Benefits of Policy Enforcer
Most enterprise computer security revolves around creating a wall around the perimeter of an organization. See Figure 1.
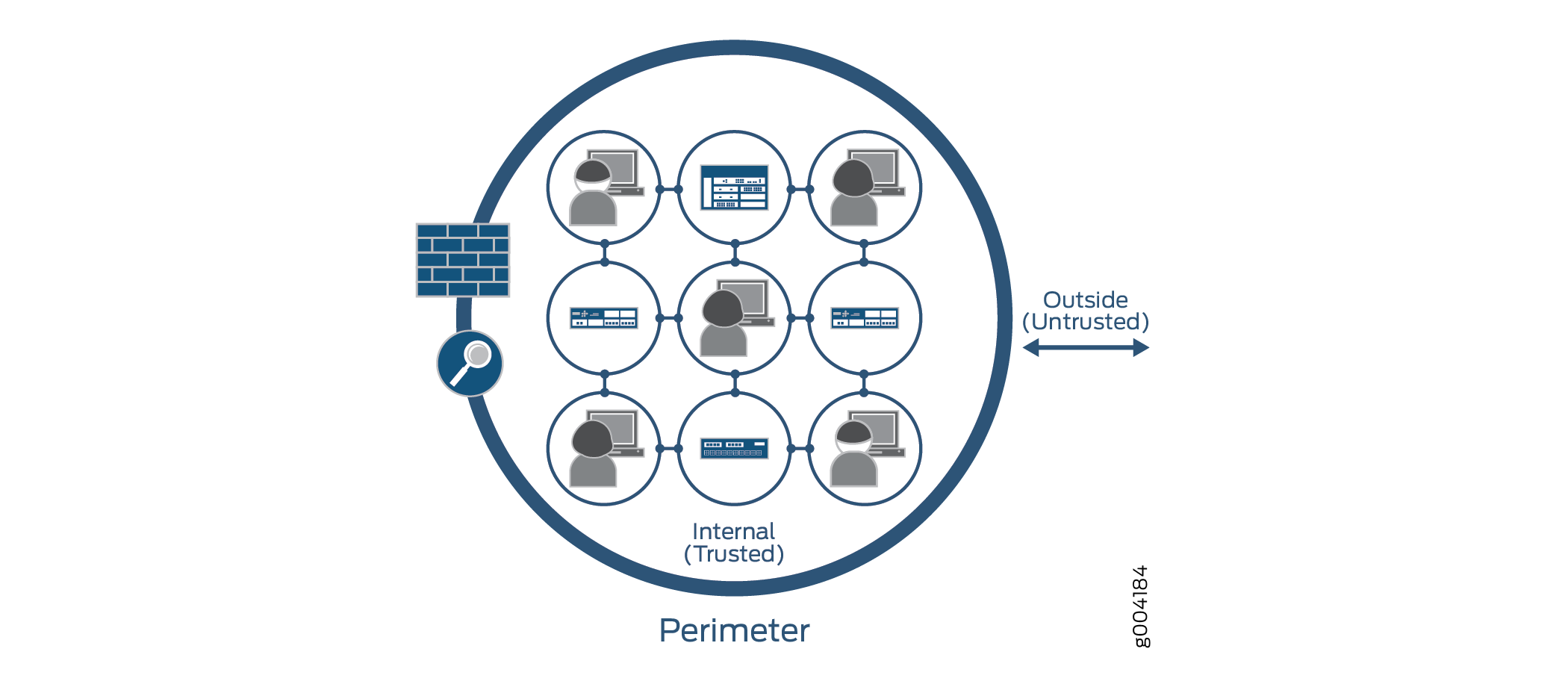
With this perimeter oriented security, networks are built with an inherently trusted model where the applications or users connecting to a network (for example, VLAN) can fundamentally talk to each other and network security solutions like firewalls and Intrusion Prevention Systems (IPS) are deployed in the perimeter to provide security. Firewalls are often configured with all possible rules in an effort to prevent unknown malware, application and network attacks from penetrating the enterprise. This architecture is based on a model where it is assumed that “Everything already inside the network is fundamentally trusted” and “Everything outside the network is untrusted” so the perimeter is the location where all security controls are deployed.
This architecture is consistent across data centers, and campus and branch configurations. Unfortunately, there are flaws to this security architecture. They don’t help in protecting against internal threats. Despite the popularity of firewalls, the sophistication of applications and malware in recent years has found a way to circumvent perimeter defenses. Once inside the enterprise, these threats can easily spread; where someone’s infected laptop or desktop could make Enterprise networks a botnet army and become a source of internal and external attacks. Enterprises can protect against internal threats by deploying multiple layers of firewalls, but that requires careful planning since it is difficult to take all internal traffic through a separate layer of firewalls.
The security framework become a highly fragmented approach due to multiple administrators, management systems and reliance on a lot of manual coordination among different administrators and systems:
-
There is a network security team that manages security policies on perimeter firewalls primarily to manage external threats.
-
There is a network operations team, that typically manages security policies by using network and application isolation to protect against internal attacks and unauthorized access.
-
Then there is third team, an IT team, that manages end-points such as laptops, desktops and application servers to make sure that they have the correct security posture.
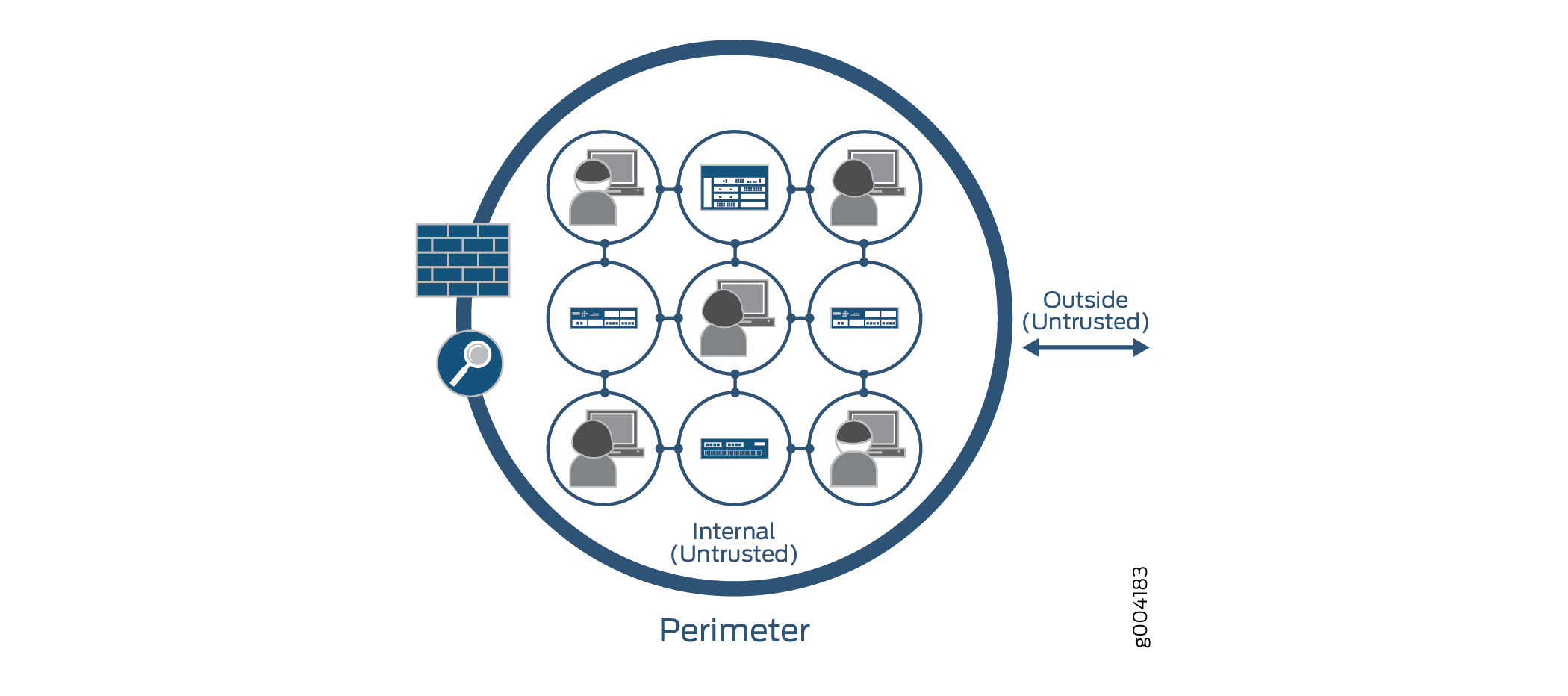
In contrast, Policy Enforcer and Juniper Connected Security, see Figure 2, simplifies network security by providing protection based on logical policies and not security devices. Policy Enforcer does provide perimeter security, but it’s no longer just protecting the inside from the outside. The fact that somebody is connected to the internal network does not mean that they can get unrestricted access to the network. This model is fundamentally more secure because even if one application on the network is compromised, companies can limit the spread of that infection/threat to other potentially more critical assets inside the network.
Policy Enforcer is a model where the information security is controlled and managed by security software. New devices are automatically covered by security policies, instead of having to identify it’s IP address as with other models. Because it’s software-defined, environments can be moved without affecting security policies and controls already in place. Other advantages include:
-
Better and more detailed security—By providing better visibility into network activity, you can respond faster to cyber threats and other security incidents. Threats can be detected faster by leveraging threat intelligence from multiple sources (including third-party feeds) and the cloud. A central control lets you analyze security challenges without interfering with standard network activity and to distribute security policies throughout your organization. For example, you can selectively block malicious traffic while allowing normal traffic flow.
-
Scalability and cost savings—A software-based model allows you to quickly and easily scale security up or down based on your immediate needs all without having to add or subtract hardware that is expensive to buy and maintain.
-
Simpler solution—Hardware security architectures can be complex due to the servers and specialized physical devices that are required. In a software model, security is based on policies. Information can be protected anywhere it resides without depending on its physical location.
