Integrating ForeScout CounterACT with Juniper Networks Connected Security
This topic provides instructions on how to integrate the third-party device ForeScout CounterACT with Juniper Networks Connected Security solution to remediate threats from infected hosts for enterprises. ForeScout CounterACT is an agentless security appliance that dynamically identifies and evaluates network endpoints and applications the instant they connect to your network. CounterACT applies an agentless approach and integrates with Juniper Connected Security to block or quarantine infected hosts on Juniper Networks’ devices, third-party switches, and wireless access controllers with or without 802.1x protocol integration.
To integrate ForeScout CounterACT with Juniper Connected Security, you must create a connector in Policy Enforcer that enables CounterACT to connect to your secure fabric and create policies for CounterACT. Before you configure the ForeScout CounterACT connector, you must ensure that ForeScout CounterACT is installed and running with the Open Integration Module (OIM). The ForeScout OIM consists of two plug-ins: Data Exchange (DEX) and Web API. Install both the plug-ins and ensure that they are running. You must configure these plug-ins before you create a connector in Policy Enforcer.
If you do not have ForeScout CounterACT installed in your network, obtain an evaluation copy from here.
This topic includes the following sections:
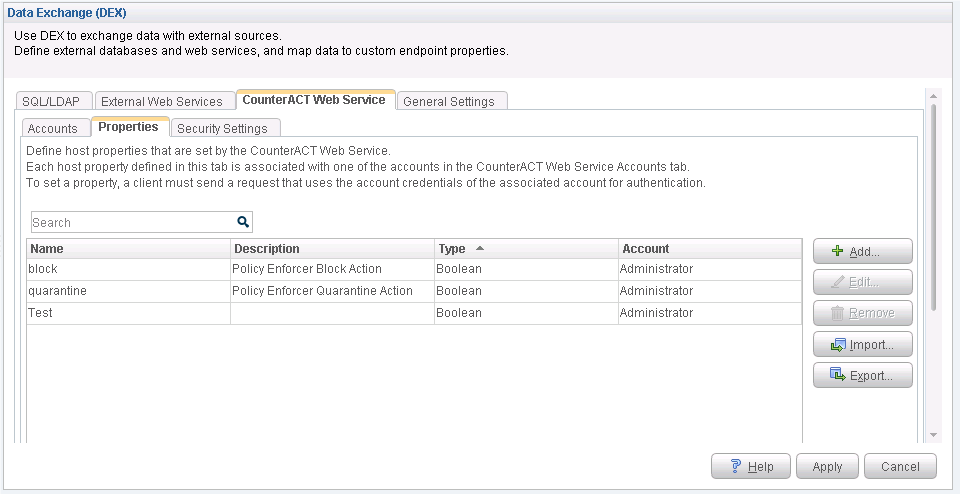
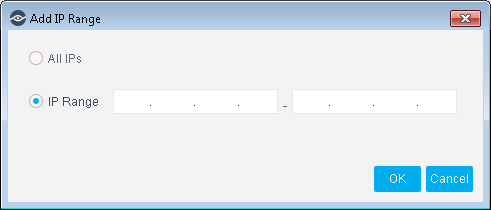
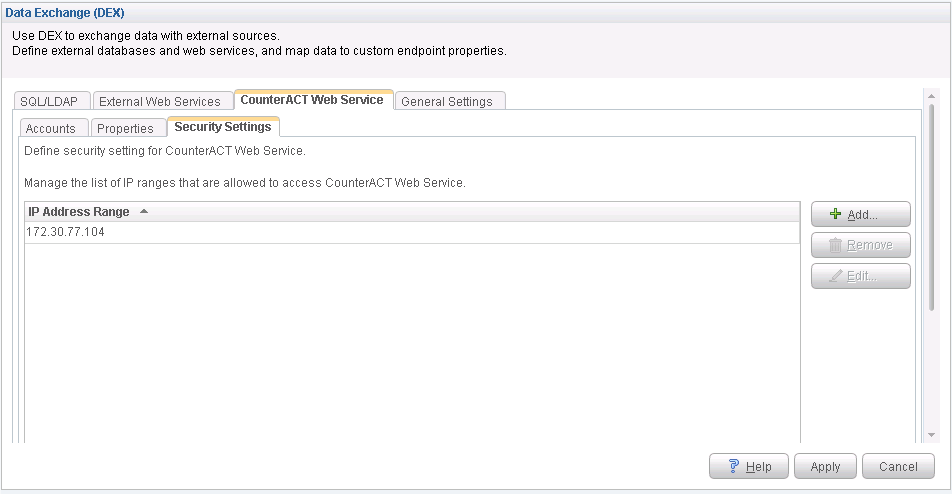
Configuring the DEX Plug-in
The DEX plug-in receives API information about infected hosts from the ForeScout CounterACT connector. Messages from infected hosts are either blocked or quarantined.
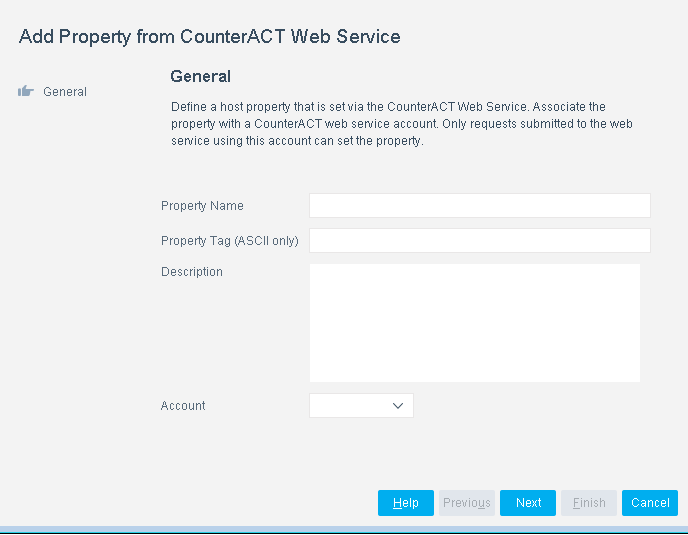
When you configure the DEX plug-in, you also configure a new property, Test, for DEX. When configured, this property ensures that Web services are available for Policy Enforcer, monitors the network status, and validates usernames and passwords.
To configure the DEX plug-in:
Configuring the Web API Plug-in
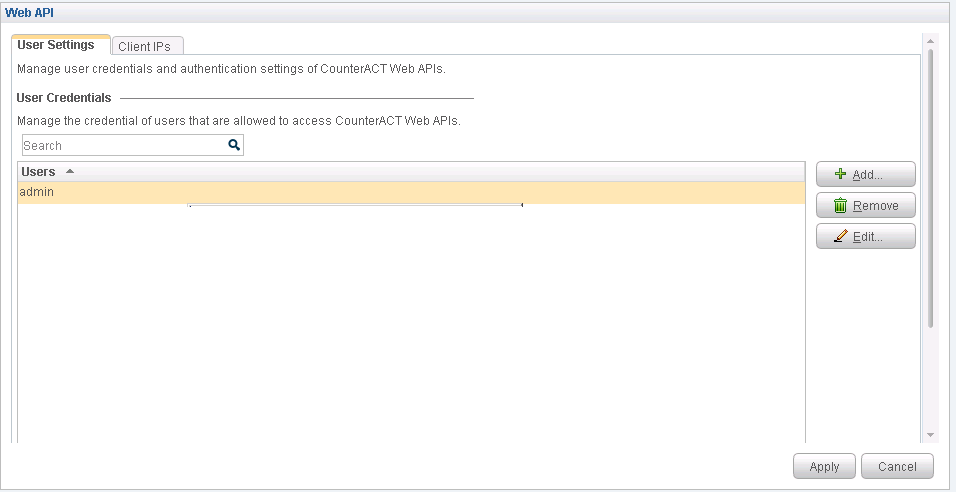
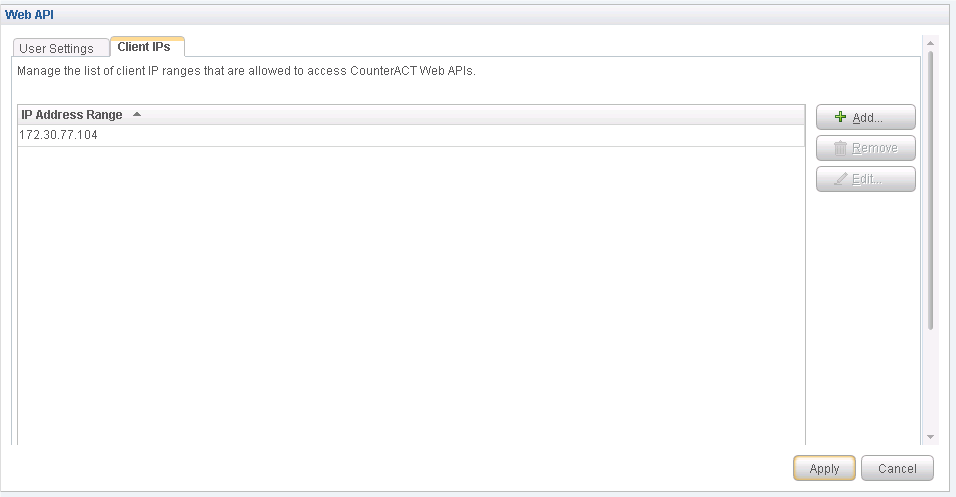
The Web API plug-in enables external entities to communicate with CounterACT by using simple, yet powerful Web service requests based on HTTP interaction. You configure the Web API plug-in to create an account for Policy Enforcer integration.
To configure the Web API plug-in:
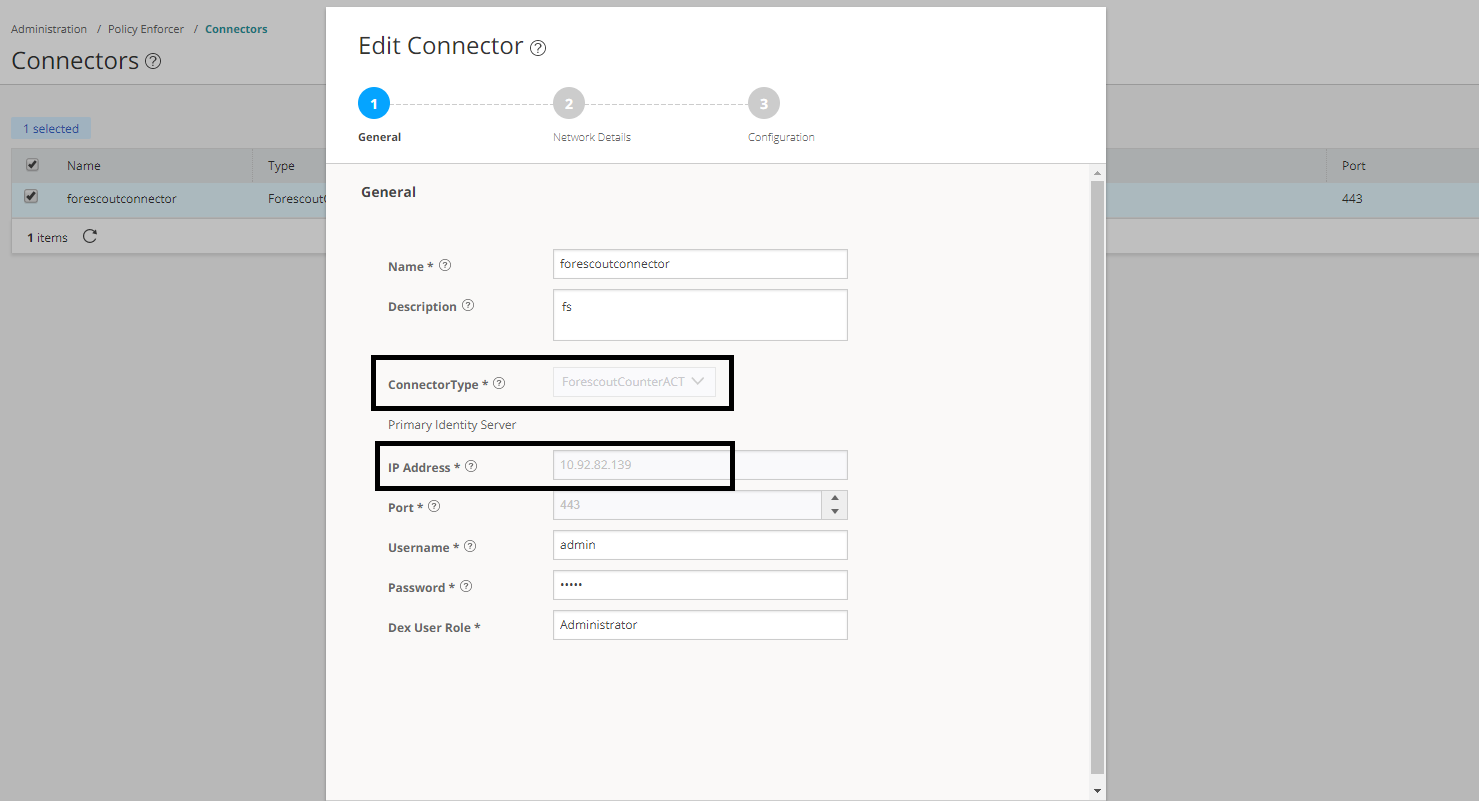
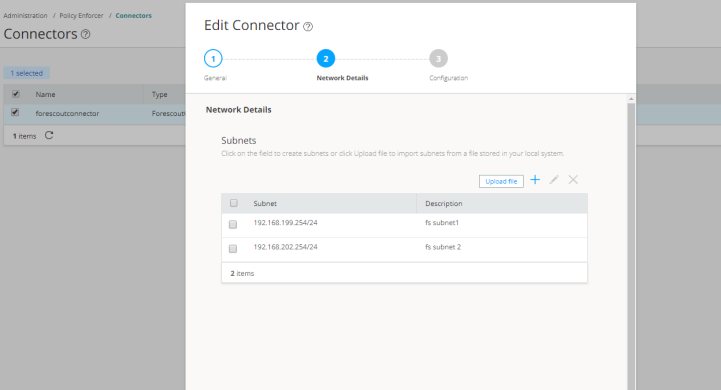
Creating ForeScout CounterACT Connector in Security Director
After you configure the DEX and Web API plug-ins, you need to create a connector for ForeScout CounterACT in Policy Enforcer.
To create a ForeScout CounterACT connector in Junos Space Security Director:
After installing ForeScout CounterACT and configuring a connector, in the CounterACT UI, create policies for CounterACT to take the necessary action on the infected hosts. The Hosts page lists compromised hosts and their associated threat levels, as shown in Figure 11.
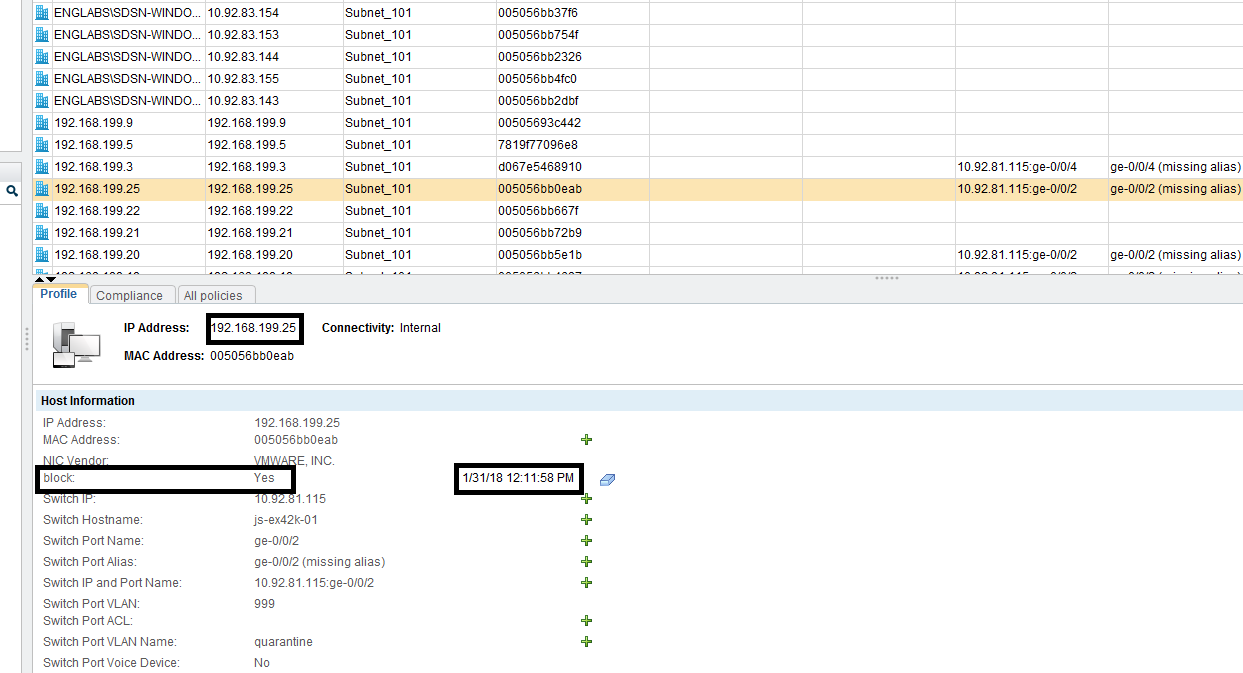
Table 1 shows the recommended actions performed by CounterACT on the infected hosts that are blocked or quarantined.
|
Infected Host Policy Enforcer Action |
Connection State |
Action Performed by CounterACT |
|---|---|---|
|
Blocked |
Wired |
Apply access control list (ACL) to block inbound and outbound traffic for a specific MAC address. |
|
Wireless |
Apply WLAN block on the endpoint, which will block the traffic based on the wireless MAC address. |
|
|
Dot1x |
Apply CoA. |
|
|
Quarantined |
Wired |
Apply VLAN. This action is specified by Policy Enforcer. |
|
Wireless |
Apply VLAN. This action is specified by Policy Enforcer. |