Inter-Chassis High Availability for MS-MIC and MS-MPC (Release 15.1 and earlier)
This topic applies to Junos OS release 15.1 and earlier. (For Junos OS release 16.1 and higher, see Inter-Chassis Stateful Synchronization for Long Lived NAT and Stateful Firewall Flows (MS-MPC, MS-MIC) Overview (Release 16.1 and later).)
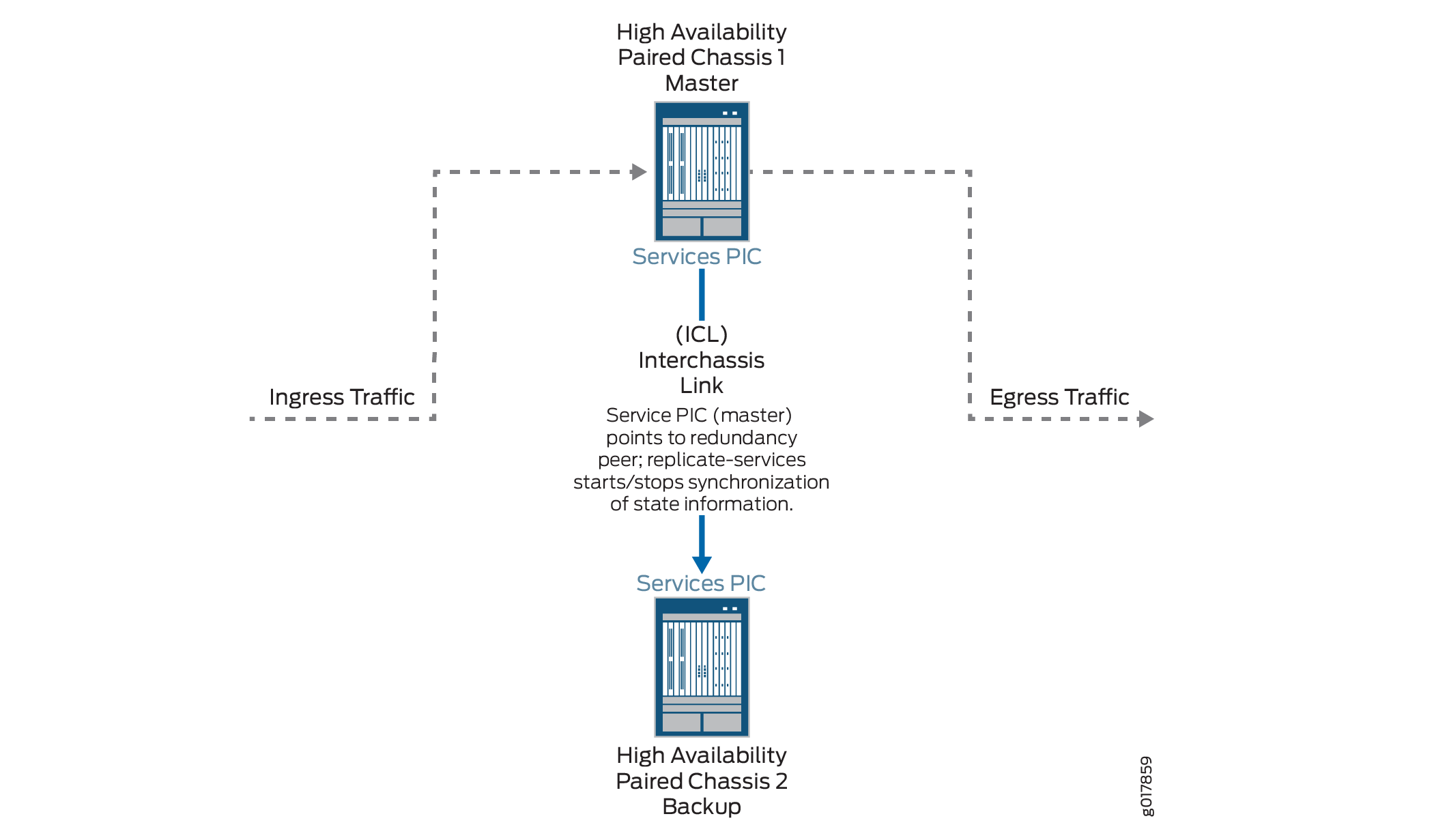
Inter-chassis high availability supports stateful synchronization of services using a switchover to a backup services PIC on a different chassis. This topic applies to Junos OS release 15.1 and earlier. (For Junos OS release 16.1 and higher, see Inter-Chassis Stateful Synchronization for Long Lived NAT and Stateful Firewall Flows (MS-MPC, MS-MIC) Overview (Release 16.1 and later).) The feature is described in the following topics:
Inter-Chassis High Availability for Stateful Firewall and NAPT44 Overview (MS-MIC, MS-MPC)
Carrier-grade NAT (CGN) deployments can use dual-chassis implementations
to provide a redundant data path and redundancy for key components
in the router. Although intra-chassis high availability can be used
in dual-chassis environments, it deals only with service PIC failures.
If traffic is switched to a backup router due to some other failure
in the router, state is lost. Inter-chassis high availability preserves
state and provides redundancy using fewer service PICs than intra-chassis
high availability. Only long-lived flows are synchronized between
the primary and backup chassis in the high availability pair. The
service PICs do not replicate state until an explicit CLI command, request services redundancy (synchronize | no-synchronize),
is issued to start or stop the state replication. Stateful firewall,
NAPT44, and APP state information can be synchronized.
When both the primary and backup PICs are up, replication
starts immediately when the request services redundancy command is issued.
In order to use Inter-chassis high availability, you must use
service sets configured for next-hop service interfaces. Inter-chassis
high availability works with ms- service interfaces configured on
MS-MIC or MS-MPC interface cards. A unit other than unit 0 must be
configured with the ip-address-owner service-plane option.
The following restrictions apply:
NAPT44 is the only translation type supported.
Checkpointing is not supported for ALGs, PBA port block allocation (PBA), endpoint- independent mapping (EIM), or endpoint- independent filters (EIF).
Figure 1 shows the inter-chassis high availability topology.
Configuring Inter-Chassis High Availability for Stateful Firewall and NAPT44 (MS-MPC, MS-MIC)
To configure inter-chassis availability for stateful firewall and NAPT44 on MS-MIC or MS-MPC service PICS, perform the following configuration steps on each chassis of the high availability pair:
Example: Inter-Chassis Stateful High Availability for NAT and Stateful Firewall (MS-MIC, MS-MPC)
This example shows how to configure inter-chassis high availability for stateful firewall and NAT services.
Requirements
This example uses the following hardware and software components:
Two MX480 routers with MS-MPC line cards
Junos OS Release 13.3 or later
Overview
Two MX 3D routers are identically configured to facilitate stateful failover for firewall and NAT services in case of a chassis failure.
Configuration
To configure inter-chassis high availability for this example, perform these tasks:
- CLI Quick Configuration
- Configuring Interfaces for Chassis 1.
- Configure Routing Information for Chassis 1
- Configuring NAT and Stateful Firewall for Chassis 1
- Configuring the Service Set
- Configuring Interfaces for Chassis 2
- Configure Routing Information for Chassis 2
CLI Quick Configuration
To quickly configure this example on the routers, copy the following commands and paste them into the router terminal window after removing line breaks and substituting interface information specific to your site.
The following configuration is for chassis 1.
[edit] set interfaces ms-4/0/0 redundancy-options redundancy-peer ipaddress 5.5.5.2 set interfaces ms-4/0/0 redundancy-options routing-instance HA set interfaces ms-4/0/0 unit 10 ip-address-owner service-plane set interfaces ms-4/0/0 unit 10 family inet address 5.5.5.1/32 set interfaces ms-4/0/0 unit 20 family inet set interfaces ms-4/0/0 unit 20 service-domain inside set interfaces ms-4/0/0 unit 30 family inet set interfaces ms-4/0/0 unit 30 service-domain outside set interfaces ge-2/0/0 vlan-tagging set interfaces ge-2/0/0 unit 0 vlan-id 100 family inet address 20.1.1.1/24 set routing-instances HA instance-type vrf set routing-instances HA interface ge-2/0/0.0 set routing-instances HA interface ms-4/0/0.10 set routing-instances HA route-distinguisher 1:1 set policy-options policy-statement dummy term 1 then reject set routing-instances HA vrf-import dummy set routing-instances HA vrf-export dummy set routing-instances HA routing-options static route route 5.5.5.1/32 next-hop ms-4/0/0.10 set routing-instances HA routing-options static route route 5.5.5.2/32 next-hop 20.1.1.2 set services nat pool p2 address 32.0.0.0/24 set services nat pool p2 port automatic random-allocation set services nat pool p2 address-allocation round-robin set services nat rule r2 match-direction input set services nat rule r2 term t1 from source-address 129.0.0.0/8 set services nat rule r2 term t1 from source-address 128.0.0.0/8 set services nat rule r2 term t1 then translated source-pool p2 set services nat rule r2 term t1 then translated translation-type napt-44 set services nat rule r2 term t1 then translated address-pooling paired set services nat rule r2 term t1 then syslog set services stateful-firewall rule r2 match-direction input set services stateful-firewall rule r2 term t1 from source-address any-unicast set services stateful-firewall rule r2 term t1 then accept set services stateful-firewall rule r2 term t1 then syslog set services service-set ss2 replicate-services replication-threshold 180 set services service-set ss2 replicate-services stateful-firewall set services service-set ss2 replicate-services nat set services service-set ss2 stateful-firewall-rules r2 set services service-set ss2 nat-rules r2 set services service-set ss2 next-hop-service inside-service-interface ms-4/0/0.20 set services service-set ss2 next-hop-service outside-service-interface ms-4/0/0.30 set services service-set ss2 syslog host local class session-logs set services service-set ss2 syslog host local class stateful-firewall-logs set services service-set ss2 syslog host local class nat-logs
The following configuration is for chassis 2. The NAT, stateful firewall, and service-set information must be identical for chassis 1 and 2.
set interfaces ms-4/0/0 redundancy-options routing-instance HA set interfaces ms-4/0/0 unit 10 ip-address-owner service-plane set interfaces ms-4/0/0 unit 10 family inet address 5.5.5.2/32 set interfaces ms-4/0/0 unit 20 family inet set interfaces ms-4/0/0 unit 20 service-domain inside set interfaces ms-4/0/0 unit 30 family inet set interfaces ms-4/0/0 unit 30 service-domain outside set interfaces ge-2/0/0 vlan-tagging set interfaces ge-2/0/0 unit 0 vlan-id 100 family inet address 20.1.1.2/24 set routing-instances HA instance-type vrf set routing-instances HA interface ge-2/0/0.0 set routing-instances HA interface ms-4/0/0.10 set routing-instances HA route-distinguisher 1:1 set routing-instances HA vrf-import dummy set routing-instances HA vrf-export dummy set routing-instances HA routing-options static route 5.5.5.2/32 next-hop ms-4/0/0.10 set routing-instances HA routing-options static route 5.5.5.1/32 next-hop 20.1.1.1 set services nat pool p2 address 32.0.0.0/24 set services nat pool p2 port automatic random-allocation set services nat pool p2 address-allocation round-robin set services nat rule r2 match-direction input set services nat rule r2 term t1 from source-address 129.0.0.0/8 set services nat rule r2 term t1 from source-address 128.0.0.0/8 set services nat rule r2 term t1 then translated source-pool p2 set services nat rule r2 term t1 then translated translation-type napt-44 set services nat rule r2 term t1 then translated address-pooling paired set services nat rule r2 term t1 then syslog set services stateful-firewall rule r2 match-direction input set services stateful-firewall rule r2 term t1 from source-address any-unicast set services stateful-firewall rule r2 term t1 then accept set services stateful-firewall rule r2 term t1 then syslog set services service-set ss2 replicate-services replication-threshold 180 set services service-set ss2 replicate-services stateful-firewall set services service-set ss2 replicate-services nat set services service-set ss2 stateful-firewall-rules r2 set services service-set ss2 nat-rules r2 set services service-set ss2 next-hop-service inside-service-interface ms-4/0/0.20 set services service-set ss2 next-hop-service outside-service-interface ms-4/0/0.30 set services service-set ss2 syslog host local class session-logs set services service-set ss2 syslog host local class stateful-firewall-logs set services service-set ss2 syslog host local class nat-logs
Configuring Interfaces for Chassis 1.
Step-by-Step Procedure
The interfaces for each of the HA pair of routers are configured identically with the exception of the following service PIC options:
redundancy-options redundancy-peer ipaddress addressunit unit-number family inet address addressof a unit, other than 0, that contains theip-address-owner service-planeoption
To configure interfaces:
Configure the redundant service PIC on chassis 1.
[edit interfaces} user@host# set interfaces ms-4/0/0 redundancy-options redundancy-peer ipaddress 5.5.5.2 user@host# set interfaces ms-4/0/0 redundancy-options routing-instance HA user@host# set interfaces ms-4/0/0 unit 10 ip-address-owner service-plane user@host# set interfaces ms-4/0/0 unit 10 family inet address 5.5.5.1/32 user@host# set interfaces ms-4/0/0 unit 20 family inet user@host# set interfaces ms-4/0/0 unit 20 service-domain inside user@host# set interfaces ms-4/0/0 unit 30 family inet user@host# set interfaces ms-4/0/0 unit 30 service-domain outside
Configure the interfaces for chassis 1 that are used as interchassis links for synchronization traffic.
user@host# set interfaces ge-2/0/0 vlan-tagging user@host# set interfaces ge-2/0/0 unit 0 vlan-id 100 family inet address 20.1.1.1/24
Configure remaining interfaces as needed.
Results
user@host# show interfaces
ge-2/0/0 {
vlan-tagging;
unit 0 {
vlan-id 100;
family inet {
address 20.1.1.1/24;
}
}
}
ms-4/0/0 {
redundancy-options {
redundancy-peer {
ipaddress 5.5.5.2;
}
routing-instance HA;
}
unit 10 {
ip-address-owner service-plane;
family inet {
address 5.5.5.1/32;
}
}
unit 20 {
family inet;
family inet6;
service-domain inside;
}
unit 30 {
family inet;
family inet6;
service-domain outside;
}
}
}
Configure Routing Information for Chassis 1
Step-by-Step Procedure
Detailed routing configuration is not included for this example. A routing instance is required for the HA synchronization traffic between the chassis as follows:
Configure routing instances for Chassis 1.
user@host# set routing-instances HA instance-type vrf user@host# set routing-instances HA interface ge-2/0/0.0 user@host# set routing-instances HA interface ms-4/0/0.10 user@host# set routing-instances HA route-distinguisher 1:1 user@host# set policy-options policy-statement dummy term 1 then reject user@host# set routing-instances HA vrf-import dummy user@host# set routing-instances HA vrf-export dummy user@host# set routing-instances HA routing-options static route route 5.5.5.1/32 next-hop ms-4/0/0.10 user@host# set routing-instances HA routing-options static route route 5.5.5.2/32 next-hop 20.1.1.2
Results
user@host# show routing-instances
HA {
instance-type vrf;
interface ge-2/0/0.0;
interface ms-4/0/0.10;
route-distinguisher 1:1;
vrf-import dummy;
vrf-export dummy;
routing-options {
static {
route 5.5.5.1/32 next-hop ms-4/0/0.10;
route 5.5.5.2/32 next-hop 20.1.1.2;
}
}
}
Configuring NAT and Stateful Firewall for Chassis 1
Step-by-Step Procedure
Configure NAT and stateful firewall identically on both routers. To configure NAT and stateful firewall:
Configure NAT as needed.
user@host# set services nat pool p2 address 32.0.0.0/24 user@host# set services nat pool p2 port automatic random-allocation user@host# set services nat pool p2 address-allocation round-robin user@host# set services nat rule r2 match-direction input user@host# set services nat rule r2 term t1 from source-address 129.0.0.0/8 user@host# set services nat rule r2 term t1 from source-address 128.0.0.0/8 user@host# set services nat rule r2 term t1 then translated source-pool p2 user@host# set services nat rule r2 term t1 then translated translation-type napt-44 user@host# set services nat rule r2 term t1 then translated address-pooling paired user@host# set services nat rule r2 term t1 then syslog
Configure stateful firewall as needed.
user@host# set services stateful-firewall rule r2 match-direction input user@host# set services stateful-firewall rule r2 term t1 from source-address any-unicast user@host# set services stateful-firewall rule r2 term t1 then accept user@host# set services stateful-firewall rule r2 term t1 then syslog
Results
user@host# show services nat
nat {
pool p2 {
address 32.0.0.0/24;
port {
automatic {
random-allocation;
}
}
address-allocation round-robin;
}
rule r2 {
match-direction input;
term t1 {
from {
source-address {
129.0.0.0/8;
128.0.0.0/8;
}
}
then {
translated {
source-pool p2;
translation-type {
napt-44;
}
address-pooling paired;
}
syslog;
}
}
}
}
}
user@host show services stateful-firewell
rule r2 {
match-direction input;
term t1 {
from {
source-address {
any-unicast;
}
}
then {
accept;
syslog;
}
}
}
Configuring the Service Set
Step-by-Step Procedure
Configure the the service set identically on both routers. To configure the service set:
Configure the service set replication options.
user@host# set services service-set ss2 replicate-services replication-threshold 180 user@host# set services service-set ss2 replicate-services stateful-firewall user@host# set services service-set ss2 replicate-services nat
Configure references to NAT and stateful firewall rules for the service set.
user@host# set services service-set ss2 stateful-firewall-rules r2 user@host# set services service-set ss2 nat-rules r2
Configure next-hop service interface on the MS-PIC.
user@host# set services service-set ss2 next-hop-service inside-service-interface ms-4/0/0.20 user@host# set services service-set ss2 next-hop-service outside-service-interface ms-4/0/0.30
Configure desired logging options.
user@host# set services service-set ss2 syslog host local class session-logs user@host# set services service-set ss2 syslog host local class stateful-firewall-logs user@host# set services service-set ss2 syslog host local class nat-logs
Results
user@host# show services service-set ss2
syslog {
host local {
class {
session-logs;
inactive: stateful-firewall-logs;
nat-logs;
}
}
}
replicate-services {
replication-threshold 180;
stateful-firewall;
nat;
}
stateful-firewall-rules r2;
inactive: nat-rules r2;
next-hop-service {
inside-service-interface ms-3/0/0.20;
outside-service-interface ms-3/0/0.30;
}
}
Configuring Interfaces for Chassis 2
Step-by-Step Procedure
The interfaces for each of the HA pair of routers are configured identically with the exception of the following service PIC options:
redundancy-options redundancy-peer ipaddress addressunit unit-number family inet address addressof a unit, other than 0, that contains theip-address-owner service-planeoption
Configure the redundant service PIC on chassis 2.
The
redundancy-peer ipaddresspoints to the address of the unit (unit 10) on ms-4/0/0 on chassis on chassis 1 that contains theip-address-owner service-planestatement.[edit interfaces} set interfaces ms-4/0/0 redundancy-options redundancy-peer ipaddress 5.5.5.1 user@host# set interfaces ms-4/0/0 redundancy-options routing-instance HA user@host# set interfaces ms-4/0/0 unit 10 ip-address-owner service-plane user@host# set interfaces ms-4/0/0 unit 10 family inet address 5.5.5.2/32 user@host# set interfaces ms-4/0/0 unit 20 family inet user@host# set interfaces ms-4/0/0 unit 20 service-domain inside user@host# set interfaces ms-4/0/0 unit 30 family inet user@host# set interfaces ms-4/0/0 unit 30 service-domain outside
Configure the interfaces for chassis 2 that are used as interchassis links for synchronization traffic
user@host# set interfaces ge-2/0/0 vlan-tagging user@host# set interfaces ge-2/0/0 unit 0 vlan-id 100 family inet address 20.1.1.2/24
Configure remaining interfaces for chassis 2 as needed.
Results
user@host# show interfaces
ms-4/0/0 {
redundancy-options {
redundancy-peer {
ipaddress 5.5.5.1;
}
routing-instance HA;
}
unit 0 {
family inet;
}
unit 10 {
ip-address-owner service-plane;
family inet {
address 5.5.5.2/32;
}
}
ge-2/0/0 {
vlan-tagging;
unit 0 {
vlan-id 100;
family inet {
address 20.1.1.2/24;
}
}
unit 10 {
vlan-id 10;
family inet {
address 2.10.1.2/24;
}
Configure Routing Information for Chassis 2
Step-by-Step Procedure
Detailed routing configuration is not included for this example. A routing instance is required for the HA synchronization traffic between the two chassis and is included here.
Configure routing instances for chassis 2.
user@host# set routing-instances HA instance-type vrf user@host# set routing-instances HA interface ge-2/0/0.0 user@host# set routing-instances HA interface ms-4/0/0.10 user@host# set routing-instances HA route-distinguisher 1:1 user@host# set policy-options policy-statement dummy term 1 then reject user@host# set routing-instances HA vrf-import dummy user@host# set routing-instances HA vrf-export dummy user@host# set routing-instances HA routing-options static route 5.5.5.2/32 next-hop ms-4/0/0.10 user@host# set routing-instances HA routing-options static route 5.5.5.1/32 next-hop 20.1.1.1
Note:The following configuration steps are identical to the steps shown for chassis 1.
Configuring NAT and Stateful Firewall
Configuring the Service Set
Results
user@host# show services routing-instances
HA {
instance-type vrf;
interface xe-2/2/0.0;
interface ms-4/0/0.10;
route-distinguisher 1:1;
vrf-import dummy;
vrf-export dummy;
routing-options {
static {
route 5.5.5.2/32 next-hop ms-4/0/0.10;
route 5.5.5.1/32 next-hop 20.1.1.1;
}
}
