1vlan-2, <<= Here 1 for tagged vlan Egress-VLAN-Name += 2vlan-3, <<= Here 2 for untagged vlan Egress-VLAN-Name += 1vlan-4, Egress-VLAN-Name += 1vlan-5,For sample radius profile:
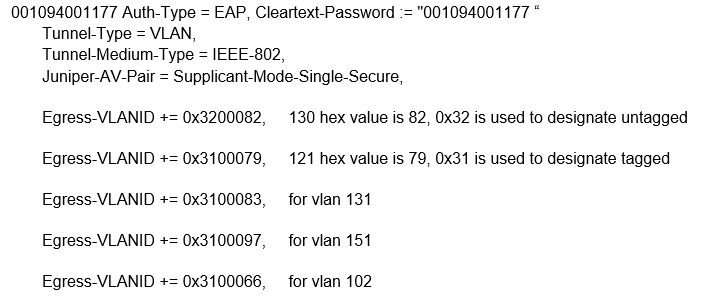
001094001177 Auth-Type = EAP, Cleartext-Password := "001094001177 “ Tunnel-Type = VLAN, Tunnel-Medium-Type = IEEE-802, Juniper-AV-Pair = Supplicant-Mode-Single-Secure, Egress-VLANID += 0x3100065, Egress-VLANID += 0x3100066
With Junos OS Release 20.3R1, we have added new VSA Supplicant-Mode-Single or Supplicant-Mode-Single-secure with attribute Juniper-AV-Pair. Which will be used to set the supplicant mode of dot1x.
Requirements
This example uses the following hardware and software components for the policy infrastructure:
EX4300, EX2300, EX3400 switch running Junos OS Release 20.4R1 or earlier
Aruba ClearPass Policy Manager running 6.9.0.130064
Overview and Topology
VLAN name is highly recommended in a colorless port deployment as it removes the need for radius server to maintain a VLAN to function mapping for each switch. This simplifies policy creation, management and troubleshooting.
For example, each switch might use a different VLAN-ID for “secure access”. Instead of having to write complex policy in radius to return the correct VLAN-ID for each switch, we just give the appropriate VLAN-ID a name on each switch; “SECURE” for example. Now in your radius server, you simply return a VLAN enforcement with “SECURE” as the VLAN-ID and each switch will use the appropriate VLAN-ID mapped locally on the switch.
In ClearPass 6.6.X and earlier, the pre-defined Juniper dynamic authorization enforcement profiles need to be used with Juniper switches.
Figure 1 shows the topology used in this example.

Here is the sample profile in a radius server to convert the port once device profiling is enabled and we detect a MIST AP to a trunk port with VLAN 130 as native VLAN and allow the rest of the VLAN’s (121,131,151,102).
Procedure
Step-by-Step Procedure
To configure colorless ports on EX Series switches with Aruba ClearPass policy manager and Cisco ISE, follow the below steps:
-
Example of an Enforcement Profile in Aruba ClearPass / ISE—When using the Egress-VLANID attribute, ClearPass requires a decimal value to be entered for the Egress-VLANID value, so you must convert your desired hexadecimal values into decimal values. For example, see entry 4 in the Enforcement Profiles, for VLAN 130 to be untagged. The hexadecimal value for this is 0x3200082. Converting the hexadecimal value to decimal gives 52428930.
Note:To quickly convert hexadecimal value to decimal value, use the conversion application tool that is available on websites.
Figure 2: Enforcement Profiles
If the switchport is configured for Supplicant Mode Multiple, you must also return the Juniper-AV-Pair of Supplicant-Mode-Single or Supplicant-Mode-Single-Secure in your RADIUS response. The Egress-VLANID and Egress-VLAN-NAME attributes are not able to be used with the supplicant mode of Multiple.
-
In the Enforcement Profiles - Egress-VLAN-NAME you can see how to use the Egress-VLAN-NAME attribute instead of the Egress-VLANID attribute.
Figure 3: Enforcement Profiles - Egress-VLAN-NAME Note:
Note:You must assign 1 to the VLAN Name to indicate tagged or 2 to indicate untagged. The values are case sensitive.
-
Example for Cisco ISE
Figure 4: Cisco ISE Figure 5: Aruba ClearPass Profiling
Figure 5: Aruba ClearPass Profiling Figure 6: Configuring VLANs and Port
Figure 6: Configuring VLANs and Port
Verification
- Verification on the switch port
- Verification of the VLANs created on the switch port
- Ethernet Switching for Egress VLAN
Verification on the switch port
Purpose
To verify the configuration on the switch port, use
the show dot1x interface ge-0/0/6 detail command.
Action
root@EX2300-1> show dot1x interface ge-0/0/6 detail
ge-0/0/6.0
Role: Authenticator
Administrative state: Auto
Supplicant mode: Single
Number of retries: 3
Quiet period: 60 seconds
Transmit period: 30 seconds
Mac Radius: Disabled
Mac Radius Restrict: Disabled
Reauthentication: Enabled
Reauthentication interval: 3600 seconds
Supplicant timeout: 30 seconds
Server timeout: 30 seconds
Maximum EAPOL requests: 2
Guest VLAN member: not configured
Number of connected supplicants: 1
Supplicant: sujitghosh, AC:87:A3:12:E3:A8
Operational state: Authenticated
Backend Authentication state: Idle
Authentication method: Radius
Authenticated VLAN: __dynamic_vlan-0130__
Session Reauth interval: 3600 seconds
Reauthentication due in 3593 seconds
Egress Vlan: 102, 121, 130, 131, 151
Eapol-Block: Not In Effect
Domain: Data
Verification of the VLANs created on the switch port
Purpose
To verify the VLANs created on the switch port, use
the show vlans command.
Action
root@EX2300-1> show vlans
Routing instance VLAN name Tag Interfaces
default-switch __dynamic_vlan-0102__ 102
ae0.0*
ge-0/0/6.0*
default-switch __dynamic_vlan-0121__ 121
ae0.0*
ge-0/0/6.0*
default-switch __dynamic_vlan-0130__ 130
ae0.0*
ge-0/0/6.0*
default-switch __dynamic_vlan-0131__ 131
ae0.0*
ge-0/0/6.0*
default-switch __dynamic_vlan-0151__ 151
ae0.0*
ge-0/0/6.0*
default-switch default 1
ae0.0*
ge-0/0/0.0
ge-0/0/1.0*
ge-0/0/11.0
ge-0/0/2.0*
ge-0/0/3.0
ge-0/0/8.0
default-switch vlan10 10
ae0.0*
ge-0/0/4.0
default-switch vlan11 11
ae0.0*
ge-0/0/4.0
default-switch vlan12 12
ae0.0*
ge-0/0/4.0
default-switch vlan20 20
ae0.0*
ge-0/0/5.0
default-switch vlan30 30
ae0.0*
ge-0/0/7.0
default-switch vlan40 40
ae0.0*
Ethernet Switching for Egress VLAN
Purpose
To verify the ethernet-switching table for Egress
vlan list, use the show ethernet-switching interface ge-0/0/6.0 command.
Action
root@EX2300-1> show ethernet-switching interface ge-0/0/6.0
Routing Instance Name : default-switch
Logical Interface flags (DL - disable learning, AD - packet action drop,
LH - MAC limit hit, DN - interface down,
MMAS - Mac-move action shutdown, AS - Autostate-exclude enabled,
SCTL - shutdown by Storm-control, MI - MAC+IP limit hit)
Logical Vlan TAG MAC MAC+IP STP Logical Tagging
interface members limit limit state interface flags
ge-0/0/6.0 16384 0 tagged,untagged
__dynamic_vlan-0130__ 130 16384 0 Forwarding untagged
__dynamic_vlan-0102__ 102 16384 0 Forwarding tagged
__dynamic_vlan-0121__ 121 16384 0 Forwarding tagged
__dynamic_vlan-0131__ 131 16384 0 Forwarding tagged
__dynamic_vlan-0151__ 151 16384 0 Forwarding tagged
