在本页
中心辐射型设备上的 AutoVPN
了解 AutoVPN 以及如何在 SRX 系列防火墙中对其进行配置。
AutoVPN 支持一个 IPsec VPN 聚合器(称为集线器),该聚合器充当通往远程站点的多个隧道(称为分支)的单个端点。AutoVPN 允许网络管理员为当前和未来的分支配置中心。
使用 功能资源管理器 确认平台和版本对特定功能的支持。
查看该 特定于平台的 AutoVPN 行为 部分,了解与您的平台相关的注意事项。
了解自动VPN
AutoVPN 支持一个 IPsec VPN 聚合器(称为 集线器),该聚合器充当通往远程站点的多个隧道(称为 分支)的单个端点。AutoVPN 允许网络管理员为当前和未来的分支配置中心。添加或删除分支设备时,无需在中心更改配置,从而使管理员可以灵活地管理大规模网络部署。
安全隧道模式
基于路由的 IPsec VPN 支持 AutoVPN。对于基于路由的 VPN,您可以配置安全隧道 (st0) 接口并将其绑定到 IPsec VPN 隧道。AutoVPN 网络中的 st0 接口可以配置为以下两种模式之一:
-
点对点模式 — 默认情况下,在 [
edit interfaces st0 unit x] 层次结构级别配置的 st0 接口处于点对点模式。 -
点对多点模式 - 在此模式下,
multipoint在 AutoVPN 中心和分支上的 [edit interfaces st0 unit x] 层次结构级别配置选项。 中心和分支上的 st0 接口必须编号,并且在分支上配置的 IP 地址必须存在于中心的 st0 接口子网中。
表 1 比较 AutoVPN 点对点和点对多点安全隧道接口模式。
|
点对点模式 |
点对多点模式 |
|---|---|
|
支持 IKEv1 或 IKEv2。 |
支持 IKEv1 或 IKEv2。 |
| 支持 IPv4 和 IPv6 流量。 |
支持 IPv4 或 IPv6。 |
| 流量选择器 |
动态路由协议(OSPF、OSPFv3 和 iBGP) |
| 失效对等体检测 |
失效对等体检测 |
| 允许分支设备为 SRX 系列或第三方设备。 |
此模式仅受 SRX 系列防火墙支持。 |
身份验证
AutoVPN 支持基于证书和预共享密钥的身份验证方法。
对于 AutoVPN 中心辐射中基于证书的身份验证,可以使用 X.509 公钥基础结构 (PKI) 证书。在中心配置的组 IKE 用户类型允许指定字符串以匹配分支证书中的备用使用者字段。还可以指定分支证书中主题字段的部分匹配项。请参见 了解 AutoVPN 部署中的分支身份验证。
我们通过以下两个选项支持 AutoVPN:
- AutoVPN 种子 PSK:连接到具有不同预共享密钥的同一网关的多个对等方。
- AutoVPN 共享 PSK:多个对等方连接到具有相同预共享密钥的同一网关。
种子 PSK 不同于非种子 PSK(即相同的共享 PSK)。种子 PSK 使用主密钥为对等方生成共享 PSK。因此,每个对等方都有不同的 PSK 连接到同一网关。例如:考虑这样一种情况:具有 IKE ID user1@juniper.net 的对等方 1 和具有 IKE ID user2@juniper.net 的对等方 2 尝试连接到网关。在这种情况下,配置为 HUB_GW 包含配置为 ThisIsMySecretPreSharedkey 的主密钥的网关将具有不同的 PSK,如下所示:
对等 1 : 79e4ea39f5c06834a3c4c031e37c6de24d46798a
对等 2: 3db8385746f3d1e639435a882579a9f28464e5c7
这意味着,对于具有不同用户 ID 和相同主密钥的不同用户,将生成不同或唯一的预共享密钥。
您可以将 seeded-pre-shared-key 或 用于 pre-shared-key 自动 VPN PSK:
- 不同的预共享密钥:如果设置了,
seeded-pre-shared-key则 VPN 网关使用不同的 IKE 预共享密钥对每个远程对等方进行身份验证。对等方预共享密钥使用 IKE 网关中的集生成master-key,并在对等方之间共享。要使 VPN 网关能够使用不同的 IKE 预共享密钥 (PSK) 对每个远程对等方进行身份验证,请使用新的 CLI 命令
seeded-pre-shared-key ascii-text或在seeded-pre-shared-key hexadecimal层次结构级别下。[edit security ike policy policy_name]此命令与同一层次结构下的命令互
pre-shared-key斥。请参阅 政策。
- 共享/相同预共享密钥:如果未配置,则
pre-shared-key-typePSK 被视为共享。VPN 网关使用相同的 IKE 预共享密钥对所有远程对等方进行身份验证。要使 VPN 网关能够使用相同的 IKE PSK 对所有远程对等方进行身份验证,请使用现有 CLI 命令
pre-sharedkey ascii-text或pre-shared-key hexadecimal。
在 VPN 网关上,您可以使用层次结构级别下的[edit security ike gateway gateway_name dynamic]配置语句绕过 general-ikeid IKE ID 验证。如果配置了此选项,则在对远程对等方进行身份验证期间,VPN 网关将允许任何远程 IKE ID 连接。请参阅 general-ikeid。
带有 SPC3 卡和运行 iked 进程的 vSRX 虚拟防火墙(带软件包 junos-ike )的 SRX5000 系列支持以下 IKE 模式:
|
IKE 模式 |
SRX5000 条线路,SPC3 卡和运行 iked 进程的 vSRX 虚拟防火墙 |
|
|---|---|---|
|
共享 PSK |
种子-PSK |
|
|
IKEv2 |
是 |
是 |
|
IKEv2 与任意 |
是 |
是 |
|
IKEv1 主动模式 |
是 |
是 |
|
IKEv1 主动模式,带 |
是 |
是 |
|
IKEv1 主模式 |
是 |
否 |
|
IKEv1 主模式,带任意远程 ID/ |
是 |
否 |
请参阅 示例:使用预共享密钥配置 AutoVPN。
配置和管理
AutoVPN 使用 CLI 在 SRX 系列防火墙上进行配置和管理。可以在单个 SRX 系列防火墙上配置多个 AutoVPN 集线器。配置的中心支持的最大分支数特定于 SRX 系列防火墙的型号。
使用 PIM 的组播支持
IP 组播通过复制数据包,将流量传送到多个预期接收方。您可以将多播数据用于视频流等应用程序。您的防火墙支持点对多点 (P2MP) 模式下的协议无关组播 (PIM)。您可以在防火墙的安全隧道 st0 接口上启用 PIM,该接口具有 P2MP 模式。该协议从接口配置中检测 P2MP 接口,并支持组播流量。若要了解 PIM,请参阅 PIM 概述。
图 1 说明了 P2MP 基础架构中的组播拓扑。
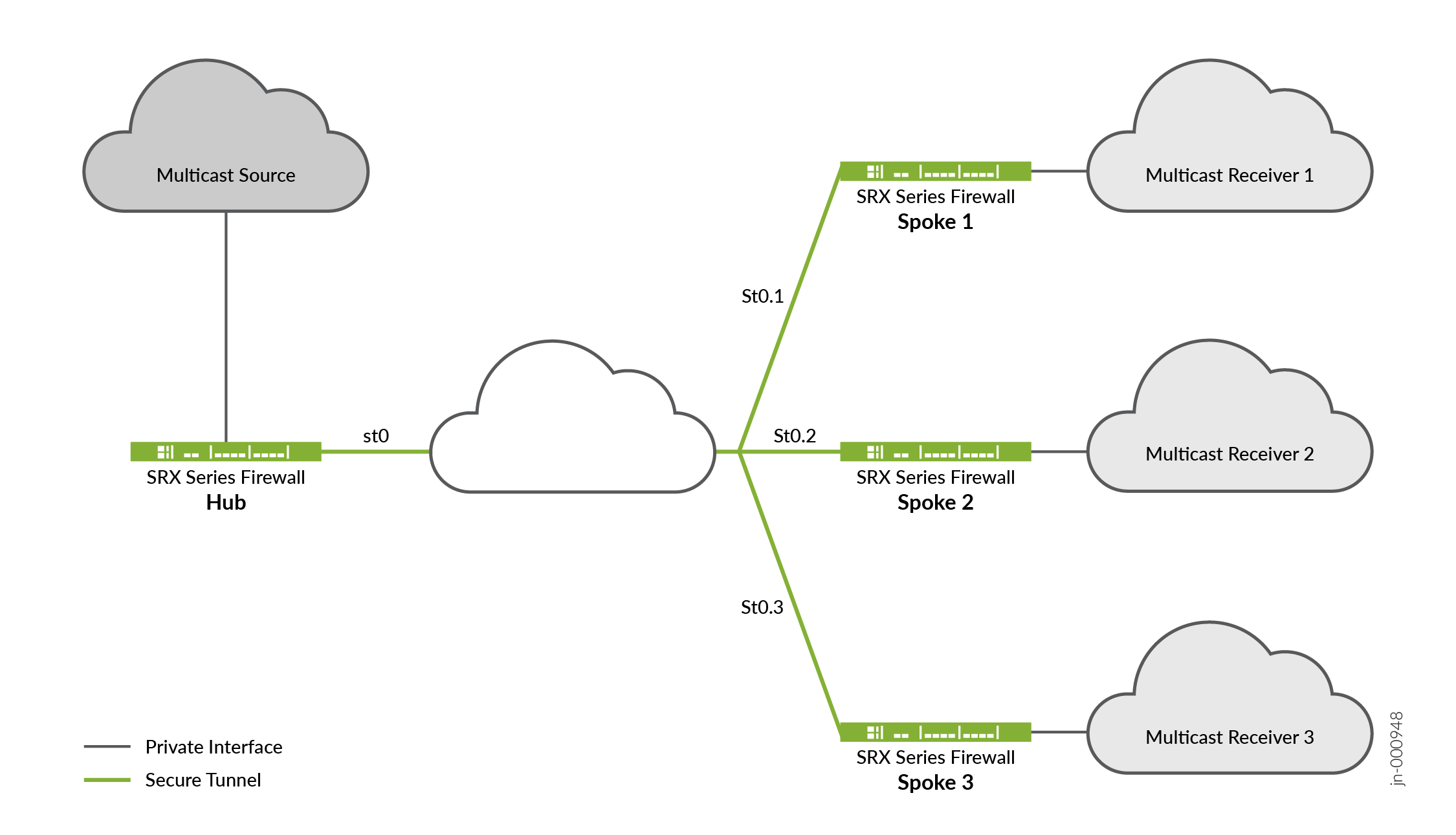
拓扑显示,其中一个 SRX 系列防火墙充当中心防火墙,其余三个防火墙充当辐射。拓扑中还可以有两个分支。通常,组播发送方位于集线器后面,而组播接收方位于分支后面。对于组播支持,请注意中心辐射型设备上的安全隧道 st0 逻辑接口配置了 PIM P2MP 模式。在上述每台设备上,st0 P2MP 接口跟踪每个邻接方的所有 PIM 联接,以确保组播转发或复制仅发生在处于联接状态的邻接方。
SRX 系列防火墙支持通过 st0 P2MP 接口以 PIM 稀疏模式进行 IP 组播流量。中枢充当第一跃点路由器 (FHR) 或集合点 (RP)。分支可以充当 P2MP 网络中的最后一跳路由器 (LHR)。网络中的设备将组播数据包复制到加入组播组的邻接方。
配置组播流量支持时,请注意以下注意事项:
-
您无法在 P2MP 接口上配置 IPv6 组播。
-
要使 IP 组播配置正常工作,必须禁用电源模式 IPsec (PMI)。
-
不能从 P2MP 接口或到 P2MP 接口执行组播 ping。
-
请注意,启用 PIM 时,IGMP 默认处于启用状态,但它在 P2MP 接口上不起作用。
有关如何在 P2MP 基础结构上配置组播支持的详细信息,请参阅 在 P2MP 基础结构上配置组播支持。
了解 AutoVPN 限制
AutoVPN 不支持以下功能:
-
不支持基于策略的 VPN。
-
AutoVPN 隧道不支持 RIP 动态路由协议。
-
不支持手动密钥和具有预共享密钥的自动密钥 IKE。
-
不支持在辐射中心配置静态下一跃点隧道绑定 (NHTB)。
-
不支持 IPv6 multicast。
-
不支持使用 IP 地址作为 IKE ID 的组 IKE ID 用户类型。
-
使用组 IKE ID 用户类型时,IKE ID 不应与在同一外部接口上配置的其他 IKE 网关重叠。
了解带有流量选择器的 AutoVPN
AutoVPN 中枢可配置多个流量选择器,以保护流向分支的流量。此功能具有以下优点:
-
单个 VPN 配置可以支持许多不同的对等方。
-
VPN 对等方可以是非 SRX 系列防火墙。
-
单个对等方可以使用同一 VPN 建立多个隧道。
-
与使用动态路由协议的 AutoVPN 相比,可以支持更多数量的隧道。
在点对点模式下使用安全隧道接口的 AutoVPN 网络为流量选择器和 IKE 对等方支持 IPv6 地址。
建立中心到分支隧道后,中心使用 自动路由插入 (ARI)(在先前版本中称为 反向路由插入 (RRI))将路由插入到其路由表中的分支前缀。然后,可以将 ARI 路由导入路由协议并分发到核心网络。
对于 IKEv1 和 IKEv2,可以在点对点模式下使用安全隧道 (st0) 接口配置带有流量选择器的 AutoVPN。
配置流量选择器时,st0 接口不支持动态路由协议。
使用流量选择器配置 AutoVPN 时,请注意以下注意事项:
-
点对点模式下具有 st0 接口的流量选择器不支持动态路由协议。
-
自动发现 VPN 和 IKEv2 配置有效负载 不能使用带有流量选择器的 AutoVPN 进行配置。
-
分支可以是非 SRX 系列防火墙;但是,请注意以下差异:
-
在 IKEv2 中,非 SRX 系列分支可以在单个 SA 协商中建议多个流量选择器。SRX 系列防火墙不支持此功能,协商将被拒绝。
-
非 SRX 系列分支可以识别流量选择器使用的特定端口或协议。SRX 系列防火墙上的流量选择器不支持端口和协议,协商将被拒绝。
-
另请参阅
了解 AutoVPN 部署中的分支身份验证
在 AutoVPN 部署中,中心辐射设备必须加载有效的 X.509 PKI 证书。您可以使用命令 show security pki local-certificate detail 显示有关设备中加载的证书的信息。
本主题介绍中心上允许分支使用证书进行身份验证并连接到中心的配置:
集线器上的组 IKE ID 配置
组 IKE ID 功能允许多个分支设备在中心共享 IKE 配置。在每个分支的 X.509 证书的主题或备用主题字段中,证书持有者的标识必须包含所有分支通用的部分;为集线器上的 IKE 配置指定证书标识的公共部分。
例如,可以在中心位置上配置 IKE ID example.net ,以使用主机名 device1.example.net、 device2.example.net和 device3.example.net标识分支。每个分支上的证书必须在备用主题字段中 example.net 包含主机名标识,该字段的最右侧部分必须包含主机名标识;例如 device1.example.net。在此示例中,所有分支在其 IKE ID 有效负载中使用此主机名标识。在 IKE 协商期间,分支中的 IKE ID 用于匹配中枢上配置的对等 IKE 身份的公共部分。有效的证书可对分支进行身份验证。
证书标识的公共部分可以是以下部分之一:
证书的备用使用者字段最右侧的部分主机名,例如
example.net。证书的备用主题字段最右侧的部分电子邮件地址,例如
@example.net。容器字符串和/或一组通配符,以匹配证书的主题字段。主题字段包含采用抽象语法表示法一 (ASN.1) 可分辨名称 (DN) 格式的数字证书持有者的详细信息。字段可以包括组织、组织单位、国家/地区、地点或公用名。
要将组 IKE ID 配置为匹配证书中的使用者字段,可以指定以下类型的身份匹配:
容器 — 如果分支证书的主题字段与中心配置的值完全匹配,则中心将验证分支的 IKE ID。可以为每个主题字段指定多个条目(例如,
ou=eng,ou=sw)。字段中值的顺序必须匹配。通配符 — 如果分支证书的主题字段与中心配置的值匹配,则中心将验证分支的 IKE ID。通配符匹配仅支持每个字段一个值(例如,
ou=eng或ou=sw,但不支持ou=eng,ou=sw)。字段的顺序无关紧要。
以下示例在证书的备用使用者字段中使用部分主机名 example.net 配置组 IKE ID。
[edit]
security {
ike {
policy common-cert-policy {
proposals common-ike-proposal;
certificate {
local-certificate hub-local-certificate;
}
}
gateway common-gateway-to-all-spoke-peer {
ike-policy common-cert-policy;
dynamic {
hostname example.net;
ike-user-type group-ike-id;
}
external-interface fe-0/0/2;
}
}
}
在此示例中, example.net 是用于所有分支的主机名标识的公共部分。分支上的所有 X.509 证书都必须在备用主题字段中 example.net 包含主机名标识,并在最右侧部分包含主机名标识。所有分支都必须在其 IKE ID 有效负载中使用主机名标识。
以下示例使用通配符配置组 IKE ID,以匹配证书的组织单位和example组织主题字段中的值sales。
[edit]
security {
ike {
policy common-cert-policy {
proposals common-ike-proposal;
certificate {
local-certificate hub-local-certificate;
}
}
gateway common-gateway-to-all-spoke-peer {
ike-policy common-cert-policy;
dynamic {
distinguished-name {
wildcard ou=sales,o=example;
}
ike-user-type group-ike-id;
}
external-interface fe-0/0/2;
}
}
}
在此示例中,字段 ou=sales,o=example 是辐射中预期证书中主题字段的公共部分。在 IKE 协商期间,如果分支提供证书中包含主题字段 cn=alice,ou=sales,o=example 的证书,则身份验证成功并建立隧道。如果分支提供证书中带有主题字段 cn=thomas,ou=engineer,o=example 的证书,则中心将拒绝该证书,因为组织单位应拒绝该证书 sales。
排除分支连接
若要从连接到中心的过程中排除特定分支,必须吊销该分支的证书。中心需要从包含已吊销证书序列号的 CA 检索最新的证书吊销列表 (CRL)。然后,中心将拒绝来自已吊销分支的 VPN 连接。在最新的 CRL 在中心可用之前,中心可能会继续从已吊销的分支建立隧道。有关详细信息,请参阅 注册证书 和 证书颁发机构配置文件。
另请参阅
AutoVPN 配置概述
以下步骤介绍了在中心辐射设备上配置 AutoVPN 的基本任务。AutoVPN 中心为所有当前分支和新分支配置 一次 。
要配置 AutoVPN 集线器,请执行以下操作:
要配置 SRX 系列 AutoVPN 分支设备,请执行以下操作:
在设备中注册 CA 证书和本地证书。
如果在 Hub 上配置预共享密钥身份验证,请使用基于预共享密钥的身份验证方法。
创建 st0 接口并将其配置为点对多点模式。
配置 IKE 策略以匹配中心上配置的 IKE 策略。
使用 ID 配置 IKE 网关,使其与集线器上配置的组 IKE ID 匹配。
配置 IPsec 策略以匹配中心上配置的 IPsec 策略。
配置动态路由协议。
本主题中列出的示例使用运行 Junos OS 的 SRX 系列防火墙进行中心辐射配置。如果分支设备未运行 Junos OS,则需要配置下一跃点隧道绑定。
另请参阅
示例:使用 iBGP 配置基本 AutoVPN
此示例说明如何将 AutoVPN 中心配置为充当单个终结点,然后将两个分支配置为充当到远程站点的隧道。此示例将 iBGP 配置为通过 VPN 隧道转发数据包,并使用基于证书的身份验证。
有关使用预共享密钥进行身份验证的信息,请参阅 分步过程 中心 位置的“配置第 1 阶段选项”步骤以配置中心、 分步过程 分支 1 以配置分支 1,分支 分步过程 2 以配置分支 2。
要求
此示例使用以下硬件和软件组件:
-
三个受支持的 SRX 系列防火墙作为 AutoVPN 中心和分支
-
支持 AutoVPN 的 Junos OS 12.1X44-D10 及更高版本
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。有关动态路由协议的特定要求的详细信息,请参阅 路由协议概述。
概述
此示例显示了 AutoVPN 中心的配置以及两个分支的后续配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。分支的证书在主题字段中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。
分支与中心建立 IPsec VPN 连接,使它们能够相互通信以及访问中心上的资源。在 AutoVPN 中心和所有分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 3 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
2 |
|
身份验证算法 |
SHA-1 |
|
加密算法 |
AES 128 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
身份验证算法 |
HMAC MD5 96 |
|
加密算法 |
加拿大广播公司 |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
14 |
在所有设备上配置相同的证书颁发机构 (CA)。
Junos OS 仅支持单级证书层次结构。
表 4 显示在中心和所有辐射上配置的选项。
|
选项 |
枢纽 |
所有辐条 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
动态 |
1 0.1.1.1 |
|
远程 IKE ID |
分支证书上的可分辨名称 (DN),组织单位 (OU) 字段中的字符串 |
集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
ge-0/0/1.0 |
辐条1:铁-0/0/1.0 辐条2:ge-0/0/1.0 |
|
VPN: |
||
|
绑定接口 |
st0.0 |
st0.0 |
|
建立隧道 |
(未配置) |
配置提交后立即 |
表 5 显示了每个分支上不同的配置选项。
|
选项 |
辐条 1 |
辐条 2 |
|---|---|---|
|
ST0.0 接口 |
10.10.10.2/24 |
10.10.10.3/24 |
|
与内部网络的接口 |
(fe-0.0/4.0) 10.60.60.1/24 |
(fe-0.0/4.0) 10.70.70.1/24 |
|
互联网接口 |
(fe-0/0/1.0) 10.2.2.1/30 |
(ge-0/0/1.0) 10.3.3.1/30 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。如果您使用的是 PSK,请忽略此步骤。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2012 09:39 Not after: 11- 6-2013 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2012 09:40 Not after: 11- 6-2013 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
分步过程
要使用分支 2 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke2@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke2,OU=SLT,O=example,L=Tumkur,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40bb71d400000000258f Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Tumkur, Common name: spoke2, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2 Alternate subject: "spoke2@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 6-2012 10:02 Not after: 11- 6-2013 10:12 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:b6:2e:e2:da:e6:ac:57:e4:5d:ff:de:f6:89 27:d6:3e:1b:4a:3f:b2:2d:b3:d3:61:ed:ed:6a:07:d9:8a:d2:24:03 77:1a:fe:84:e1:12:8a:2d:63:6e:bf:02:6b:15:96:5a:4f:37:a0:46 44:09:96:c0:fd:bb:ab:79:2c:5d:92:bd:31:f0:3b:29:51:ce:89:8e 7c:2b:02:d0:14:5b:0a:a9:02:93:21:ea:f9:fc:4a:e7:08:bc:b1:6d 7c:f8:3e:53:58:8e:f1:86:13:fe:78:b5:df:0b:8e:53:00:4a:46:11 58:4a:38:e9:82:43:d8:25:47:7d:ef:18:f0:ef:a7:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 1a:6d:77:ac:fd:94:68:ce:cf:8a:85:f0:39:fc:e0:6b:fd:fe:b8:66 (sha1) 00:b1:32:5f:7b:24:9c:e5:02:e6:72:75:9e:a5:f4:77 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.1.1.1/30 set interfaces ge-0/0/3 unit 0 family inet address 10.50.50.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.1/24 set policy-options policy-statement lan_nw from interface ge-0/0/3.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 10.10.10.1 set protocols bgp group ibgp export lan_nw set protocols bgp group ibgp cluster 10.2.3.4 set protocols bgp group ibgp peer-as 65010 set policy-options policy-statement lan_nw from interface ge-0/0/3.0 set policy-options policy-statement lan_nw then accept set policy-options policy-statement bgp_nh_self term 1 from protocol bgp set policy-options policy-statement bgp_nh_self term 1 then next-hop self set policy-options policy-statement bgp_nh_self term 1 then accept set protocols bgp group ibgp export bgp_nh_self set protocols bgp group ibgp allow 10.10.10.0/24 set routing-options static route 10.2.2.0/30 next-hop 10.1.1.2 set routing-options static route 10.3.3.0/30 next-hop 10.1.1.2 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway hub-to-spoke-gw ike-policy ike-policy1 set security ike gateway hub-to-spoke-gw dynamic distinguished-name wildcard OU=SLT set security ike gateway hub-to-spoke-gw dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw local-identity distinguished-name set security ike gateway hub-to-spoke-gw external-interface ge-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn hub-to-spoke-vpn bind-interface st0.0 set security ipsec vpn hub-to-spoke-vpn ike gateway hub-to-spoke-gw set security ipsec vpn hub-to-spoke-vpn ike ipsec-policy vpn-policy1 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/3.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.1.1.1/30 user@host# set ge-0/0/3 unit 0 family inet address 10.50.50.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.1/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface ge-0/0/3.0 user@host# set policy-statement lan_nw then accept user@host# set policy-statement bgp_nh_self term 1 from protocol bgp user@host# set policy-statement bgp_nh_self term 1 then next-hop self user@host# set policy-statement bgp_nh_self term 1 then accept [edit protocols bgp] user@host# set group ibgp type internal user@host# set group ibgp local-address 10.10.10.1 user@host# set group ibgp export lan_nw user@host# set group ibgp cluster 10.2.3.4 user@host# set group ibgp peer-as 65010 user@host# set group ibgp allow 10.10.10.0/24 user@host# set group ibgp export bgp_nh_self [edit routing-options] user@host# set static route 10.2.2.0/30 next-hop 10.1.1.2 user@host# set static route 10.3.3.0/30 next-hop 10.1.1.2 user@host# set autonomous-system 65010
-
配置第 1 阶段选项。
如果您打算使用预共享密钥而不是证书进行身份验证,请在配置中进行以下更改:
在 ike 提议中,在 [
edit security ike proposal ike-proposal] 层次结构级别,替换为authentication-method rsa-signaturesauthentication-method pre-shared-keys.有关选项的详细信息,请参阅提议(安全 IKE)。
在 ike 策略的 [
edit security ike policy policy-name] 层次结构级别,替换为certificate local-certificate Local1pre-shared-key ascii-text key。例如,
set pre-shared-key ascii-text juniper123
有关选项的详细信息,请参阅策略 (安全 IKE)。
在 IKE 网关的 [
edit security ike gateway hub-to-spoke-gw] 层次结构级别,替换为
dynamic distinguished-name wildcard OU=SLTdynamic hostname domain-name.例如,
set dynamic hostname juniper.net确保您的设备能够解析主机名。或者,也可以对分支动态标识使用
set dynamic general-ikeid和set dynamic ike-user-type group-ike-id。
替换为
local-identity distinguished-namelocal-identity hostname hub-hostname.例如,
set local-identity hostname hub.juniper.net.确保您的设备能够解析主机名。或者,也可以如
inet ip-address中使用 中的 。set local-identity inet 192.168.1.100
有关选项的详细信息,请参阅网关(安全 IKE)。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway hub-to-spoke-gw] user@host# set ike-policy ike-policy1 user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn hub-to-spoke-vpn] user@host# set bind-interface st0.0 user@host# set ike gateway hub-to-spoke-gw user@host# set ike ipsec-policy vpn-policy1
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/3.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。如果您使用的是 PSK,请忽略此步骤。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.1.1.1/30;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 10.50.50.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.1/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement bgp_nh_self {
term 1 {
from protocol bgp;
then {
next-hop self;
accept;
}
}
}
policy-statement lan_nw {
from interface ge-0/0/3.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp {
type internal;
local-address 10.10.10.1;
export lan_nw;
cluster 10.2.3.4;
peer-as 65010;
allow 10.10.10.0/24;
export bgp_nh_self;
}
}
[edit]
user@host# show routing-options
static {
route 10.2.2.0/30 next-hop 10.1.1.2;
route 10.3.3.0/30 next-hop 10.1.1.2;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway hub-to-spoke-gw {
ike-policy ike-policy1;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn hub-to-spoke-vpn {
bind-interface st0.0;
ike {
gateway hub-to-spoke-gw;
ipsec-policy vpn-policy1;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.0;
ge-0/0/1.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/3.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces fe-0/0/1 unit 0 family inet address 10.2.2.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.60.60.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.2/24 set policy-options policy-statement lan_nw from interface fe-0/0/4.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 10.10.10.2 set protocols bgp group ibgp export lan_nw set protocols bgp group ibgp neighbor 10.10.10.1 set routing-options static route 10.1.1.0/30 next-hop 10.2.2.2 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway spoke-to-hub-gw ike-policy ike-policy1 set security ike gateway spoke-to-hub-gw address 10.1.1.1 set security ike gateway spoke-to-hub-gw local-identity distinguished-name set security ike gateway spoke-to-hub-gw remote-identity distinguished-name set security ike gateway spoke-to-hub-gw external-interface fe-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn spoke-to-hub bind-interface st0.0 set security ipsec vpn spoke-to-hub ike gateway spoke-to-hub-gw set security ipsec vpn spoke-to-hub ike ipsec-policy vpn-policy1 set security ipsec vpn spoke-to-hub establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces fe-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set fe-0/0/1 unit 0 family inet address 10.2.2.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.60.60.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.2/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface fe-0/0/4.0 user@host# set policy-statement lan_nw then accept [edit protocols bgp] user@host# set group ibgp type internal user@host# set group ibgp local-address 10.10.10.2 user@host# set group ibgp export lan_nw user@host# set group ibgp neighbor 10.10.10.1 [edit routing-options] user@host# set static route 10.1.1.0/30 next-hop 10.2.2.2 user@host# set autonomous-system 10
-
配置第 1 阶段选项。
如果您打算使用预共享密钥而不是证书进行身份验证,请在配置中进行以下更改。
在 ike 提议中,在 [
edit security ike proposal ike-proposal] 层次结构级别,替换为authentication-method rsa-signaturesauthentication-method pre-shared-keys.在 ike 策略的 [
edit security ike policy policy-name] 层次结构级别,替换为certificate local-certificate Local1pre-shared-key ascii-text key。在 IKE 网关的 [
edit security ike gateway hub-to-spoke-gw] 层次结构级别,替换为
local-identity distinguished-namelocal-identity hostname spoke1-hostname.例如,
set local-identity hostname spoke1.juniper.net.
替换为
remote-identity distinguished-nameremote-identity hostname hub-hostname.例如,
set remote-identity hostname hub.juniper.net
确保您的设备能够解析主机名。或者,您也可以在
inet ip-address和 中使用set local-identity inet 172.16.1.100as 和set remote-identity inet 192.168.1.100。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway spoke-to-hub-gw] user@host# set ike-policy ike-policy1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub] user@host# set bind-interface st0.0 user@host# set ike gateway spoke-to-hub-gw user@host# set ike ipsec-policy vpn-policy1 user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。如果您使用的是 PSK,请忽略此步骤。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
fe-0/0/1 {
unit 0 {
family inet {
address 10.2.2.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.60.60.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.2/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement lan_nw {
from interface fe-0/0/4.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp {
type internal;
local-address 10.10.10.2;
export lan_nw;
neighbor 10.10.10.1;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.0/30 next-hop 10.2.2.2;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway spoke-to-hub-gw {
ike-policy ike-policy1;
address 10.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub {
bind-interface st0.0;
ike {
gateway spoke-to-hub-gw;
ipsec-policy vpn-policy1;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/1.0;
st0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 2
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.3.3.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.70.70.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.3/24 set policy-options policy-statement lan_nw from interface fe-0/0/4.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 10.10.10.3 set protocols bgp group ibgp export lan_nw set protocols bgp group ibgp neighbor 10.10.10.1 set routing-options static route 10.1.1.0/30 next-hop 10.3.3.2 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway spoke-to-hub-gw ike-policy ike-policy1 set security ike gateway spoke-to-hub-gw address 10.1.1.1 set security ike gateway spoke-to-hub-gw local-identity distinguished-name set security ike gateway spoke-to-hub-gw remote-identity distinguished-name set security ike gateway spoke-to-hub-gw external-interface ge-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn spoke-to-hub bind-interface st0.0 set security ipsec vpn spoke-to-hub ike gateway spoke-to-hub-gw set security ipsec vpn spoke-to-hub ike ipsec-policy vpn-policy1 set security ipsec vpn spoke-to-hub establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 2:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.3.3.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.70.70.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.3/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface fe-0/0/4.0 user@host# set policy-statement lan_nw then accept [edit protocols bgp] user@host# set group ibgp type internal user@host# set group ibgp local-address 10.10.10.3 user@host# set group ibgp export lan_nw user@host# set group ibgp neighbor 10.10.10.1 [edit routing-options] user@host# set static route 10.1.1.0/30 next-hop 10.3.3.2 user@host# set autonomous-system 10
-
配置第 1 阶段选项。
如果您打算使用预共享密钥而不是证书进行身份验证,请在配置中进行以下更改。
在 ike 提议中,在 [
edit security ike proposal ike-proposal] 层次结构级别,替换为authentication-method rsa-signaturesauthentication-method pre-shared-keys.在 ike 策略的 [
edit security ike policy policy-name] 层次结构级别,替换为certificate local-certificate Local1pre-shared-key ascii-text key。在 IKE 网关的 [
edit security ike gateway hub-to-spoke-gw] 层次结构级别,替换为
local-identity distinguished-namelocal-identity hostname spoke2-hostname.例如,
set local-identity hostname spoke2.juniper.net
替换为
remote-identity distinguished-nameremote-identity hostname hub-hostname.例如,
set remote-identity hostname hub.juniper.net
确保您的设备能够解析主机名。或者,您也可以在
inet ip-address和 中使用set local-identity inet 10.0.1.100as 和set remote-identity inet 192.168.1.100。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway spoke-to-hub-gw] user@host# set ike-policy ike-policy1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface ge-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub] user@host# set bind-interface st0.0 user@host# set ike gateway spoke-to-hub-gw user@host# set ike ipsec-policy vpn-policy1 user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。如果您使用的是 PSK,请忽略此步骤。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.3.3.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.70.70.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.3/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement lan_nw {
from interface fe-0/0/4.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp {
type internal;
local-address 10.10.10.3;
export lan_nw;
neighbor 10.10.10.1;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.0/30 next-hop 10.3.3.2;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway spoke-to-hub-gw {
ike-policy ike-policy1;
address 10.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface ge-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub {
bind-interface st0.0;
ike {
gateway spoke-to-hub-gw;
ipsec-policy vpn-policy1;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
st0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证 IKE 第 1 阶段状态
目的
验证 IKE 第 1 阶段状态。
操作
在操作模式下,输入 show security ike security-associations 命令。
user@host> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 5480163 UP a558717f387074ab 6d0135c5ecaed61d Main 10.3.3.1 5480162 UP 7a63d16a5a723df1 c471f7ae166d3a34 Main 10.2.2.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 第 2 阶段状态
目的
验证 IPsec 第 2 阶段状态。
操作
在操作模式下,输入 security ipsec security-associations 命令。
user@host> security ipsec security-associations Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway <268173400 ESP:des/ md5 9bf33bc7 3567/ unlim - root 500 10.2.2.1 >268173400 ESP:des/ md5 aae5196b 3567/ unlim - root 500 10.2.2.1 <268173401 ESP:des/ md5 69c24d81 622/ unlim - root 500 10.3.3.1 >268173401 ESP:des/ md5 e3fe0231 622/ unlim - root 500 10.3.3.1
意义
该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 10.10.10.2 st0.0 hub-to-spoke-vpn Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 10.10.10.3 st0.0 hub-to-spoke-vpn Auto C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 BGP
目的
验证 BGP 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show bgp summary 命令。
user@host> show bgp summary Groups: 1 Peers: 2 Down peers: 0 Unconfigured peers: 2 Table Tot Paths Act Paths Suppressed History Damp State Pending inet.0 2 2 0 0 0 0 Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped... 10.10.10.2 10 116 119 0 0 50:25 1/1/1/0 0/0/0/0 10.10.10.3 10 114 114 0 0 50:04 1/1/1/0 0/0/0/0
验证学习的路由
目的
验证是否已获知到分支的路由。
操作
在操作模式下,输入 show route 10.60.60.0 命令。
user@host> show route 10.60.60.0
inet.0: 45 destinations, 45 routes (44 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
10.60.60.0/24 *[BGP/170] 00:50:57, localpref 100
AS path: I
> to 10.10.10.2 via st0.0
在操作模式下,输入 show route 10.70.70.0 命令。
user@host> show route 10.70.70.0
inet.0: 45 destinations, 45 routes (44 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
10.70.70.0/24 *[BGP/170] 00:50:42, localpref 100
AS path: I
> to 10.10.10.3 via st0.0
示例:为 IPv6 流量配置带有 iBGP 的基本 AutoVPN
此示例说明如何将 AutoVPN 中心配置为充当单个终结点,然后将两个分支配置为充当到远程站点的隧道。此示例使用 iBGP 配置 AutoVPN for IPv6 环境,以使用基于证书的身份验证通过 VPN 隧道转发数据包。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
三个支持 SRX 系列防火墙作为 AutoVPN 中心和辐射。
-
Junos OS 18.1R1 及更高版本。
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。有关动态路由协议的特定要求的详细信息,请参阅 路由协议概述。
概述
此示例显示了 AutoVPN 中心的配置以及两个分支的后续配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。分支的证书在主题字段中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。
分支与中心建立 IPsec VPN 连接,使它们能够相互通信以及访问中心上的资源。在 AutoVPN 中心和所有分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 6 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
19 |
|
身份验证算法 |
SHA-384 |
|
加密算法 |
AES 256 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
终身秒数 |
3000 |
|
加密算法 |
AES 256 GCM |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
19 |
在所有设备上配置相同的证书颁发机构 (CA)。
Junos OS 仅支持单级证书层次结构。
表 7 显示在中心和所有辐射上配置的选项。
|
选项 |
枢纽 |
所有辐条 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
动态 |
2001:db8:2000::1 |
|
远程 IKE ID |
分支证书上的可分辨名称 (DN),组织单位 (OU) 字段中的字符串 |
集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
ge-0/0/0 |
辐条1:ge-0/0/0.0 辐条2:ge-0/0/0.0 |
|
VPN: |
||
|
绑定接口 |
st0.1 |
st0.1 |
|
建立隧道 |
(未配置) |
建立隧道流量 |
表 8 显示了每个分支上不同的配置选项。
|
选项 |
辐条 1 |
辐条 2 |
|---|---|---|
|
ST0.0 接口 |
2001:db8:7000::2/64 |
2001:db8:7000::3/64 |
|
与内部网络的接口 |
(ge-0/0/1.0) 2001:db8:4000::1/64 |
(ge-0/0/1.0) 2001:db8:6000::1/64 |
|
互联网接口 |
(ge-0/0/0.0) 2001:db8:3000::2/64 |
(ge-0/0/0.0) 2001:db8:5000::2/64 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2012 09:39 Not after: 11- 6-2013 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2012 09:40 Not after: 11- 6-2013 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
分步过程
要使用分支 2 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke2@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke2,OU=SLT,O=example,L=Tumkur,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40bb71d400000000258f Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Tumkur, Common name: spoke2, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2 Alternate subject: "spoke2@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 6-2012 10:02 Not after: 11- 6-2013 10:12 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:b6:2e:e2:da:e6:ac:57:e4:5d:ff:de:f6:89 27:d6:3e:1b:4a:3f:b2:2d:b3:d3:61:ed:ed:6a:07:d9:8a:d2:24:03 77:1a:fe:84:e1:12:8a:2d:63:6e:bf:02:6b:15:96:5a:4f:37:a0:46 44:09:96:c0:fd:bb:ab:79:2c:5d:92:bd:31:f0:3b:29:51:ce:89:8e 7c:2b:02:d0:14:5b:0a:a9:02:93:21:ea:f9:fc:4a:e7:08:bc:b1:6d 7c:f8:3e:53:58:8e:f1:86:13:fe:78:b5:df:0b:8e:53:00:4a:46:11 58:4a:38:e9:82:43:d8:25:47:7d:ef:18:f0:ef:a7:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 1a:6d:77:ac:fd:94:68:ce:cf:8a:85:f0:39:fc:e0:6b:fd:fe:b8:66 (sha1) 00:b1:32:5f:7b:24:9c:e5:02:e6:72:75:9e:a5:f4:77 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate HUB set security ike gateway IKE_GWA_1 ike-policy IKE_POL set security ike gateway IKE_GWA_1 dynamic distinguished-name wildcard OU=SLT set security ike gateway IKE_GWA_1 dead-peer-detection always-send set security ike gateway IKE_GWA_1 dead-peer-detection interval 10 set security ike gateway IKE_GWA_1 dead-peer-detection threshold 3 set security ike gateway IKE_GWA_1 local-identity distinguished-name set security ike gateway IKE_GWA_1 external-interface ge-0/0/0 set security ike gateway IKE_GWA_1 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPNA_1 bind-interface st0.1 set security ipsec vpn IPSEC_VPNA_1 ike gateway IKE_GWA_1 set security ipsec vpn IPSEC_VPNA_1 ike ipsec-policy IPSEC_POL set security policies default-policy permit-all set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/0.0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:2000::1/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:1000::2/64 set interfaces st0 unit 1 multipoint set interfaces st0 unit 1 family inet6 address 2001:db8:7000::1/64 set routing-options rib inet6.0 static route 2001:db8:3000::/64 next-hop 2001:db8:2000::2 set routing-options rib inet6.0 static route 2001:db8:5000::/64 next-hop 2001:db8:2000::2 set routing-options autonomous-system 100 set routing-options forwarding-table export load_balance set protocols bgp traceoptions file bgp set protocols bgp traceoptions flag all set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 2001:db8:9000::1 set protocols bgp group ibgp export ibgp set protocols bgp group ibgp cluster 10.1.3.4 set protocols bgp group ibgp peer-as 100 set protocols bgp group ibgp multipath set protocols bgp group ibgp allow 2001:db8:9000::/64 set policy-options policy-statement ibgp from interface ge-0/0/1.0 set policy-options policy-statement ibgp then accept set policy-options policy-statement load_balance then load-balance per-packet
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:2000::1/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:1000::2/64 user@host# set st0 unit 1 multipoint user@host# set st0 unit 1 family inet6 address 2001:db8:7000::1/64
-
配置路由协议。
[edit policy-options] user@host# set policy-statement ibgp from interface ge-0/0/1.0 user@host# set policy-statement ibgp then accept user@host# set policy-statement load_balance then load-balance per-packet [edit protocols bgp] user@host# set traceoptions file bgp user@host# set traceoptions flag all user@host# set group ibgp type internal user@host# set group ibgp local-address 2001:db8:9000::1 user@host# set group ibgp export ibgp user@host# set group ibgp cluster 10.1.3.4 user@host# set group ibgp peer-as 100 user@host# set group ibgp multipath user@host# set group ibgp allow 2001:db8:9000::/64 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:3000::/64 next-hop 2001:db8:2000::2 user@host# set rib inet6.0 static route 2001:db8:5000::/64 next-hop 2001:db8:2000::2 user@host# set autonomous-system 100 user@host# set forwarding-table export load_balance
-
配置第 1 阶段选项。
[edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike proposal ike-proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate HUB [edit security ike gateway IKE_GWA_1] user@host# set ike-policy IKE_POL user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROP] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPNA_1] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GWA_1 user@host# set ike ipsec-policy IPSEC_POL
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:2000::1/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:1000::2/64;
}
}
}
st0 {
unit 1{
multipoint;
family inet6 {
address 2001:db8:7000::1/64;
}
}
}
[edit]
user@host# show policy-options
policy-statement ibgp {
from interface ge-0/0/1.0;
then accept;
}
policy-statement load_balance {
then {
load-balance per-packet;
}
}
[edit]
user@host# show protocols
bgp {
traceoptions {
file bgp;
flag all;
}
group ibgp {
type internal;
local-address 2001:db8:9000::1;
export ibgp;
cluster 10.1.3.4;
peer-as 100;
multipath;
allow 2001:db8:9000::/64;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route route 2001:db8:3000::/64 next-hop 2001:db8:2000::2;
route 2001:db8:5000::/64 next-hop 2001:db8:2000::2;
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate HUB;
}
}
gateway IKE_GWA_1 {
ike-policy IKE_POL;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
}
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
external-interface ge-0/0/0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPNA_1 {
bind-interface st0.1;
ike {
gateway IKE_GWA_1;
ipsec-policy IPSEC_POL;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate SPOKE1 set security ike gateway IKE_GW_SPOKE_1 ike-policy IKE_POL set security ike gateway IKE_GW_SPOKE_1 address 2001:db8:2000::1 set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection always-send set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection interval 10 set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection threshold 3 set security ike gateway IKE_GW_SPOKE_1 local-identity distinguished-name set security ike gateway IKE_GW_SPOKE_1 remote-identity distinguished-name container OU=SLT set security ike gateway IKE_GW_SPOKE_1 external-interface ge-0/0/0.0 set security ike gateway IKE_GW_SPOKE_1 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN_SPOKE_1 bind-interface st0.1 set security ipsec vpn IPSEC_VPN_SPOKE_1 ike gateway IKE_GW_SPOKE_1 set security ipsec vpn IPSEC_VPN_SPOKE_1 ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN_SPOKE_1 establish-tunnels on-traffic set security policies default-policy permit-all set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces st0.1 set security zones security-zone untrust interfaces ge-0/0/1.0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:3000::2/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:4000::1/64 set interfaces st0 unit 1 family inet6 address 2001:db8:7000::2/64 set routing-options rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:3000::1 set routing-options autonomous-system 100 set protocols bgp traceoptions file bgp set protocols bgp traceoptions flag all set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 2001:db8:9000::2 set protocols bgp group ibgp export ibgp set protocols bgp group ibgp peer-as 100 set protocols bgp group ibgp neighbor 2001:db8:9000::1 set policy-options policy-statement ibgp from interface ge-0/0/1.0 set policy-options policy-statement ibgp then accept
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:3000::2/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:4000::1/64 user@host# set st0 unit 1 family inet6 address 2001:db8:7000::2/64
-
配置路由协议。
[edit policy-options] user@host# set policy-statement ibgp from interface ge-0/0/1.0 user@host# set policy-statement ibgp then accept [edit protocols bgp] user@host# set traceoptions file bgp user@host# set traceoptions flag all user@host# set group ibgp type internal user@host# set group ibgp local-address 2001:db8:9000::2 user@host# set group ibgp export ibgp user@host# set group ibgp peer-as 100 user@host# set group ibgp neighbor 2001:db8:9000::1 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:3000::1 user@host# set autonomous-system 100
-
配置第 1 阶段选项。
[edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike proposal ike-proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate SPOKE1 [edit security ike gateway IKE_GW_SPOKE_1] user@host# set ike-policy IKE_POL user@host# set address 2001:db8:2000::1 user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name container OU=SLT user@host# set external-interface ge-0/0/0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROP] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPNA_SPOKE_1] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GWA_SPOKE_1 user@host# set ike ipsec-policy IPSEC_POL user@host# set establish-tunnels on-traffic
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:3000::2/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:4000::1/64;
}
}
}
st0 {
unit 1{
family inet6 {
address 2001:db8:7000::2/64;
}
}
}
[edit]
user@host# show policy-options
policy-statement ibgp {
from interface ge-0/0/1.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
traceoptions {
file bgp;
flag all;
}
group ibgp {
type internal;
local-address 2001:db8:9000::2;
export ibgp;
peer-as 100;
neighbor 2001:db8:9000::1;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route route 2001:db8:2000::/64 next-hop 2001:db8:3000::1;
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate SPOKE1;
}
}
gateway IKE_GWA_SPOKE1 {
ike-policy IKE_POL;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
}
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
external-interface ge-0/0/0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPNA_SPOKE_1 {
bind-interface st0.1;
ike {
gateway IKE_GWA_SPOKE_1;
ipsec-policy IPSEC_POL;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 2
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate SPOKE2 set security ike gateway IKE_GW_SPOKE_2 ike-policy IKE_POL set security ike gateway IKE_GW_SPOKE_2 address 2001:db8:2000::1 set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection always-send set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection interval 10 set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection threshold 3 set security ike gateway IKE_GW_SPOKE_2 local-identity distinguished-name set security ike gateway IKE_GW_SPOKE_2 remote-identity distinguished-name container OU=SLT set security ike gateway IKE_GW_SPOKE_2 external-interface ge-0/0/0.0 set security ike gateway IKE_GW_SPOKE_2 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN_SPOKE_2 bind-interface st0.1 set security ipsec vpn IPSEC_VPN_SPOKE_2 ike gateway IKE_GW_SPOKE_2 set security ipsec vpn IPSEC_VPN_SPOKE_2 ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN_SPOKE_2 establish-tunnels on-traffic set security policies default-policy permit-all set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces st0.1 set security zones security-zone untrust interfaces ge-0/0/1.0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:5000::2/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:6000::1/64 set interfaces st0 unit 1 family inet6 address 2001:db8:7000::3/64 set routing-options rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:5000::1 set routing-options autonomous-system 100 set protocols bgp traceoptions file bgp set protocols bgp traceoptions flag all set protocols bgp group ibgp type internal set protocols bgp group ibgp local-address 2001:db8:9000::3 set protocols bgp group ibgp export ibgp set protocols bgp group ibgp peer-as 100 set protocols bgp group ibgp neighbor 2001:db8:9000::1 set policy-options policy-statement ibgp from interface ge-0/0/1.0 set policy-options policy-statement ibgp then accept
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 2:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:5000::2/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:6000::1/64 user@host# set st0 unit 1 family inet6 address 2001:db8:7000::3/64
-
配置路由协议。
[edit policy-options] user@host# set policy-statement ibgp from interface ge-0/0/1.0 user@host# set policy-statement ibgp then accept [edit protocols bgp] user@host# set traceoptions file bgp user@host# set traceoptions flag all user@host# set group ibgp type internal user@host# set group ibgp local-address 2001:db8:9000::3 user@host# set group ibgp export ibgp user@host# set group ibgp peer-as 100 user@host# set group ibgp neighbor 2001:db8:9000::1 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:5000::1 user@host# set autonomous-system 100
-
配置第 1 阶段选项。
[edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike proposal ike-proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate SPOKE2 [edit security ike gateway IKE_GW_SPOKE_2] user@host# set ike-policy IKE_POL user@host# set address 2001:db8:2000::1 user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name container OU=SLT user@host# set external-interface ge-0/0/0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROP] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPNA_SPOKE_2] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GWA_SPOKE_2 user@host# set ike ipsec-policy IPSEC_POL user@host# set establish-tunnels on-traffic
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:5000::2/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:6000::1/64;
}
}
}
st0 {
unit 1{
family inet6 {
address 2001:db8:7000::3/64;
}
}
}
[edit]
user@host# show policy-options
policy-statement ibgp {
from interface ge-0/0/1.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
traceoptions {
file bgp;
flag all;
}
group ibgp {
type internal;
local-address 2001:db8:9000::3;
export ibgp;
peer-as 100;
neighbor 2001:db8:9000::1;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route route 2001:db8:2000::/64 next-hop 2001:db8:5000::1;
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate SPOKE2;
}
}
gateway IKE_GWA_SPOKE2 {
ike-policy IKE_POL;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
}
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
external-interface ge-0/0/0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPNA_SPOKE_2 {
bind-interface st0.1;
ike {
gateway IKE_GWA_SPOKE_2;
ipsec-policy IPSEC_POL;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证 IKE 状态
目的
验证 IKE 状态。
操作
在操作模式下,输入 show security ike sa 命令。
user@host> show security ike sa Index State Initiator cookie Responder cookie Mode Remote Address 493333 UP 2001:db8:88b49d915e684c93 2001:db8:fe890b1cac8522b5 Main 2001:db8:3000::2 493334 UP 2001:db8:26e40244ad3d722d 2001:db8:68b4d9f94097d32e Main 2001:db8:5000::2
意义
该 show security ike sa 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 状态
目的
验证 IPsec 状态。
操作
在操作模式下,输入 show security ipsec sa 命令。
user@host> show security ipsec sa Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway >67108885 ESP:aes-gcm-256/None fdef4dab 2918/ unlim - root 500 2001:db8:3000::2 >67108885 ESP:aes-gcm-256/None e785dadc 2918/ unlim - root 500 2001:db8:3000::2 >67108887 ESP:aes-gcm-256/None 34a787af 2971/ unlim - root 500 2001:db8:5000::2 >67108887 ESP:aes-gcm-256/None cf57007f 2971/ unlim - root 500 2001:db8:5000::2
意义
该 show security ipsec sa 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 2001:db8:9000::2 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE1 Not-Available 2001:db8:9000::3 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE2 Not-Available 2001:db8::5668:ad10:fcd8:163c st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE1 Not-Available 2001:db8::5668:ad10:fcd8:18a1 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE2 Not-Available
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 BGP
目的
验证 BGP 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show bgp summary 命令。
user@host> show bgp summary
Groups: 1 Peers: 2 Down peers: 0
Unconfigured peers: 2
Table Tot Paths Act Paths Suppressed History Damp State Pending
inet6.0
2 2 0 0 0 0
Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State
2001:db8:9000::2 100 4 4 0 0 32 Establ
inet6.0: 1/1/1/0
2001:db8:9000::3 100 4 4 0 0 8 Establ
inet6.0: 1/1/1/0示例:使用 iBGP 和 ECMP 配置 AutoVPN
此示例说明如何在 AutoVPN 中心和分支之间配置两个 IPsec VPN 隧道。此示例将 iBGP 配置为具有等价多路径 (ECMP),以使用基于证书的身份验证通过 VPN 隧道转发数据包。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
两个受支持的 SRX 系列防火墙作为 AutoVPN 中心和分支防火墙
-
支持 AutoVPN 的 Junos OS 12.1X44-D10 及更高版本
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。
概述
此示例显示了具有两个 IPsec VPN 隧道的 AutoVPN 中心和分支的配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。证书在中心和每个 IPsec VPN 隧道的分支中注册。分支的其中一个证书在可分辨名称 (DN) 中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。分支的另一个证书在 DN 中包含 OU 值“SBU”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SBU”。
分支与中心建立 IPsec VPN 连接,从而允许它访问中心上的资源。在 AutoVPN 中心和分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。表 9 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
2 |
|
身份验证算法 |
SHA-1 |
|
加密算法 |
AES 128 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
身份验证算法 |
HMAC MD5 96 |
|
加密算法 |
加拿大广播公司 |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
14 |
在所有设备上配置相同的证书颁发机构 (CA)。
Junos OS 仅支持单级证书层次结构。
表 10 显示在中心和分支上配置的选项。
|
选项 |
枢纽 |
辐条 1 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
中心到辐射型 GW-1:动态 中心到辐射型 GW-2:动态 |
分支到集线器-GW-1:1 0.1.1.1 分支到集线器-GW-2:10.1.2.1 |
|
远程 IKE ID |
中心到辐射型 GW-1:分支证书上的 DN,OU 字段中有字符串 中心到辐射型 GW-2:分支证书上的 DN,OU 字段中有字符串 |
分支到集线器-GW-1:集线器证书上的 DN 分支到集线器-GW-2:集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
中心到辐射型 GW-1:ge-0/0/1.0 中心到辐射型 GW-2:ge-0/0/2.0 |
分支到集线器-GW-1:铁-0/0/1.0 分支到集线器-GW-2:铁-0/0/2.0 |
|
VPN: |
||
|
绑定接口 |
中心到辐射型 VPN-1:st0.0 中心到辐射型 VPN-2:st0.1 |
分支到集线器-1:st0.0 辐射到中枢-2:st0.1 |
|
建立隧道 |
(未配置) |
配置提交后立即 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
为每个证书生成一个密钥对。
user@host> request security pki generate-key-pair certificate-id Local1 user@host> request security pki generate-key-pair certificate-id Local2
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password> user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local2 domain-name example.net email hub_backup@example.net ip-address 10.1.2.1 subject DC=example.net,CN=hub_backup,OU=SBU,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate certificate-id Local1 detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2012 09:39 Not after: 11- 6-2013 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not starteduser@host> show security pki local-certificate certificate-id Local2 detail Certificate identifier: Local2 Certificate version: 3 Serial number: 505efdf900000000259a Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SBU, Country: IN, State: KA, Locality: Bengaluru, Common name: hub_backup, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SBU, CN=hub_backup Alternate subject: "hub_backup@example.net", example.net, 10.1.2.1 Validity: Not before: 11- 9-2012 10:55 Not after: 11- 9-2013 11:05 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d5:44:08:96:f6:77:05:e6:91:50:8a:8a:2a 4e:95:43:1e:88:ea:43:7c:c5:ac:88:d7:a0:8d:b5:d9:3f:41:db:db 44:34:1f:56:a5:38:4b:b2:c5:85:f9:f1:bf:b2:7b:d4:b2:af:98:a0 95:50:02:ad:f5:dd:4d:dc:67:85:dd:84:09:df:9c:68:a5:58:65:e7 2c:72:cc:47:4b:d0:cc:4a:28:ca:09:db:ad:6e:5a:13:6c:e6:cc:f0 29:ed:2b:2d:d1:38:38:bc:68:84:de:ae:86:39:c9:dd:06:d5:36:f0 e6:2a:7b:46:4c:cd:a5:24:1c:e0:92:8d:ad:35:29:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 98:96:2f:ff:ca:af:33:ee:d7:4c:c8:4f:f7:71:53:c0:5d:5f:c5:59 (sha1) c9:87:e3:a4:5c:47:b5:aa:90:22:e3:06:b2:0b:e1:ea (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
为每个证书生成一个密钥对。
user@host> rrequest security pki generate-key-pair certificate-id Local1 user@host> request security pki generate-key-pair certificate-id Local2
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password> user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local2 domain-name example.net email spoke1_backup@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke1_backup,OU=SBU,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate certificate-id Local1 detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2012 09:40 Not after: 11- 6-2013 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started user@host> show security pki local-certificate certificate-id Local2 detail Certificate identifier: Local2 Certificate version: 3 Serial number: 506c3d0600000000259b Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SBU, Country: IN, State: KA, Locality: Mysore, Common name: spoke1_backup, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SBU, CN=spoke1_backup Alternate subject: "spoke1_backup@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 9-2012 11:09 Not after: 11- 9-2013 11:19 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:a7:02:b5:e2:cd:79:24:f8:97:a3:8d:4d:27 8c:2b:dd:f1:57:72:4d:2b:6d:d5:95:0d:9c:1b:5c:e2:a4:b0:84:2e 31:82:3c:91:08:a2:58:b9:30:4c:5f:a3:6b:e6:2b:9c:b1:42:dd:1c cd:a2:7a:84:ea:7b:a6:b7:9a:13:33:c6:27:2b:79:2a:b1:0c:fe:08 4c:a7:35:fc:da:4f:df:1f:cf:f4:ba:bc:5a:05:06:63:92:41:b4:f2 54:00:3f:ef:ff:41:e6:ca:74:10:56:f7:2b:5f:d3:1a:33:7e:49:74 1c:42:cf:c2:23:ea:4b:8f:50:2c:eb:1c:a6:37:89:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: d6:7f:52:a3:b6:f8:ae:cb:70:3f:a9:79:ea:8a:da:9e:ba:83:e4:5f (sha1) 76:0b:72:73:cf:51:ee:58:81:2d:f7:b4:e2:5c:f4:5c (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 适用于
SLT本地 1 和SBU本地 2。中心位置上的 IKE 配置包括OU=SLT和OU=SBU用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.1.1.1/30 set interfaces ge-0/0/2 unit 0 family inet address 10.1.2.1/30 set interfaces ge-0/0/3 unit 0 family inet address 10.50.50.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.1/24 set interfaces st0 unit 1 multipoint set interfaces st0 unit 1 family inet address 10.20.20.1/24 set policy-options policy-statement lan_nw from interface ge-0/0/3.0 set policy-options policy-statement lan_nw then accept set policy-options policy-statement load_balance then load-balance per-packet set protocols bgp group ibgp-1 type internal set protocols bgp group ibgp-1 local-address 10.10.10.1 set protocols bgp group ibgp-1 export lan_nw set protocols bgp group ibgp-1 cluster 10.2.3.4 set protocols bgp group ibgp-1 multipath set protocols bgp group ibgp-1 allow 10.10.10.0/24 set protocols bgp group ibgp-2 type internal set protocols bgp group ibgp-2 local-address 10.20.20.1 set protocols bgp group ibgp-2 export lan_nw set protocols bgp group ibgp-2 cluster 10.2.3.5 set protocols bgp group ibgp-2 multipath set protocols bgp group ibgp-2 allow 10.20.20.0/24 set routing-options static route 10.2.2.0/30 next-hop 10.1.1.2 set routing-options static route 10.3.3.0/30 next-hop 10.1.2.2 set routing-options autonomous-system 65010 set routing-options forwarding-table export load_balance set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy-1 mode main set security ike policy ike-policy-1 proposals ike-proposal set security ike policy ike-policy-1 certificate local-certificate Local1 set security ike policy ike-policy-2 mode main set security ike policy ike-policy-2 proposals ike-proposal set security ike policy ike-policy-2 certificate local-certificate Local2 set security ike gateway hub-to-spoke-gw-1 ike-policy ike-policy-1 set security ike gateway hub-to-spoke-gw-1 dynamic distinguished-name wildcard OU=SLT set security ike gateway hub-to-spoke-gw-1 dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw-1 local-identity distinguished-name set security ike gateway hub-to-spoke-gw-1 external-interface ge-0/0/1.0 set security ike gateway hub-to-spoke-gw-2 ike-policy ike-policy-2 set security ike gateway hub-to-spoke-gw-2 dynamic distinguished-name wildcard OU=SBU set security ike gateway hub-to-spoke-gw-2 dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw-2 local-identity distinguished-name set security ike gateway hub-to-spoke-gw-2 external-interface ge-0/0/2.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy proposals ipsec-proposal set security ipsec vpn hub-to-spoke-vpn-1 bind-interface st0.0 set security ipsec vpn hub-to-spoke-vpn-1 ike gateway hub-to-spoke-gw-1 set security ipsec vpn hub-to-spoke-vpn-1 ike ipsec-policy vpn-policy set security ipsec vpn hub-to-spoke-vpn-2 bind-interface st0.1 set security ipsec vpn hub-to-spoke-vpn-2 ike gateway hub-to-spoke-gw-2 set security ipsec vpn hub-to-spoke-vpn-2 ike ipsec-policy vpn-policy set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces ge-0/0/2.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/3.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.1.1.1/30 user@host# set ge-0/0/2 unit 0 family inet address 10.1.2.1/30 user@host# set ge-0/0/3 unit 0 family inet address 10.50.50.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.1/24 user@host# set st0 unit 1 multipoint user@host# set st0 unit 1 family inet address 10.20.20.1/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface ge-0/0/3.0 user@host# set policy-statement lan_nw then accept user@host# set policy-statement load_balance then load-balance per-packet [edit protocols bgp] user@host# set group ibgp-1 type internal user@host# set group ibgp-1 local-address 10.10.10.1 user@host# set group ibgp-1 export lan_nw user@host# set group ibgp-1 cluster 10.2.3.4 user@host# set group ibgp-1 multipath user@host# set group ibgp-1 allow 10.10.10.0/24 user@host# set group ibgp-2 type internal user@host# set group ibgp-2 local-address 10.20.20.1 user@host# set group ibgp-2 export lan_nw user@host# set group ibgp-2 cluster 10.2.3.5 user@host# set group ibgp-2 multipath user@host# set group ibgp-2 allow 10.20.20.0/24 [edit routing-options] user@host# set static route 10.2.2.0/30 next-hop 10.1.1.2 user@host# set static route 10.3.3.0/30 next-hop 10.1.2.2 user@host# set autonomous-system 65010 user@host# set forwarding-table export load_balance
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy-1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike policy ike-policy-2] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local2 [edit security ike gateway hub-to-spoke-gw-1] user@host# set ike-policy ike-policy-1 user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/1.0 [edit security ike gateway hub-to-spoke-gw-2] user@host# set ike-policy ike-policy-2 user@host# set dynamic distinguished-name wildcard OU=SBU user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/2.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn hub-to-spoke-vpn-1] user@host# set bind-interface st0.0 user@host# set ike gateway hub-to-spoke-gw-1 user@host# set ike ipsec-policy vpn-policy [edit security ipsec vpn hub-to-spoke-vpn-2] user@host# set bind-interface st0.1 user@host# set ike gateway hub-to-spoke-gw-2 user@host# set ike ipsec-policy vpn-policy
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.0 user@host# set interfaces ge-0/0/1.0 user@host# set interfaces ge-0/0/2.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/3.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.1.1.1/30;
}
}
}
ge-0/0/2 {
unit 0 {
family inet {
address 10.1.2.1/30;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 10.50.50.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.1/24;
}
}
unit 1 {
multipoint;
family inet {
address 10.20.20.1/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement lan_nw {
from interface ge-0/0/3.0;
then accept;
}
policy-statement load_balance {
then {
load-balance per-packet;
}
}
[edit]
user@host# show protocols
bgp {
group ibgp-1 {
type internal;
local-address 10.10.10.1;
export lan_nw;
cluster 10.2.3.4;
multipath;
allow 10.10.10.0/24;
}
group ibgp-2 {
type internal;
local-address 10.20.20.1;
export lan_nw;
cluster 10.2.3.5;
multipath;
allow 10.20.20.0/24;
}
}
[edit]
user@host# show routing-options
static {
route 10.2.2.0/30 next-hop 10.1.1.2;
route 10.3.3.0/30 next-hop 10.1.2.2;
}
autonomous-system 65010;
forwarding-table {
export load_balance;
}
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy-1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
policy ike-policy-2 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local2;
}
}
gateway hub-to-spoke-gw-1 {
ike-policy ike-policy-1;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/1.0;
}
gateway hub-to-spoke-gw-2 {
ike-policy ike-policy-2;
dynamic {
distinguished-name {
wildcard OU=SBU;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/2.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn hub-to-spoke-vpn-1 {
bind-interface st0.0;
ike {
gateway hub-to-spoke-gw-1;
ipsec-policy vpn-policy;
}
}
vpn hub-to-spoke-vpn-2 {
bind-interface st0.1;
ike {
gateway hub-to-spoke-gw-2;
ipsec-policy vpn-policy;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.0;
ge-0/0/1.0;
ge-0/0/2.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/3.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces fe-0/0/1 unit 0 family inet address 10.2.2.1/30 set interfaces fe-0/0/2 unit 0 family inet address 10.3.3.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.60.60.1/24 set interfaces st0 unit 0 family inet address 10.10.10.2/24 set interfaces st0 unit 1 family inet address 10.20.20.2/24 set policy-options policy-statement lan_nw from interface fe-0/0/4.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp-1 type internal set protocols bgp group ibgp-1 local-address 10.10.10.2 set protocols bgp group ibgp-1 export lan_nw set protocols bgp group ibgp-1 neighbor 10.10.10.1 set protocols bgp group ibgp-2 type internal set protocols bgp group ibgp-2 local-address 10.20.20.2 set protocols bgp group ibgp-2 export lan_nw set protocols bgp group ibgp-2 neighbor 10.20.20.1 set routing-options static route 10.1.1.0/30 next-hop 10.2.2.2 set routing-options static route 10.1.2.0/30 next-hop 10.3.3.2 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy-1 mode main set security ike policy ike-policy-1 proposals ike-proposal set security ike policy ike-policy-1 certificate local-certificate Local1 set security ike policy ike-policy-2 mode main set security ike policy ike-policy-2 proposals ike-proposal set security ike policy ike-policy-2 certificate local-certificate Local2 set security ike gateway spoke-to-hub-gw-1 ike-policy ike-policy-1 set security ike gateway spoke-to-hub-gw-1 address 10.1.1.1 set security ike gateway spoke-to-hub-gw-1 local-identity distinguished-name set security ike gateway spoke-to-hub-gw-1 remote-identity distinguished-name set security ike gateway spoke-to-hub-gw-1 external-interface fe-0/0/1.0 set security ike gateway spoke-to-hub-gw-2 ike-policy ike-policy-2 set security ike gateway spoke-to-hub-gw-2 address 10.1.2.1 set security ike gateway spoke-to-hub-gw-2 local-identity distinguished-name set security ike gateway spoke-to-hub-gw-2 remote-identity distinguished-name set security ike gateway spoke-to-hub-gw-2 external-interface fe-0/0/2.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy proposals ipsec-proposal set security ipsec vpn spoke-to-hub-1 bind-interface st0.0 set security ipsec vpn spoke-to-hub-1 ike gateway spoke-to-hub-gw-1 set security ipsec vpn spoke-to-hub-1 ike ipsec-policy vpn-policy set security ipsec vpn spoke-to-hub-1 establish-tunnels immediately set security ipsec vpn spoke-to-hub-2 bind-interface st0.1 set security ipsec vpn spoke-to-hub-2 ike gateway spoke-to-hub-gw-2 set security ipsec vpn spoke-to-hub-2 ike ipsec-policy vpn-policy set security ipsec vpn spoke-to-hub-2 establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces fe-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces fe-0/0/2.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set fe-0/0/1 unit 0 family inet address 10.2.2.1/30 user@host# set fe-0/0/2 unit 0 family inet address 10.3.3.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.60.60.1/24 user@host# set st0 unit 0 family inet address 10.10.10.2/24 user@host# set st0 unit 1 family inet address 10.20.20.2/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface fe-0/0/4.0 user@host# set policy-statement lan_nw then accept [edit protocols bgp] user@host# set group ibgp-1 type internal user@host# set group ibgp-1 local-address 10.10.10.2 user@host# set group ibgp-1 export lan_nw user@host# set group ibgp-1 neighbor 10.10.10.1 user@host# set group ibgp-2 type internal user@host# set group ibgp-2 local-address 10.20.20.2 user@host# set group ibgp-2 export lan_nw user@host# set group ibgp-2 neighbor 10.20.20.1 [edit routing-options] user@host# set static route 10.1.1.0/30 next-hop 10.2.2.2 user@host# set static route 10.1.2.0/30 next-hop 10.3.3.2 user@host# set autonomous-system 65010
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy-1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike policy ike-policy-2] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local2 [edit security ike gateway spoke-to-hub-gw-1] user@host# set ike-policy ike-policy-1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/1.0 [edit security ike gateway spoke-to-hub-gw-2] user@host# set ike-policy ike-policy-2 user@host# set address 10.1.2.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/2.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub-1] user@host# set bind-interface st0.0 user@host# set ike gateway spoke-to-hub-gw-1 user@host# set ike ipsec-policy vpn-policy user@host# set establish-tunnels immediately [edit security ipsec vpn spoke-to-hub-2] user@host# set bind-interface st0.1 user@host# set ike gateway spoke-to-hub-gw-2 user@host# set ike ipsec-policy vpn-policy user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/1.0 user@host# set interfaces st0.0 user@host# set interfaces fe-0/0/2.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
fe-0/0/1 {
unit 0 {
family inet {
address 10.2.2.1/30;
}
}
}
fe-0/0/2 {
unit 0 {
family inet {
address 10.3.3.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.60.60.1/24;
}
}
}
st0 {
unit 0 {
family inet {
address 10.10.10.2/24;
}
}
unit 1 {
family inet {
address 10.20.20.2/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement lan_nw {
from interface fe-0/0/4.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp-1 {
type internal;
local-address 10.10.10.2;
export lan_nw;
neighbor 10.10.10.1;
}
group ibgp-2 {
type internal;
local-address 10.20.20.2;
export lan_nw;
neighbor 10.20.20.1;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.0/30 next-hop 10.2.2.2;
route 10.1.2.0/30 next-hop 10.3.3.2;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy-1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
policy ike-policy-2 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local2;
}
}
gateway spoke-to-hub-gw-1 {
ike-policy ike-policy-1;
address 1o.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/1.0;
}
gateway spoke-to-hub-gw-2 {
ike-policy ike-policy-2;
address 1o.1.2.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/2.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub-1 {
bind-interface st0.0;
ike {
gateway spoke-to-hub-gw-1;
ipsec-policy vpn-policy;
}
establish-tunnels immediately;
}
vpn spoke-to-hub-2 {
bind-interface st0.1;
ike {
gateway spoke-to-hub-gw-2;
ipsec-policy vpn-policy;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/1.0;
st0.0;
fe-0/0/2.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证 IKE 第 1 阶段状态
目的
验证 IKE 第 1 阶段状态。
操作
在操作模式下,输入 show security ike security-associations 命令。
user@host> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 3733049 UP bc9686796c2e52e9 1fbe46eee168f24e Main 10.2.2.1 3733048 UP a88db7ed23ec5f6b c88b81dff52617a5 Main 10.3.3.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 第 2 阶段状态
目的
验证 IPsec 第 2 阶段状态。
操作
在操作模式下,输入 security ipsec security-associations 命令。
user@host> security ipsec security-associations Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway <268173315 ESP:des/ md5 93cfb417 1152/ unlim - root 500 10.2.2.1 >268173315 ESP:des/ md5 101de6f7 1152/ unlim - root 500 10.2.2.1 <268173313 ESP:des/ md5 272e29c0 1320/ unlim - root 500 10.3.3.1 >268173313 ESP:des/ md5 a3bf8fad 1320/ unlim - root 500 10.3.3.1
意义
该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 10.10.10.2 st0.0 hub-to-spoke-vpn-1 Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 10.20.20.2 st0.1 hub-to-spoke-vpn-2 Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SBU, CN=spoke1_backup
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 BGP
目的
验证 BGP 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show bgp summary 命令。
user@host> show bgp summary Groups: 2 Peers: 2 Down peers: 0 Unconfigured peers: 2 Table Tot Paths Act Paths Suppressed History Damp State Pending inet.0 2 2 0 0 0 0 Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped... 10.10.10.2 65010 4819 4820 0 2 1d 12:15:14 1/1/1/0 0/0/0/0 10.20.20.2 65010 4926 4928 0 0 1d 13:03:03 1/1/1/0 0/0/0/0
验证学习的路由
目的
验证是否已获知到分支的路由。
操作
在操作模式下,输入 show route 10.60.60.0 detail 命令。
user@host> show route 10.60.60.0 detail
inet.0: 47 destinations, 48 routes (46 active, 0 holddown, 1 hidden)
10.60.60.0/24 (2 entries, 1 announced)
*BGP Preference: 170/-101
Next hop type: Indirect
Address: 0x167407c
Next-hop reference count: 3
Source: 10.10.10.2
Next hop type: Router
Next hop: 10.10.10.2 via st0.0
Next hop type: Router
Next hop: 10.20.20.2 via st0.1, selected
Protocol next hop: 10.10.10.2
Indirect next hop: 15c8000 262142
Protocol next hop: 10.20.20.2
Indirect next hop: 15c80e8 262143
State: <Act Int Ext>
Local AS: 65010 Peer AS: 65010
Age: 1d 12:16:25 Metric2: 0
Task: BGP_10.10.10.10.2+53120
Announcement bits (2): 0-KRT 3-Resolve tree 1
AS path: I
Accepted Multipath
Localpref: 100
Router ID: 10.207.36.182
BGP Preference: 170/-101
Next hop type: Indirect
Address: 0x15b8ac0
Next-hop reference count: 1
Source: 10.20.20.2
Next hop type: Router
Next hop: 10.20.20.2 via st0.1, selected
Protocol next hop: 10.20.20.2
Indirect next hop: 15c80e8 262143
State: <NotBest Int Ext>
Inactive reason: Not Best in its group - Update source
Local AS: 65010 Peer AS: 65010
Age: 1d 13:04:14 Metric2: 0
Task: BGP_10.20.20.20.2+50733
AS path: I
Accepted MultipathContrib
Localpref: 100
Router ID: 10.207.36.182
验证转发表中的路由安装
目的
验证转发表中是否已安装到分支的路由。
操作
在操作模式下,输入 show route forwarding-table matching 10.60.60.0 命令。
user@host> show route forwarding-table matching 60.60.60.0
Routing table: default.inet
Internet:
Destination Type RtRef Next hop Type Index NhRef Netif
10.60.60.0/24 user 0 ulst 262144 1
indr 262142 2
10.10.10.2 ucst 572 3 st0.0
indr 262143 2
10.20.20.2 ucst 573 3 st0.1
示例:使用 iBGP 和主动备份隧道配置 AutoVPN
此示例说明如何在 AutoVPN 中心和分支之间配置活动和备份 IPsec VPN 隧道。此示例将 iBGP 配置为使用基于证书的身份验证通过 VPN 隧道转发流量。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
两个受支持的 SRX 系列防火墙作为 AutoVPN 中心和分支防火墙
-
支持 AutoVPN 的 Junos OS 12.1X44-D10 及更高版本
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。
概述
此示例显示了具有两个 IPsec VPN 隧道的 AutoVPN 中心和分支的配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。证书在中心和每个 IPsec VPN 隧道的分支中注册。分支的其中一个证书在可分辨名称 (DN) 中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。分支的另一个证书在 DN 中包含 OU 值“SBU”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SBU”。
分支与中心建立 IPsec VPN 连接,从而允许它访问中心上的资源。在 AutoVPN 中心和分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 11 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
2 |
|
身份验证算法 |
SHA-1 |
|
加密算法 |
AES 128 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
身份验证算法 |
HMAC MD5 96 |
|
加密算法 |
加拿大广播公司 |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
14 |
在所有设备上配置相同的证书颁发机构 (CA)。
Junos OS 仅支持单级证书层次结构。
表 12 显示在中心和分支上配置的选项。
|
选项 |
枢纽 |
辐条 1 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
中心到辐射型 GW-1:动态 中心到辐射型 GW-2:动态 |
分支到集线器-GW-1:1 0.1.1.1 分支到集线器-GW-2:10.1.2.1 |
|
远程 IKE ID |
中心到辐射型 GW-1:分支证书上的 DN,OU 字段中有字符串 中心到辐射型 GW-2:分支证书上的 DN,OU 字段中有字符串 |
分支到集线器-GW-1:集线器证书上的 DN 分支到集线器-GW-2:集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
中心到辐射型 GW-1:ge-0/0/1.0 中心到辐射型 GW-2:ge-0/0/2.0 |
分支到集线器-GW-1:铁-0/0/1.0 分支到集线器-GW-2:铁-0/0/2.0 |
|
VPN: |
||
|
绑定接口 |
中心到辐射型 VPN-1:st0.0 中心到辐射型 VPN-2:st0.1 |
分支到集线器-1:st0.0 辐射到中枢-2:st0.1 |
|
VPN 监视器 |
中心到辐射型 VPN-1:ge-0/0/1.0(源接口) 中心到辐射型 VPN-2:ge-0/0/2.0(源接口) |
分支到集线器-1:10.1.1.1(目标 IP) 辐射到中枢-2:10.1.2.1(目标 IP) |
|
建立隧道 |
(未配置) |
配置提交后立即 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
拓扑学
图 5 显示了此示例中要为 AutoVPN 配置的 SRX 系列防火墙。
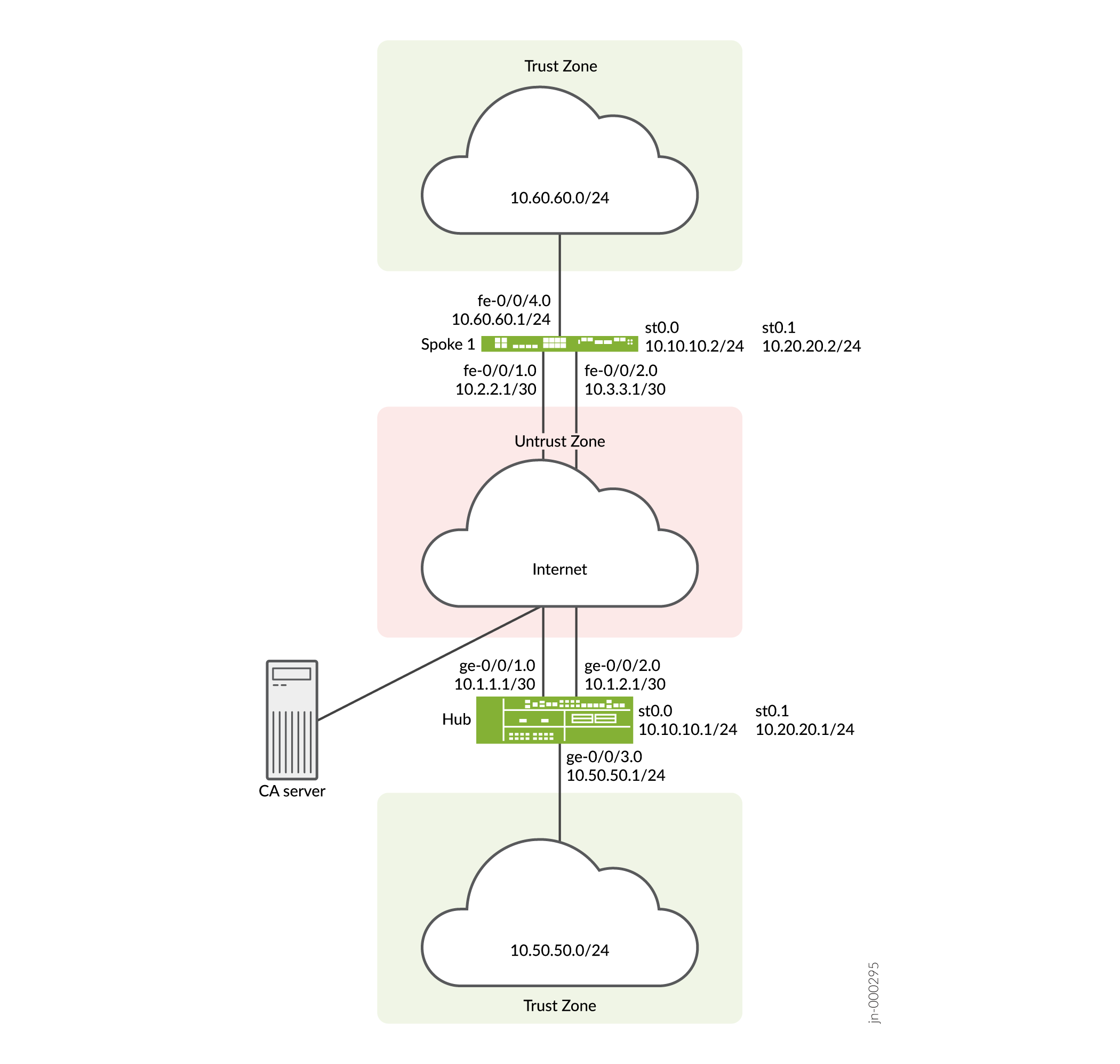
在此示例中,在中心和分支 1 之间建立了两个 IPsec VPN 隧道。路由信息通过每个隧道中的 iBGP 会话进行交换。到 10.60.60.0/24 的路由的最长前缀匹配是通过集线器上的 st0.0 接口。因此,路由的主隧道将通过中心辐射型 1 上的 st0.0 接口。默认路由是通过中心辐射型 1 上 st0.1 接口上的备份隧道。
VPN 监控会检查隧道的状态。如果主隧道出现问题(例如,无法访问远程隧道网关),隧道状态将更改为关闭,发往 10.60.60.0/24 的数据将通过备份隧道重新路由。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
为每个证书生成一个密钥对。
user@host> request security pki generate-key-pair certificate-id Local1 user@host> request security pki generate-key-pair certificate-id Local2
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password> user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local2 domain-name example.net email hub_backup@example.net ip-address 10.1.2.1 subject DC=example.net,CN=hub_backup,OU=SBU,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate certificate-id Local1 detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2012 09:39 Not after: 11- 6-2013 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not starteduser@host> show security pki local-certificate certificate-id Local2 detail Certificate identifier: Local2 Certificate version: 3 Serial number: 505efdf900000000259a Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SBU, Country: IN, State: KA, Locality: Bengaluru, Common name: hub_backup, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SBU, CN=hub_backup Alternate subject: "hub_backup@example.net", example.net, 10.1.2.1 Validity: Not before: 11- 9-2012 10:55 Not after: 11- 9-2013 11:05 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d5:44:08:96:f6:77:05:e6:91:50:8a:8a:2a 4e:95:43:1e:88:ea:43:7c:c5:ac:88:d7:a0:8d:b5:d9:3f:41:db:db 44:34:1f:56:a5:38:4b:b2:c5:85:f9:f1:bf:b2:7b:d4:b2:af:98:a0 95:50:02:ad:f5:dd:4d:dc:67:85:dd:84:09:df:9c:68:a5:58:65:e7 2c:72:cc:47:4b:d0:cc:4a:28:ca:09:db:ad:6e:5a:13:6c:e6:cc:f0 29:ed:2b:2d:d1:38:38:bc:68:84:de:ae:86:39:c9:dd:06:d5:36:f0 e6:2a:7b:46:4c:cd:a5:24:1c:e0:92:8d:ad:35:29:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 98:96:2f:ff:ca:af:33:ee:d7:4c:c8:4f:f7:71:53:c0:5d:5f:c5:59 (sha1) c9:87:e3:a4:5c:47:b5:aa:90:22:e3:06:b2:0b:e1:ea (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
为每个证书生成一个密钥对。
user@host> rrequest security pki generate-key-pair certificate-id Local1 user@host> request security pki generate-key-pair certificate-id Local2
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password> user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local2 domain-name example.net email spoke1_backup@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke1_backup,OU=SBU,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate certificate-id Local1 detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2012 09:40 Not after: 11- 6-2013 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started user@host> show security pki local-certificate certificate-id Local2 detail Certificate identifier: Local2 Certificate version: 3 Serial number: 506c3d0600000000259b Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SBU, Country: IN, State: KA, Locality: Mysore, Common name: spoke1_backup, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SBU, CN=spoke1_backup Alternate subject: "spoke1_backup@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 9-2012 11:09 Not after: 11- 9-2013 11:19 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:a7:02:b5:e2:cd:79:24:f8:97:a3:8d:4d:27 8c:2b:dd:f1:57:72:4d:2b:6d:d5:95:0d:9c:1b:5c:e2:a4:b0:84:2e 31:82:3c:91:08:a2:58:b9:30:4c:5f:a3:6b:e6:2b:9c:b1:42:dd:1c cd:a2:7a:84:ea:7b:a6:b7:9a:13:33:c6:27:2b:79:2a:b1:0c:fe:08 4c:a7:35:fc:da:4f:df:1f:cf:f4:ba:bc:5a:05:06:63:92:41:b4:f2 54:00:3f:ef:ff:41:e6:ca:74:10:56:f7:2b:5f:d3:1a:33:7e:49:74 1c:42:cf:c2:23:ea:4b:8f:50:2c:eb:1c:a6:37:89:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: d6:7f:52:a3:b6:f8:ae:cb:70:3f:a9:79:ea:8a:da:9e:ba:83:e4:5f (sha1) 76:0b:72:73:cf:51:ee:58:81:2d:f7:b4:e2:5c:f4:5c (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 适用于
SLT本地 1 和SBU本地 2。中心位置上的 IKE 配置包括OU=SLT和OU=SBU用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.1.1.1/30 set interfaces ge-0/0/2 unit 0 family inet address 10.1.2.1/30 set interfaces ge-0/0/3 unit 0 family inet address 10.50.50.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.1/24 set interfaces st0 unit 1 multipoint set interfaces st0 unit 1 family inet address 10.20.20.1/24 set policy-options policy-statement lan_nw from interface ge-0/0/3.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp-1 type internal set protocols bgp group ibgp-1 local-address 10.10.10.1 set protocols bgp group ibgp-1 export lan_nw set protocols bgp group ibgp-1 cluster 10.2.3.4 set protocols bgp group ibgp-1 allow 10.10.10.0/24 set protocols bgp group ibgp-2 type internal set protocols bgp group ibgp-2 local-address 10.20.20.1 set protocols bgp group ibgp-2 export lan_nw set protocols bgp group ibgp-2 cluster 10.2.3.5 set protocols bgp group ibgp-2 allow 10.20.20.0/24 set routing-options static route 10.2.2.0/30 next-hop 10.1.1.2 set routing-options static route 10.3.3.0/30 next-hop 10.1.2.2 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy-1 mode main set security ike policy ike-policy-1 proposals ike-proposal set security ike policy ike-policy-1 certificate local-certificate Local1 set security ike policy ike-policy-2 mode main set security ike policy ike-policy-2 proposals ike-proposal set security ike policy ike-policy-2 certificate local-certificate Local2 set security ike gateway hub-to-spoke-gw-1 ike-policy ike-policy-1 set security ike gateway hub-to-spoke-gw-1 dynamic distinguished-name wildcard OU=SLT set security ike gateway hub-to-spoke-gw-1 dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw-1 local-identity distinguished-name set security ike gateway hub-to-spoke-gw-1 external-interface ge-0/0/1.0 set security ike gateway hub-to-spoke-gw-2 ike-policy ike-policy-2 set security ike gateway hub-to-spoke-gw-2 dynamic distinguished-name wildcard OU=SBU set security ike gateway hub-to-spoke-gw-2 dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw-2 local-identity distinguished-name set security ike gateway hub-to-spoke-gw-2 external-interface ge-0/0/2.0 set security ipsec vpn-monitor-options interval 5 set security ipsec vpn-monitor-options threshold 2 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy proposals ipsec-proposal set security ipsec vpn hub-to-spoke-vpn-1 bind-interface st0.0 set security ipsec vpn hub-to-spoke-vpn-1 vpn-monitor source-interface ge-0/0/1.0 set security ipsec vpn hub-to-spoke-vpn-1 ike gateway hub-to-spoke-gw-1 set security ipsec vpn hub-to-spoke-vpn-1 ike ipsec-policy vpn-policy set security ipsec vpn hub-to-spoke-vpn-2 bind-interface st0.1 set security ipsec vpn hub-to-spoke-vpn-2 vpn-monitor source-interface ge-0/0/2.0 set security ipsec vpn hub-to-spoke-vpn-2 ike gateway hub-to-spoke-gw-2 set security ipsec vpn hub-to-spoke-vpn-2 ike ipsec-policy vpn-policy set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces ge-0/0/2.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/3.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.1.1.1/30 user@host# set ge-0/0/2 unit 0 family inet address 10.1.2.1/30 user@host# set ge-0/0/3 unit 0 family inet address 10.50.50.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.1/24 user@host# set st0 unit 1 multipoint user@host# set st0 unit 1 family inet address 10.20.20.1/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement lan_nw from interface ge-0/0/3.0 user@host# set policy-statement lan_nw then accept [edit protocols bgp] user@host# set group ibgp-1 type internal user@host# set group ibgp-1 local-address 10.10.10.1 user@host# set group ibgp-1 export lan_nw user@host# set group ibgp-1 cluster 10.2.3.4 user@host# set group ibgp-1 allow 10.10.10.0/24 user@host# set group ibgp-2 type internal user@host# set group ibgp-2 local-address 10.20.20.1 user@host# set group ibgp-2 export lan_nw user@host# set group ibgp-2 cluster 10.2.3.5 user@host# set group ibgp-2 allow 10.20.20.0/24 [edit routing-options] user@host# set static route 10.2.2.0/30 next-hop 10.1.1.2 user@host# set static route 10.3.3.0/30 next-hop 10.1.2.2 user@host# set autonomous-system 65010
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy-1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike policy ike-policy-2] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local2 [edit security ike gateway hub-to-spoke-gw-1] user@host# set ike-policy ike-policy-1 user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/1.0 [edit security ike gateway hub-to-spoke-gw-2] user@host# set ike-policy ike-policy-2 user@host# set dynamic distinguished-name wildcard OU=SBU user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/2.0
-
配置第 2 阶段选项。
[edit security ipsec vpn-monitor] user@host# set options interval 5 user@host# set options threshold 2 [edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn hub-to-spoke-vpn-1] user@host# set bind-interface st0.0 user@host# set vpn-monitor source-interface ge-0/0/1.0 user@host# set ike gateway hub-to-spoke-gw-1 user@host# set ike ipsec-policy vpn-policy [edit security ipsec vpn hub-to-spoke-vpn-2] user@host# set bind-interface st0.1 user@host# set vpn-monitor source-interface ge-0/0/2.0 user@host# set ike gateway hub-to-spoke-gw-2 user@host# set ike ipsec-policy vpn-policy
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.0 user@host# set interfaces ge-0/0/1.0 user@host# set interfaces ge-0/0/2.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/3.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.1.1.1/30;
}
}
}
ge-0/0/2 {
unit 0 {
family inet {
address 10.1.2.1/30;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 10.50.50.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.1/24;
}
}
unit 1 {
multipoint;
family inet {
address 10.20.20.1/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement lan_nw {
from interface ge-0/0/3.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp-1 {
type internal;
local-address 10.10.10.1;
export lan_nw;
cluster 10.2.3.4;
allow 10.10.10.0/24;
}
group ibgp-2 {
type internal;
local-address 10.20.20.1;
export lan_nw;
cluster 10.2.3.5;
allow 10.20.20.0/24;
}
}
[edit]
user@host# show routing-options
static {
route 10.2.2.0/30 next-hop 10.1.1.2;
route 10.3.3.0/30 next-hop 10.1.2.2;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy-1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
policy ike-policy-2 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local2;
}
}
gateway hub-to-spoke-gw-1 {
ike-policy ike-policy-1;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/1.0;
}
gateway hub-to-spoke-gw-2 {
ike-policy ike-policy-2;
dynamic {
distinguished-name {
wildcard OU=SBU;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/2.0;
}
[edit]
user@host# show security ipsec
vpn-monitor-options {
interval 5;
threshold 2;
}
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn hub-to-spoke-vpn-1 {
bind-interface st0.0;
vpn-monitor {
source-interface ge-0/0/1.0;
}
ike {
gateway hub-to-spoke-gw-1;
ipsec-policy vpn-policy;
}
}
vpn hub-to-spoke-vpn-2 {
bind-interface st0.1;
vpn-monitor {
source-interface ge-0/0/2.0;
}
ike {
gateway hub-to-spoke-gw-2;
ipsec-policy vpn-policy;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.0;
ge-0/0/1.0;
ge-0/0/2.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/3.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces fe-0/0/1 unit 0 family inet address 10.2.2.1/30 set interfaces fe-0/0/2 unit 0 family inet address 10.3.3.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.60.60.1/24 set interfaces st0 unit 0 family inet address 10.10.10.2/24 set interfaces st0 unit 1 family inet address 10.20.20.2/24 set policy-options policy-statement default_route from protocol static set policy-options policy-statement default_route from route-filter 0.0.0.0/0 exact set policy-options policy-statement default_route then accept set policy-options policy-statement lan_nw from interface fe-0/0/4.0 set policy-options policy-statement lan_nw then accept set protocols bgp group ibgp-1 type internal set protocols bgp group ibgp-1 local-address 10.10.10.2 set protocols bgp group ibgp-1 export lan_nw set protocols bgp group ibgp-1 neighbor 10.10.10.1 set protocols bgp group ibgp-2 type internal set protocols bgp group ibgp-2 local-address 10.20.20.2 set protocols bgp group ibgp-2 export default_route set protocols bgp group ibgp-2 neighbor 10.20.20.1 set routing-options static route 10.1.1.0/30 next-hop 10.2.2.2 set routing-options static route 10.1.2.0/30 next-hop 10.3.3.2 set routing-options static route 0.0.0.0/0 next-hop st0.1 set routing-options autonomous-system 65010 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy-1 mode main set security ike policy ike-policy-1 proposals ike-proposal set security ike policy ike-policy-1 certificate local-certificate Local1 set security ike policy ike-policy-2 mode main set security ike policy ike-policy-2 proposals ike-proposal set security ike policy ike-policy-2 certificate local-certificate Local2 set security ike gateway spoke-to-hub-gw-1 ike-policy ike-policy-1 set security ike gateway spoke-to-hub-gw-1 address 10.1.1.1 set security ike gateway spoke-to-hub-gw-1 local-identity distinguished-name set security ike gateway spoke-to-hub-gw-1 remote-identity distinguished-name set security ike gateway spoke-to-hub-gw-1 external-interface fe-0/0/1.0 set security ike gateway spoke-to-hub-gw-2 ike-policy ike-policy-2 set security ike gateway spoke-to-hub-gw-2 address 10.1.2.1 set security ike gateway spoke-to-hub-gw-2 local-identity distinguished-name set security ike gateway spoke-to-hub-gw-2 remote-identity distinguished-name set security ike gateway spoke-to-hub-gw-2 external-interface fe-0/0/2.0 set security ipsec vpn-monitor-options interval 5 set security ipsec vpn-monitor-options threshold 2 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy proposals ipsec-proposal set security ipsec vpn spoke-to-hub-1 bind-interface st0.0 set security ipsec vpn spoke-to-hub-1 vpn-monitor destination-ip 10.1.1.1 set security ipsec vpn spoke-to-hub-1 ike gateway spoke-to-hub-gw-1 set security ipsec vpn spoke-to-hub-1 ike ipsec-policy vpn-policy set security ipsec vpn spoke-to-hub-1 establish-tunnels immediately set security ipsec vpn spoke-to-hub-2 bind-interface st0.1 set security ipsec vpn spoke-to-hub-2 vpn-monitor destination-ip 10.1.2.1 set security ipsec vpn spoke-to-hub-2 ike gateway spoke-to-hub-gw-2 set security ipsec vpn spoke-to-hub-2 ike ipsec-policy vpn-policy set security ipsec vpn spoke-to-hub-2 establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces fe-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces fe-0/0/2.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set fe-0/0/1 unit 0 family inet address 10.2.2.1/30 user@host# set fe-0/0/2 unit 0 family inet address 10.3.3.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.60.60.1/24 user@host# set st0 unit 0 family inet address 10.10.10.2/24 user@host# set st0 unit 1 family inet address 10.20.20.2/24
-
配置路由协议。
[edit policy-options] user@host# set policy-statement default_route from protocol static user@host# set policy-statement default_route from route-filter 0.0.0.0/0 exact user@host# set policy-statement default_route then accept user@host# set policy-statement lan_nw from interface fe-0/0/4.0 user@host# set policy-statement lan_nw then accept [edit protocols bgp] user@host# set group ibgp-1 type internal user@host# set group ibgp-1 local-address 10.10.10.2 user@host# set group ibgp-1 export lan_nw user@host# set group ibgp-1 neighbor 10.10.10.1 user@host# set group ibgp-2 type internal user@host# set group ibgp-2 local-address 10.20.20.2 user@host# set group ibgp-2 export default_route user@host# set group ibgp-2 neighbor 10.20.20.1 [edit routing-options] user@host# set static route 10.1.1.0/30 next-hop 10.2.2.2 user@host# set static route 10.1.2.0/30 next-hop 10.3.3.2 user@host# set static route 0.0.0.0/0 next-hop st0.1 user@host# set autonomous-system 65010
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy-1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike policy ike-policy-2] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local2 [edit security ike gateway spoke-to-hub-gw-1] user@host# set ike-policy ike-policy-1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/1.0 [edit security ike gateway spoke-to-hub-gw-2] user@host# set ike-policy ike-policy-2 user@host# set address 10.1.2.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/2.0
-
配置第 2 阶段选项。
[edit security ipsec vpn-monitor] user@host# set options interval 5 user@host# set options threshold 2 [edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub-1] user@host# set bind-interface st0.0 user@host# set vpn-monitor destination-ip 10.1.1.1 user@host# set ike gateway spoke-to-hub-gw-1 user@host# set ike ipsec-policy vpn-policy user@host# set establish-tunnels immediately [edit security ipsec vpn spoke-to-hub-2] user@host# set bind-interface st0.1 user@host# set vpn-monitor destination-ip 10.1.2.1 user@host# set ike gateway spoke-to-hub-gw-2 user@host# set ike ipsec-policy vpn-policy user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/1.0 user@host# set interfaces st0.0 user@host# set interfaces fe-0/0/2.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show policy-options、 show security ipsecshow protocolsshow security ikeshow security zonesshow routing-optionsshow security policies和show security pki命令来确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
fe-0/0/1 {
unit 0 {
family inet {
address 10.2.2.1/30;
}
}
}
fe-0/0/2 {
unit 0 {
family inet {
address 10.3.3.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.60.60.1/24;
}
}
}
st0 {
unit 0 {
family inet {
address 10.10.10.2/24;
}
}
unit 1 {
family inet {
address 10.20.20.2/24;
}
}
}
[edit]
user@host# show policy-options
policy-statement default_route {
from {
protocol static;
route-filter 0.0.0.0/0 exact;
}
then accept;
}
policy-statement lan_nw {
from interface fe-0/0/4.0;
then accept;
}
[edit]
user@host# show protocols
bgp {
group ibgp-1 {
type internal;
local-address 10.10.10.2;
export lan_nw;
neighbor 10.10.10.1;
}
group ibgp-2 {
type internal;
local-address 10.20.20.2;
export default_route;
neighbor 10.20.20.1;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.0/30 next-hop 10.2.2.2;
route 10.1.2.0/30 next-hop 10.3.3.2;
route 0.0.0.0/0 next-hop st0.1;
}
autonomous-system 65010;
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy-1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
policy ike-policy-2 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local2;
}
}
gateway spoke-to-hub-gw-1 {
ike-policy ike-policy-1;
address 10.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/1.0;
}
gateway spoke-to-hub-gw-2 {
ike-policy ike-policy-2;
address 10.1.2.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/2.0;
}
[edit]
user@host# show security ipsec
vpn-monitor-options {
interval 5;
threshold 2;
}
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub-1 {
bind-interface st0.0;
vpn-monitor {
destination-ip 10.1.1.1;
}
ike {
gateway spoke-to-hub-gw-1;
ipsec-policy vpn-policy;
}
establish-tunnels immediately;
}
vpn spoke-to-hub-2 {
bind-interface st0.1;
vpn-monitor {
destination-ip 10.1.2.1;
}
ike {
gateway spoke-to-hub-gw-2;
ipsec-policy vpn-policy;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/1.0;
st0.0;
fe-0/0/2.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
- 验证 IKE 第 1 阶段状态(两个隧道均已启动)
- 验证 IPsec 第 2 阶段状态(两个隧道均已启动)
- 验证 IPsec 下一跳隧道(两个隧道均已启动)
- 验证 BGP(两条隧道均已启动)
- 验证获知的路由(两个隧道都已启动)
- 验证 IKE 第 1 阶段状态(主隧道已关闭)
- 验证 IPsec 第 2 阶段状态(主隧道已关闭)
- 验证 IPsec 下一跳隧道(主隧道已关闭)
- 验证 BGP(主隧道已关闭)
- 验证获知的路由(主隧道已关闭)
验证 IKE 第 1 阶段状态(两个隧道均已启动)
目的
当两个 IPSec VPN 隧道都启动时,验证 IKE 第 1 阶段状态。
操作
在操作模式下,输入 show security ike security-associations 命令。
user@host> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 3733075 UP d4f51c28c0a82101 05b125993a864d3c Main 10.3.3.1 3733076 UP d53c8a0b7d4c319b c23c5f7a26388247 Main 10.2.2.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 第 2 阶段状态(两个隧道均已启动)
目的
当两个 IPsec VPN 隧道都已启动时,验证 IPsec 第 2 阶段状态。
操作
在操作模式下,输入 security ipsec security-associations 命令。
user@host> security ipsec security-associations Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway <268173316 ESP:des/ md5 3cd96946 3555/ unlim U root 500 10.2.2.1 >268173316 ESP:des/ md5 1c09b9b 3555/ unlim U root 500 10.2.2.1 <268173313 ESP:des/ md5 7c6ffca3 3340/ unlim U root 500 10.3.3.1 >268173313 ESP:des/ md5 33bf6f2f 3340/ unlim U root 500 10.3.3.1
意义
该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道(两个隧道均已启动)
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 10.10.10.2 st0.0 hub-to-spoke-vpn-1 Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 10.20.20.2 st0.1 hub-to-spoke-vpn-2 Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SBU, CN=spoke1_backup
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 BGP(两条隧道均已启动)
目的
验证当两个 IPsec VPN 隧道都启动时,BGP 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show bgp summary 命令。
user@host> show bgp summary Groups: 2 Peers: 2 Down peers: 0 Unconfigured peers: 2 Table Tot Paths Act Paths Suppressed History Damp State Pending inet.0 2 2 0 0 0 0 Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped... 10.10.10.2 65010 5 6 0 0 54 1/1/1/0 0/0/0/0 10.20.20.2 65010 13 16 0 0 4:29 1/1/1/0 0/0/0/0
验证获知的路由(两个隧道都已启动)
目的
验证当两个隧道都启动时,是否已获知到分支的路由。到 10.60.60.0/24 的路由通过 st0.0 接口,默认路由通过 st0.1 接口。
操作
在操作模式下,输入 show route 10.60.60.0 命令。
user@host> show route 10.60.60.0
inet.0: 48 destinations, 48 routes (47 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
60.60.60.0/24 *[BGP/170] 00:01:11, localpref 100
AS path: I
> to 10.10.10.2 via st0.0
在操作模式下,输入 show route 0.0.0.0 命令。
user@host> show route 0.0.0.0
inet.0: 48 destinations, 48 routes (47 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
0.0.0.0/0 *[BGP/170] 00:04:55, localpref 100
AS path: I
> to 10.20.20.2 via st0.1
验证 IKE 第 1 阶段状态(主隧道已关闭)
目的
当主隧道关闭时,验证 IKE 第 1 阶段状态。
操作
在操作模式下,输入 show security ike security-associations 命令。
user@host> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 3733075 UP d4f51c28c0a82101 05b125993a864d3c Main 10.3.3.1 3733076 UP d53c8a0b7d4c319b c23c5f7a26388247 Main 10.2.2.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 第 2 阶段状态(主隧道已关闭)
目的
当主隧道关闭时,验证 IPsec 第 2 阶段状态。
操作
在操作模式下,输入 security ipsec security-associations 命令。
user@host> security ipsec security-associations Total active tunnels: 1 ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway <268173313 ESP:des/ md5 7c6ffca3 3156/ unlim U root 500 10.3.3.1 >268173313 ESP:des/ md5 33bf6f2f 3156/ unlim U root 500 10.3.3.1
意义
该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道(主隧道已关闭)
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 10.20.20.2 st0.1 hub-to-spoke-vpn-2 Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SBU, CN=spoke1_backup
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联,在本例中为备份 VPN 隧道。
验证 BGP(主隧道已关闭)
目的
验证当主隧道关闭时,BGP 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show bgp summary 命令。
user@host> show bgp summary Groups: 2 Peers: 1 Down peers: 0 Unconfigured peers: 1 Table Tot Paths Act Paths Suppressed History Damp State Pending inet.0 1 1 0 0 0 0 Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped... 10.20.20.2 10 20 24 0 0 7:24 1/1/1/0 0/0/0/0
验证获知的路由(主隧道已关闭)
目的
验证在主隧道关闭时是否已获知到分支的路由。到 10.60.60.0/24 的路由和默认路由都通过 st0.1 接口。
操作
在操作模式下,输入 show route 10.60.60.0 命令。
user@host> show route 60.60.60.0
inet.0: 46 destinations, 46 routes (45 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
0.0.0.0/0 *[BGP/170] 00:07:41, localpref 100
AS path: I
> to 10.20.20.2 via st0.1
在操作模式下,输入 show route 0.0.0.0 命令。
user@host> show route 0.0.0.0
inet.0: 46 destinations, 46 routes (45 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
0.0.0.0/0 *[BGP/170] 00:07:47, localpref 100
AS path: I
> to 10.20.20.2 via st0.1
示例:使用 OSPF 配置基本 AutoVPN
此示例说明如何将 AutoVPN 中心配置为充当单个终结点,然后将两个分支配置为充当到远程站点的隧道。此示例将 OSPF 配置为使用基于证书的身份验证通过 VPN 隧道转发数据包。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
三个受支持的 SRX 系列防火墙作为 AutoVPN 中心和分支
-
支持 AutoVPN 的 Junos OS 12.1X44-D10 及更高版本
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。
概述
此示例显示了 AutoVPN 中心的配置以及两个分支的后续配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。分支的证书在主题字段中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。
分支与中心建立 IPsec VPN 连接,使它们能够相互通信以及访问中心上的资源。在 AutoVPN 中心和所有分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 13 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
2 |
|
身份验证算法 |
SHA-1 |
|
加密算法 |
AES 128 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
身份验证算法 |
HMAC MD5 96 |
|
加密算法 |
加拿大广播公司 |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
14 |
在所有设备上配置相同的证书颁发机构 (CA)。
Junos OS 仅支持单级证书层次结构。
表 14 显示在中心和所有辐射上配置的选项。
|
选项 |
枢纽 |
所有辐条 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
动态 |
1 0.1.1.1 |
|
远程 IKE ID |
分支证书上的可分辨名称 (DN),组织单位 (OU) 字段中的字符串 |
集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
ge-0/0/1.0 |
辐条1:铁-0/0/1.0 辐条2:ge-0/0/1.0 |
|
VPN: |
||
|
绑定接口 |
st0.0 |
st0.0 |
|
建立隧道 |
(未配置) |
配置提交后立即 |
表 15 显示了每个分支上不同的配置选项。
|
选项 |
辐条 1 |
辐条 2 |
|---|---|---|
|
ST0.0 接口 |
10.10.10.2/24 |
10.10.10.3/24 |
|
与内部网络的接口 |
fe-0.0/4.0:100.60.60.1/24 |
fe-0.0/4.0:10.70.70.1/24 |
|
互联网接口 |
fe-0/0/1.0:10.2.2.1/30 |
ge-0/0/1.0:10.3.3.1/30 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2012 09:39 Not after: 11- 6-2013 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2012 09:40 Not after: 11- 6-2013 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
分步过程
要使用分支 2 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke2@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke2,OU=SLT,O=example,L=Tumkur,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40bb71d400000000258f Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Tumkur, Common name: spoke2, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2 Alternate subject: "spoke2@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 6-2012 10:02 Not after: 11- 6-2013 10:12 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:b6:2e:e2:da:e6:ac:57:e4:5d:ff:de:f6:89 27:d6:3e:1b:4a:3f:b2:2d:b3:d3:61:ed:ed:6a:07:d9:8a:d2:24:03 77:1a:fe:84:e1:12:8a:2d:63:6e:bf:02:6b:15:96:5a:4f:37:a0:46 44:09:96:c0:fd:bb:ab:79:2c:5d:92:bd:31:f0:3b:29:51:ce:89:8e 7c:2b:02:d0:14:5b:0a:a9:02:93:21:ea:f9:fc:4a:e7:08:bc:b1:6d 7c:f8:3e:53:58:8e:f1:86:13:fe:78:b5:df:0b:8e:53:00:4a:46:11 58:4a:38:e9:82:43:d8:25:47:7d:ef:18:f0:ef:a7:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 1a:6d:77:ac:fd:94:68:ce:cf:8a:85:f0:39:fc:e0:6b:fd:fe:b8:66 (sha1) 00:b1:32:5f:7b:24:9c:e5:02:e6:72:75:9e:a5:f4:77 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.1.1.1/30 set interfaces ge-0/0/3 unit 0 family inet address 10.50.50.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.1/24 set protocols ospf area 0.0.0.0 interface st0.0 interface-type p2mp set protocols ospf area 0.0.0.0 interface st0.0 dynamic-neighbors set protocols ospf area 0.0.0.0 interface ge-0/0/3.0 set routing-options static route 10.2.2.0/30 next-hop 10.1.1.2 set routing-options static route 10.3.3.0/30 next-hop 10.1.1.2 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway hub-to-spoke-gw ike-policy ike-policy1 set security ike gateway hub-to-spoke-gw dynamic distinguished-name wildcard OU=SLT set security ike gateway hub-to-spoke-gw dynamic ike-user-type group-ike-id set security ike gateway hub-to-spoke-gw local-identity distinguished-name set security ike gateway hub-to-spoke-gw external-interface ge-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn hub-to-spoke-vpn bind-interface st0.0 set security ipsec vpn hub-to-spoke-vpn ike gateway hub-to-spoke-gw set security ipsec vpn hub-to-spoke-vpn ike ipsec-policy vpn-policy1 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces st0.0 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/3.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.1.1.1/30 user@host# set ge-0/0/3 unit 0 family inet address 10.50.50.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.1/24
-
配置路由协议。
[edit protocols ospf] user@host# set area 0.0.0.0 interface st0.0 interface-type p2mp user@host# set area 0.0.0.0 interface st0.0 dynamic-neighbors user@host# set area 0.0.0.0 interface ge-0/0/3.0 [edit routing-options] user@host# set static route 2.2.2.0/30 next-hop 10.1.1.2 user@host# set static route 3.3.3.0/30 next-hop 10.1.1.2
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway hub-to-spoke-gw] user@host# set ike-policy ike-policy1 user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn hub-to-spoke-vpn] user@host# set bind-interface st0.0 user@host# set ike gateway hub-to-spoke-gw user@host# set ike ipsec-policy vpn-policy1
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/3.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.1.1.1/30;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 10.50.50.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.1/24;
}
}
}
[edit]
user@host# show protocols
ospf {
area 0.0.0.0 {
interface st0.0 {
interface-type p2mp;
dynamic-neighbors;
}
interface ge-0/0/3.0;
}
}
[edit]
user@host# show routing-options
static {
route 10.2.2.0/30 next-hop 10.1.1.2;
route 10.3.3.0/30 next-hop 10.1.1.2;
}
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway hub-to-spoke-gw {
ike-policy ike-policy1;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
ike-user-type group-ike-id;
}
local-identity distinguished-name;
external-interface ge-0/0/1.0;
}
[edit]
user@host# show security ipsec
traceoptions {
flag all;
}
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn hub-to-spoke-vpn {
bind-interface st0.0;
ike {
gateway hub-to-spoke-gw;
ipsec-policy vpn-policy1;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.0;
ge-0/0/1.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/3.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces fe-0/0/1 unit 0 family inet address 10.2.2.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.60.60.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.2/24 set protocols ospf area 0.0.0.0 interface st0.0 interface-type p2mp set protocols ospf area 0.0.0.0 interface st0.0 neighbor 10.10.10.1 set protocols ospf area 0.0.0.0 interface fe-0/0/4.0 set routing-options static route 10.1.1.0/30 next-hop 10.2.2.2 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway spoke-to-hub-gw ike-policy ike-policy1 set security ike gateway spoke-to-hub-gw address 10.1.1.1 set security ike gateway spoke-to-hub-gw local-identity distinguished-name set security ike gateway spoke-to-hub-gw remote-identity distinguished-name set security ike gateway spoke-to-hub-gw external-interface fe-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn spoke-to-hub bind-interface st0.0 set security ipsec vpn spoke-to-hub ike gateway spoke-to-hub-gw set security ipsec vpn spoke-to-hub ike ipsec-policy vpn-policy1 set security ipsec vpn spoke-to-hub establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces fe-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set fe-0/0/1 unit 0 family inet address 10.2.2.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.60.60.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.2/24
-
配置路由协议。
[edit protocols ospf] user@host# set area 0.0.0.0 interface st0.0 interface-type p2mp user@host# set area 0.0.0.0 interface st0.0 neighbor 10.10.10.1 user@host# set area 0.0.0.0 interface fe-0/0/4.0 [edit routing-options] user@host# set static route 10.1.1.0/30 next-hop 10.2.2.2
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway spoke-to-hub-gw] user@host# set ike-policy ike-policy1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface fe-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub] user@host# set bind-interface st0.0 user@host# set ike gateway spoke-to-hub-gw user@host# set ike ipsec-policy vpn-policy1 user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
fe-0/0/1 {
unit 0 {
family inet {
address 10.2.2.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.60.60.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.2/24;
}
}
}
[edit]
user@host# show protocols
ospf {
area 0.0.0.0 {
interface st0.0 {
interface-type p2mp;
neighbor 10.10.10.1;
}
interface fe-0/0/4.0;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.0/30 next-hop 10.2.2.2;
}
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway spoke-to-hub-gw {
ike-policy ike-policy1;
address 10.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface fe-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub {
bind-interface st0.0;
ike {
gateway spoke-to-hub-gw;
ipsec-policy vpn-policy1;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/1.0;
st0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 2
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.3.3.1/30 set interfaces fe-0/0/4 unit 0 family inet address 10.70.70.1/24 set interfaces st0 unit 0 multipoint set interfaces st0 unit 0 family inet address 10.10.10.3/24 set protocols ospf area 0.0.0.0 interface st0.0 interface-type p2mp set protocols ospf area 0.0.0.0 interface st0.0 neighbor 10.10.10.1 set protocols ospf area 0.0.0.0 interface fe-0/0/4.0 set routing-options static route 10.1.1.1/32 next-hop 10.3.3.2 set security ike proposal ike-proposal authentication-method rsa-signatures set security ike proposal ike-proposal dh-group group2 set security ike proposal ike-proposal authentication-algorithm sha1 set security ike proposal ike-proposal encryption-algorithm aes-128-cbc set security ike policy ike-policy1 mode main set security ike policy ike-policy1 proposals ike-proposal set security ike policy ike-policy1 certificate local-certificate Local1 set security ike gateway spoke-to-hub-gw ike-policy ike-policy1 set security ike gateway spoke-to-hub-gw address 10.1.1.1 set security ike gateway spoke-to-hub-gw local-identity distinguished-name set security ike gateway spoke-to-hub-gw remote-identity distinguished-name set security ike gateway spoke-to-hub-gw external-interface ge-0/0/1.0 set security ipsec proposal ipsec-proposal protocol esp set security ipsec proposal ipsec-proposal authentication-algorithm hmac-md5-96 set security ipsec proposal ipsec-proposal encryption-algorithm des-cbc set security ipsec policy vpn-policy1 perfect-forward-secrecy keys group14 set security ipsec policy vpn-policy1 proposals ipsec-proposal set security ipsec vpn spoke-to-hub bind-interface st0.0 set security ipsec vpn spoke-to-hub ike gateway spoke-to-hub-gw set security ipsec vpn spoke-to-hub ike ipsec-policy vpn-policy1 set security ipsec vpn spoke-to-hub establish-tunnels immediately set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces st0.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces fe-0/0/4.0 set security policies default-policy permit-all set security pki ca-profile ca-profile1 ca-identity ca-profile1 set security pki ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll set security pki ca-profile ca-profile1 revocation-check disable
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 2:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.3.3.1/30 user@host# set fe-0/0/4 unit 0 family inet address 10.70.70.1/24 user@host# set st0 unit 0 multipoint user@host# set st0 unit 0 family inet address 10.10.10.3/24
-
配置路由协议。
[edit protocols ospf] user@host# set area 0.0.0.0 interface st0.0 interface-type p2mp user@host# set area 0.0.0.0 interface st0.0 neighbor 10.10.10.1 user@host# set area 0.0.0.0 interface fe-0/0/4.0 [edit routing-options] user@host# set static route 10.1.1.1/32 next-hop 10.3.3.2
-
配置第 1 阶段选项。
[edit security ike proposal ike-proposal] user@host# set authentication-method rsa-signatures user@host# set dh-group group2 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-128-cbc [edit security ike policy ike-policy1] user@host# set mode main user@host# set proposals ike-proposal user@host# set certificate local-certificate Local1 [edit security ike gateway spoke-to-hub-gw] user@host# set ike-policy ike-policy1 user@host# set address 10.1.1.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name user@host# set external-interface ge-0/0/1.0
-
配置第 2 阶段选项。
[edit security ipsec proposal ipsec-proposal] user@host# set protocol esp user@host# set authentication-algorithm hmac-md5-96 user@host# set encryption-algorithm des-cbc [edit security ipsec policy vpn-policy1] user@host# set perfect-forward-secrecy keys group14 user@host# set proposals ipsec-proposal [edit security ipsec vpn spoke-to-hub] user@host# set bind-interface st0.0 user@host# set ike gateway spoke-to-hub-gw user@host# set ike ipsec-policy vpn-policy1 user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/1.0 user@host# set interfaces st0.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces fe-0/0/4.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ca-profile1 ca-identity ca-profile1 user@host# set ca-profile ca-profile1 enrollment url http://pc4/certsrv/mscep/mscep.dll user@host# set ca-profile ca-profile1 revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.3.3.1/30;
}
}
}
fe-0/0/4 {
unit 0 {
family inet {
address 10.70.70.1/24;
}
}
}
st0 {
unit 0 {
multipoint;
family inet {
address 10.10.10.3/24;
}
}
}
[edit]
user@host# show protocols
ospf {
area 0.0.0.0 {
interface st0.0 {
interface-type p2mp;
neighbor 10.10.10.1;
}
interface fe-0/0/4.0;
}
}
[edit]
user@host# show routing-options
static {
route 10.1.1.1/32 next-hop 10.3.3.2;
}
[edit]
user@host# show security ike
proposal ike-proposal {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha1;
encryption-algorithm aes-128-cbc;
}
policy ike-policy1 {
mode main;
proposals ike-proposal;
certificate {
local-certificate Local1;
}
}
gateway spoke-to-hub-gw {
ike-policy ike-policy1;
address 10.1.1.1;
local-identity distinguished-name;
remote-identity distinguished-name;
external-interface ge-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec-proposal {
protocol esp;
authentication-algorithm hmac-md5-96;
encryption-algorithm des-cbc;
}
policy vpn-policy1 {
perfect-forward-secrecy {
keys group14;
}
proposals ipsec-proposal;
}
vpn spoke-to-hub {
bind-interface st0.0;
ike {
gateway spoke-to-hub-gw;
ipsec-policy vpn-policy1;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
st0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
fe-0/0/4.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ca-profile1 {
ca-identity ca-profile1;
enrollment {
url http://pc4/certsrv/mscep/mscep.dll;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证 IKE 第 1 阶段状态
目的
验证 IKE 第 1 阶段状态。
操作
在操作模式下,输入 show security ike security-associations 命令。
user@host> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 5480159 UP 22432fb6f7fbc389 412b751f79b45099 Main 10.2.2.1 5480161 UP d455050707bc3eaf b3dde111232270d2 Main 10.3.3.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 第 2 阶段状态
目的
验证 IPsec 第 2 阶段状态。
操作
在操作模式下,输入 security ipsec security-associations 命令。
user@host> security ipsec security-associations Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway <268173400 ESP:des/ md5 f38eea12 2954/ unlim - root 500 10.2.2.1 >268173400 ESP:des/ md5 bb48d228 2954/ unlim - root 500 10.2.2.1 <268173401 ESP:des/ md5 bcd1390b 3530/ unlim - root 500 10.3.3.1 >268173401 ESP:des/ md5 77fcf6e2 3530/ unlim - root 500 10.3.3.1
意义
该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 10.10.10.2 st0.0 hub-to-spoke-vpn Auto C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 10.10.10.3 st0.0 hub-to-spoke-vpn Auto C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 OSPF
目的
验证 OSPF 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show ospf neighbor 命令。
user@host> show ospf neighbor Address Interface State ID Pri Dead 10.10.10.3 st0.0 Full 10.255.226.179 128 32 10.10.10.2 st0.0 Full 10.207.36.182 128 38
验证学习的路由
目的
验证是否已获知到分支的路由。
操作
在操作模式下,输入 show route 60.60.60.0 命令。
user@host> show route 10.60.60.0
inet.0: 48 destinations, 48 routes (47 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
10.60.60.0/24 *[OSPF/10] 00:51:13, metric 2
> to 10.10.10.2 via st0.0
在操作模式下,输入 show route 10.70.70.0 命令。
user@host> show route 10.70.70.0
inet.0: 48 destinations, 48 routes (47 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
10.70.70.0/24 *[OSPF/10] 00:51:48, metric 2
> to 10.10.10.3 via st0.0
示例:使用 OSPFv3 配置 AutoVPN 以实现 IPv6 流量
此示例说明如何将 AutoVPN 中心配置为充当单个终结点,然后将两个分支配置为充当到远程站点的隧道。此示例使用 OSPFv3 配置适用于 IPv6 的 AutoVPN 环境,以使用基于证书的身份验证通过 VPN 隧道 转发数据包。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
三个支持 SRX 系列防火墙作为 AutoVPN 中心和辐射。
-
Junos OS 18.1R1 及更高版本。
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
您应该熟悉用于通过 VPN 隧道转发数据包的动态路由协议。
概述
此示例显示了在中心位置采用 OSPFv3 路由协议的 AutoVPN 配置,以及两个分支的后续配置。
在此示例中,第一步是使用简单证书注册协议 (SCEP) 在每个设备中注册数字证书。分支的证书在主题字段中包含组织单位 (OU) 值“SLT”;中心配置了组 IKE ID,以匹配 OU 字段中的值“SLT”。
分支与中心建立 IPsec VPN 连接,使它们能够相互通信以及访问中心上的资源。在 AutoVPN 中心和所有分支上配置的第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 16 显示了此示例中使用的选项。
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
RSA 数字证书 |
|
Diffie-Hellman (DH) 组 |
19 |
|
身份验证算法 |
SHA-384 |
|
加密算法 |
AES 256 全血细胞计数 |
|
IKE 策略: |
|
|
模式 |
主要 |
|
IPsec 提议: |
|
|
协议 |
ESP |
|
生命周期秒数 |
3000 |
|
加密算法 |
AES 256 GCM |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
19 |
在所有设备上配置相同的证书颁发机构 (CA)。
表 17 显示在中心和所有辐射上配置的选项。
|
选项 |
枢纽 |
所有辐条 |
|---|---|---|
|
IKE 网关: |
||
|
远程 IP 地址 |
动态 |
2001:db8:2000::1 |
|
远程 IKE ID |
分支证书上的可分辨名称 (DN),组织单位 (OU) 字段中的字符串 |
集线器证书上的 DN |
|
本地 IKE ID |
集线器证书上的 DN |
分支证书上的 DN |
|
外部接口 |
ge-0/0/0 |
辐条1:ge-0/0/0.0 辐条2:ge-0/0/0.0 |
|
VPN: |
||
|
绑定接口 |
st0.1 |
st0.1 |
|
建立隧道 |
(未配置) |
配置提交后立即 |
表 18 显示了每个分支上不同的配置选项。
|
选项 |
辐条 1 |
辐条 2 |
|---|---|---|
|
ST0.1 接口 |
2001:db8:7000::2/64 |
2001:db8:7000::3/64 |
|
与内部网络的接口 |
(ge-0/0/1.0) 2001:db8:4000::1/64 |
(ge-0/0/1.0) 2001:db8:6000::1/64 |
|
互联网接口 |
(ge-0/0/0.0) 2001:db8:3000::2/64 |
(ge-0/0/0.0) 2001:db8:5000::2/64 |
所有设备的路由信息都通过 VPN 隧道进行交换。
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。
配置
要配置 AutoVPN,请执行以下任务:
第一部分介绍如何在中心辐射设备上使用简单证书注册协议 (SCEP) 联机获取 CA 和本地证书。
使用 SCEP 注册设备证书
分步过程
若要在中心使用 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email hub@example.net ip-address 10.1.1.1 subject DC=example.net,CN=hub,OU=SLT,O=example,L=Bengaluru,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a6d5f300000000258d Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Bengaluru, Common name: hub, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Bengaluru, O=example, OU=SLT, CN=hub Alternate subject: "hub@example.net", example.net, 10.1.1.1 Validity: Not before: 11- 6-2020 09:39 Not after: 11- 6-2021 09:49 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:c9:c9:cc:30:b6:7a:86:12:89:b5:18:b3:76 01:2d:cc:65:a8:a8:42:78:cd:d0:9a:a2:c0:aa:c4:bd:da:af:88:f3 2a:78:1f:0a:58:e6:11:2c:81:8f:0e:7c:de:86:fc:48:4c:28:5b:8b 34:91:ff:2e:91:e7:b5:bd:79:12:de:39:46:d9:fb:5c:91:41:d1:da 90:f5:09:00:9b:90:07:9d:50:92:7d:ff:fb:3f:3c:bc:34:e7:e3:c8 ea:cb:99:18:b4:b6:1d:a8:99:d3:36:b9:1b:36:ef:3e:a1:fd:48:82 6a:da:22:07:da:e0:d2:55:ef:57:be:09:7a:0e:17:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: e1:f7:a1:a6:1e:c3:97:69:a5:07:9b:09:14:1a:c7:ae:09:f1:f6:35 (sha1) a0:02:fa:8d:5c:63:e5:6d:f7:f4:78:56:ac:4e:b2:c4 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started
分步过程
要使用分支 1 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke1@example.net ip-address 10.2.2.1 subject DC=example.net,CN=spoke1,OU=SLT,O=example,L=Mysore,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40a7975f00000000258e Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Mysore, Common name: spoke1, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Mysore, O=example, OU=SLT, CN=spoke1 Alternate subject: "spoke1@example.net", example.net, 10.2.2.1 Validity: Not before: 11- 6-2020 09:40 Not after: 11- 6-2021 09:50 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:d8:45:09:77:cd:36:9a:6f:58:44:18:91:db b0:c7:8a:ee:c8:d7:a6:d2:e2:e7:20:46:2b:26:1a:92:e2:4e:8a:ce c9:25:d9:74:a2:81:ad:ea:e0:38:a0:2f:2d:ab:a6:58:ac:88:35:f4 90:01:08:33:33:75:2c:44:26:f8:25:18:97:96:e4:28:de:3b:35:f2 4a:f5:92:b7:57:ae:73:4f:8e:56:71:ab:81:54:1d:75:88:77:13:64 1b:6b:01:96:15:0a:1c:54:e3:db:f8:ec:ec:27:5b:86:39:c1:09:a1 e4:24:1a:19:0d:14:2c:4b:94:a4:04:91:3f:cb:ef:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: b6:24:2a:0e:96:5d:8c:4a:11:f3:5a:24:89:7c:df:ea:d5:c0:80:56 (sha1) 31:58:7f:15:bb:d4:66:b8:76:1a:42:4a:8a:16:b3:a9 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
分步过程
要使用分支 2 上的 SCEP 注册数字证书,请执行以下操作:
-
配置 CA。
[edit] user@host# set security pki ca-profile ca-profile1 ca-identity ca-profile1 user@host# set security pki ca-profile ca-profile1 enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set security pki ca-profile ca-profile1 revocation-check disable user@host# commit
-
注册 CA 证书。
user@host> request security pki ca-certificate enroll ca-profile ca-profile1
在提示符下键入 yes 以加载 CA 证书。
-
生成密钥对。
user@host> request security pki generate-key-pair certificate-id Local1
-
注册本地证书。
user@host> request security pki local-certificate enroll ca-profile ca-profile1 certificate-id Local1 domain-name example.net email spoke2@example.net ip-address 10.3.3.1 subject DC=example.net,CN=spoke2,OU=SLT,O=example,L=Tumkur,ST=KA,C=IN challenge-password <password>
-
验证本地证书。
user@host> show security pki local-certificate detail Certificate identifier: Local1 Certificate version: 3 Serial number: 40bb71d400000000258f Issuer: Common name: CASERVER1, Domain component: net, Domain component: internal Subject: Organization: example, Organizational unit: SLT, Country: IN, State: KA, Locality: Tumkur, Common name: spoke2, Domain component: example.net Subject string: C=IN, DC=example.net, ST=KA, L=Tumkur, O=example, OU=SLT, CN=spoke2 Alternate subject: "spoke2@example.net", example.net, 10.3.3.1 Validity: Not before: 11- 6-2020 10:02 Not after: 11- 6-2021 10:12 Public key algorithm: rsaEncryption(1024 bits) 30:81:89:02:81:81:00:b6:2e:e2:da:e6:ac:57:e4:5d:ff:de:f6:89 27:d6:3e:1b:4a:3f:b2:2d:b3:d3:61:ed:ed:6a:07:d9:8a:d2:24:03 77:1a:fe:84:e1:12:8a:2d:63:6e:bf:02:6b:15:96:5a:4f:37:a0:46 44:09:96:c0:fd:bb:ab:79:2c:5d:92:bd:31:f0:3b:29:51:ce:89:8e 7c:2b:02:d0:14:5b:0a:a9:02:93:21:ea:f9:fc:4a:e7:08:bc:b1:6d 7c:f8:3e:53:58:8e:f1:86:13:fe:78:b5:df:0b:8e:53:00:4a:46:11 58:4a:38:e9:82:43:d8:25:47:7d:ef:18:f0:ef:a7:02:03:01:00:01 Signature algorithm: sha1WithRSAEncryption Distribution CRL: http://ca-server1/CertEnroll/CASERVER1.crl file://\\ca-server1\CertEnroll\CASERVER1.crl Fingerprint: 1a:6d:77:ac:fd:94:68:ce:cf:8a:85:f0:39:fc:e0:6b:fd:fe:b8:66 (sha1) 00:b1:32:5f:7b:24:9c:e5:02:e6:72:75:9e:a5:f4:77 (md5) Auto-re-enrollment: Status: Disabled Next trigger time: Timer not started主题字段中显示的组织单位 (OU) 为
SLT。中心上的 IKE 配置包括ou=SLT用于标识分支。
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate HUB set security ike gateway IKE_GWA_1 ike-policy IKE_POL set security ike gateway IKE_GWA_1 dynamic distinguished-name wildcard OU=SLT set security ike gateway IKE_GWA_1 dead-peer-detection always-send set security ike gateway IKE_GWA_1 dead-peer-detection interval 10 set security ike gateway IKE_GWA_1 dead-peer-detection threshold 3 set security ike gateway IKE_GWA_1 local-identity distinguished-name set security ike gateway IKE_GWA_1 external-interface ge-0/0/0 set security ike gateway IKE_GWA_1 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPNA_1 bind-interface st0.1 set security ipsec vpn IPSEC_VPNA_1 ike gateway IKE_GWA_1 set security ipsec vpn IPSEC_VPNA_1 ike ipsec-policy IPSEC_POL set security policies default-policy permit-all set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces ge-0/0/0.0 set security zones security-zone untrust interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/l..0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:2000::1/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:1000::2/64 set interfaces st0 unit 1 multipoint set interfaces st0 unit 1 family inet6 address 2001:db8:7000::1/64 set routing-options rib inet6.0 static route 2001:db8:3000::/64 next-hop 2001:db8:2000::1 set routing-options rib inet6.0 static route 2001:db8:5000::/64 next-hop 2001:db8:2000::1 set protocols ospf3 traceoptions file ospf set protocols ospf3 traceoptions flag all set protocols ospf3 area 0.0.0.0 interface st0.1 interface-type p2mp set protocols ospf3 area 0.0.0.0 interface st0.1 demand-circuit set protocols ospf3 area 0.0.0.0 interface st0.1 dynamic-neighbors set protocols ospf3 area 0.0.0.0 interface ge-0/0/1.0
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:2000::1/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:1000::2/64 user@host# set st0 unit 1 multipoint user@host# set st0 unit 1 family inet6 address 2001:db8:7000::1/64
-
配置路由协议。
[edit protocols ospf3] user@host# set traceoptions file ospf user@host# set traceoptions flag all user@host# set area 0.0.0.0 interface st0.1 interface-type p2mp user@host# set area 0.0.0.0 interface st0.1 demand-circuit user@host# set area 0.0.0.0 interface st0.1 dynamic-neighbors user@host# set area 0.0.0.0 interface ge-0/0/1.0 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:3000::/64 next-hop 2001:db8:2000::1 user@host# set rib inet6.0 static route 2001:db8:5000::/64 next-hop 2001:db8:2000::1
-
配置第 1 阶段选项。
[edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate HUB [edit security ike gateway IKE_GWA_1] user@host# set ike-policy IKE_POL user@host# set dynamic distinguished-name wildcard OU=SLT user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROP] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPNA_1] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GWA_1 user@host# set ike ipsec-policy IPSEC_POL
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0 user@host# set interfaces st0.1 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/1.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set pki ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:2000::1/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:1000::2/64;
}
}
}
st0 {
unit 1 {
family inet6 {
address 2001:db8:7000::1/64;
}
}
}
[edit]
user@host# show protocols
ospf3 {
traceoptions {
file ospf;
flag all;
}
area 0.0.0.0 {
interface st0.1 {
interface-type p2mp;
demand-circuit;
dynamic-neighbors;
}
interface ge-0/0/1.0;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route 2001:db8:3000::/64 next-hop 2001:db8::1;
route 2001:db8:5000::/64 next-hop 2001:db8::1;
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate HUB;
}
}
gateway IKE_GWA_1 {
ike-policy IKE_POL;
dynamic {
distinguished-name {
wildcard OU=SLT;
}
}
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
external-interface ge-0/0/0.0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
authentication-algorithm aes-256-gcm;
set lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPNA_1 {
bind-interface st0.1;
ike {
gateway IKE_GWA_1;
ipsec-policy IPSEC_POL;
}
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 1
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate SPOKE1 set security ike gateway IKE_GW_SPOKE_1 ike-policy IKE_POL set security ike gateway IKE_GW_SPOKE_1 address 2001:db8:2000::1 set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection always-send set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection interval 10 set security ike gateway IKE_GW_SPOKE_1 dead-peer-detection threshold 3 set security ike gateway IKE_GW_SPOKE_1 local-identity distinguished-name set security ike gateway IKE_GW_SPOKE_1 remote-identity distinguished-name container OU=SLT set security ike gateway IKE_GW_SPOKE_1 external-interface ge-0/0/0.0 set security ike gateway IKE_GW_SPOKE_1 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN_SPOKE_1 bind-interface st0.1 set security ipsec vpn IPSEC_VPN_SPOKE_1 ike gateway IKE_GW_SPOKE_1 set security ipsec vpn IPSEC_VPN_SPOKE_1 ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN_SPOKE_1 establish-tunnels immediately set security policies default-policy permit-all set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces st0.1 set security zones security-zone untrust interfaces ge-0/0/1.0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:3000::2/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:4000::1/64 set interfaces st0 unit 1 family inet6 address 2001:db8:7000::2/64 set routing-options rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:3000::2 set protocols ospf3 traceoptions file ospf set protocols ospf3 traceoptions flag all set protocols ospf3 area 0.0.0.0 interface st0.1 interface-type p2mp set protocols ospf3 area 0.0.0.0 interface st0.1 demand-circuit set protocols ospf3 area 0.0.0.0 interface st0.1 dynamic-neighbors set protocols ospf3 area 0.0.0.0 interface ge-0/0/1.0
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 1:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:3000::2/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:4000::1/64 user@host# set st0 unit 1 family inet6 address 2001:db8:7000::2/64
-
配置路由协议。
[edit protocols ospf3] user@host# set traceoptions file ospf user@host# set traceoptions flag all user@host# set area 0.0.0.0 interface st0.1 interface-type p2mp user@host# set area 0.0.0.0 interface st0.1 demand-circuit user@host# set area 0.0.0.0 interface st0.1 dynamic-neighbors user@host# set area 0.0.0.0 interface ge-0/0/1.0 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:3000::2
-
配置第 1 阶段选项。
[edit security ike proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate SPOKE1 [edit security ike gateway IKE_GW_SPOKE_1] user@host# set ike-policy IKE_POL user@host# set address 2001:db8:2000::1 user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name container OU=SLT user@host# set external-interface ge-0/0/0.0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROPl] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPN_SPOKE_1] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GW_SPOKE_1 user@host# set ike ipsec-policy IPSEC_POL user@host# set establish-tunnels immediately
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces st0.1 user@host# set interfaces ge-0/0/1.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:3000::2/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:4000::1/64;
}
}
}
st0 {
unit 1 {
family inet6 {
address 2001:db8:7000::2/64;
}
}
}
[edit]
user@host# show protocols
ospf3 {
traceoptions {
file ospf;
flag all;
}
area 0.0.0.0 {
interface st0.1 {
interface-type p2mp;
demand-circuit;
dynamic-neighbors;
}
interface ge-0/0/1.0;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route 2001:db8:2000::/64 next-hop [ 2001:db8:3000::1 2001:db8:5000::1 ];
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate SPOKE1;
}
}
gateway IKE_GW_SPOKE_1 {
ike-policy IKE_POL;
address 2001:db8:2000::1;
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
remote-identity distinguished-name container OU=SLT;
external-interface ge-0/0/0.0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPN_SPOKE_1 {
bind-interface st0.1;
ike {
gateway IKE_GW_SPOKE_1;
ipsec-policy IPSEC_POL;
}
establish-tunnels immediately;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
配置分支 2
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set security pki ca-profile ROOT-CA ca-identity ROOT-CA set security pki ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll set security pki ca-profile ROOT-CA enrollment retry 5 set security pki ca-profile ROOT-CA enrollment retry-interval 0 set security pki ca-profile ROOT-CA revocation-check disable set security ike traceoptions file ik set security ike traceoptions flag all set security ike proposal IKE_PROP authentication-method rsa-signatures set security ike proposal IKE_PROP dh-group group19 set security ike proposal IKE_PROP authentication-algorithm sha-384 set security ike proposal IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal IKE_PROP lifetime-seconds 6000 set security ike policy IKE_POL mode main set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate SPOKE2 set security ike gateway IKE_GW_SPOKE_2 ike-policy IKE_POL set security ike gateway IKE_GW_SPOKE_2 address 2001:db8:2000::1 set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection always-send set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection interval 10 set security ike gateway IKE_GW_SPOKE_2 dead-peer-detection threshold 3 set security ike gateway IKE_GW_SPOKE_2 local-identity distinguished-name set security ike gateway IKE_GW_SPOKE_2 remote-identity distinguished-name container OU=SLT set security ike gateway IKE_GW_SPOKE_2 external-interface ge-0/0/0.0 set security ike gateway IKE_GW_SPOKE_2 version v1-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal IPSEC_PROP lifetime-seconds 3000 set security ipsec policy IPSEC_POL perfect-forward-secrecy keys group19 set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN_SPOKE_2 bind-interface st0.1 set security ipsec vpn IPSEC_VPN_SPOKE_2 ike gateway IKE_GW_SPOKE_2 set security ipsec vpn IPSEC_VPN_SPOKE_2 ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN_SPOKE_2 establish-tunnels on-traffic set security policies default-policy permit-all set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols ospf3 set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols ospf3 set security zones security-zone untrust interfaces st0.1 set security zones security-zone untrust interfaces ge-0/0/1.0 set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:5000::2/64 set interfaces ge-0/0/1 unit 0 family inet6 address 2001:db8:6000::1/64 set interfaces st0 unit 1 family inet6 address 2001:db8:7000::3/64 set routing-options rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:5000::1 set protocols ospf3 traceoptions file ospf set protocols ospf3 traceoptions flag all set protocols ospf3 area 0.0.0.0 interface st0.1 interface-type p2mp set protocols ospf3 area 0.0.0.0 interface st0.1 demand-circuit set protocols ospf3 area 0.0.0.0 interface st0.1 dynamic-neighbors set protocols ospf3 area 0.0.0.0 interface ge-0/0/1.0
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅在配置模式下使用 CLI 编辑器。
要配置分支 2:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/0 unit 0 family inet6 address 2001:db8:5000::2/64 user@host# set ge-0/0/1 unit 0 family inet6 address 2001:db8:6000::1/64 user@host# set st0 unit 1 family inet6 address 2001:db8:7000::3/64
-
配置路由协议。
[edit protocols ospf3] user@host# set traceoptions file ospf user@host# set traceoptions flag all user@host# set area 0.0.0.0 interface st0.1 interface-type p2mp user@host# set area 0.0.0.0 interface st0.1 demand-circuit user@host# set area 0.0.0.0 interface st0.1 dynamic-neighbors user@host# set area 0.0.0.0 interface ge-0/0/1.0 [edit routing-options] user@host# set rib inet6.0 static route 2001:db8:2000::/64 next-hop 2001:db8:5000::1
-
配置第 1 阶段选项。
[edit security ike proposal IKE_PROP] user@host# set authentication-method rsa-signatures user@host# set dh-group group19 user@host# set authentication-algorithm sha-384 user@host# set encryption-algorithm aes-256-cbc user@host# set lifetime-seconds 6000 [edit security ike traceoptions] user@host# set file ik user@host# set flag all [edit security ike policy IKE_POL] user@host# set mode main user@host# set proposals IKE_PROP user@host# set certificate local-certificate SPOKE2 [edit security ike gateway IKE_GW_SPOKE_2] user@host# set ike-policy IKE_POL user@host# set address 2001:db8:2000::1 user@host# set dead-peer-detection always-send user@host# set dead-peer-detection interval 10 user@host# set dead-peer-detection threshold 3 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name container OU=SLT user@host# set external-interface ge-0/0/0.0 user@host# set version v1-only
-
配置第 2 阶段选项。
[edit security ipsec proposal IPSEC_PROPl] user@host# set protocol esp user@host# set encryption-algorithm aes-256-gcm user@host# set lifetime-seconds 3000 [edit security ipsec policy IPSEC_POL] user@host# set perfect-forward-secrecy keys group19 user@host# set proposals IPSEC_PROP [edit security ipsec vpn IPSEC_VPN_SPOKE_2] user@host# set bind-interface st0.1 user@host# set ike gateway IKE_GW_SPOKE_2 user@host# set ike ipsec-policy IPSEC_POL user@host# set establish-tunnels on-traffic
-
配置区域。
[edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces st0.1 user@host# set interfaces ge-0/0/1.0 [edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols ospf3 user@host# set interfaces ge-0/0/0.0
-
配置默认安全策略。
[edit security policies] user@host# set default-policy permit-all
-
配置 CA 配置文件。
[edit security pki] user@host# set ca-profile ROOT-CA ca-identity ROOT-CA user@host# set ca-profile ROOT-CA enrollment url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll user@host# set ca-profile ROOT-CA enrollment retry 5 user@host# set ca-profile ROOT-CA enrollment retry-interval 0 user@host# set ca-profile ROOT-CA revocation-check disable
结果
在配置模式下,输入 show interfaces、 show protocols、 show routing-optionsshow security ike、 show security ipsec、 show security zones、 和show security policiesshow security pki命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/0 {
unit 0 {
family inet6 {
address 2001:db8:5000::2/64;
}
}
}
ge-0/0/1 {
unit 0 {
family inet6 {
address 2001:db8:6000::1/64;
}
}
}
st0 {
unit 1 {
family inet6 {
address 2001:db8:7000::3/64;
}
}
}
[edit]
user@host# show protocols
ospf3 {
traceoptions {
file ospf;
flag all;
}
area 0.0.0.0 {
interface st0.1 {
interface-type p2mp;
demand-circuit;
dynamic-neighbors;
}
interface ge-0/0/1.0;
}
}
[edit]
user@host# show routing-options
rib inet6.0 {
static {
route 2001:db8:2000::/64 next-hop [ 2001:db8:3000::1 2001:db8:5000::1 ];
}
}
[edit]
user@host# show security ike
traceoptions {
file ik;
flag all;
}
proposal IKE_PROP {
authentication-method rsa-signatures;
dh-group group19;
authentication-algorithm sha-384;
encryption-algorithm aes-256-cbc;
lifetime-seconds 6000;
}
policy IKE_POL {
mode main;
proposals IKE_PROP;
certificate {
local-certificate SPOKE2;
}
}
gateway IKE_GW_SPOKE_2 {
ike-policy IKE_POL;
address 2001:db8:2000::1;
dead-peer-detection {
always-send;
interval 10;
threshold 3;
}
local-identity distinguished-name;
remote-identity distinguished-name container OU=SLT;
external-interface ge-0/0/0.0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal IPSEC_PROP {
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 3000;
}
policy IPSEC_POL {
perfect-forward-secrecy {
keys group19;
}
proposals IPSEC_PROP;
}
vpn IPSEC_VPN_SPOKE_2 {
bind-interface st0.1;
ike {
gateway IKE_GW_SPOKE_2;
ipsec-policy IPSEC_POL;
}
establish-tunnels on-traffic;
}
[edit]
user@host# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/1.0;
st0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
ospf3;
}
}
interfaces {
ge-0/0/0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
[edit]
user@host# show security pki
ca-profile ROOT-CA {
ca-identity ROOT-CA;
enrollment {
url http://2001:db8:1710:f00::2/certsrv/mscep/mscep.dll;
retry 5;
retry-interval 0;
}
revocation-check {
disable;
}
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证 IKE 状态
目的
验证 IKE 状态。
操作
在操作模式下,输入 show security ike sa 命令。
user@host> show security ike sa Index State Initiator cookie Responder cookie Mode Remote Address 493333 UP 2001:db8:88b49d915e684c93 2001:db8:fe890b1cac8522b5 Main 2001:db8:3000::2 493334 UP 2001:db8:26e40244ad3d722d 2001:db8:68b4d9f94097d32e Main 2001:db8:5000::2
意义
该 show security ike sa 命令会列出所有活动的 IKE 第 1 阶段 SA。如果未列出任何 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 状态
目的
验证 IPsec 状态。
操作
在操作模式下,输入 show security ipsec sa 命令。
user@host> show security ipsec sa Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway >67108885 ESP:aes-gcm-256/None fdef4dab 2918/ unlim - root 500 2001:db8:3000::2 >67108885 ESP:aes-gcm-256/None e785dadc 2918/ unlim - root 500 2001:db8:3000::2 >67108887 ESP:aes-gcm-256/None 34a787af 2971/ unlim - root 500 2001:db8:5000::2 >67108887 ESP:aes-gcm-256/None cf57007f 2971/ unlim - root 500 2001:db8:5000::2
意义
该 show security ipsec sa 命令将列出所有活动的 IKE 第 2 阶段 SA。如果未列出任何 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证 IPsec 下一跳隧道
目的
验证 IPsec 下一跃点隧道。
操作
在操作模式下,输入 show security ipsec next-hop-tunnels 命令。
user@host> show security ipsec next-hop-tunnels Next-hop gateway interface IPSec VPN name Flag IKE-ID XAUTH username 2001:db8:9000::2 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE1 Not-Available 2001:db8:9000::3 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE2 Not-Available 2001:db8::5668:ad10:fcd8:163c st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE1 Not-Available 2001:db8::5668:ad10:fcd8:18a1 st0.1 IPSEC_VPNA_1 Auto C=US, DC=example.net, ST=CA, L=Sunnyvale, O=example, OU=SLT, CN=SPOKE2 Not-Available
意义
下一跃点网关是分支接口的 st0 IP 地址。下一跃点应与正确的 IPsec VPN 名称相关联。
验证 OSPFv3
目的
验证 OSPFv3 是否引用分支接口的 st0 IP 地址。
操作
在操作模式下,输入 show ospf3 neighbor detail 命令。
枢纽:
user@host> show ospf3 neighbor detail ID Interface State Pri Dead 2001:db8:7000:2 st0.1 Full 128 - Neighbor-address 2001:db8::5668:ad10:fcd8:18a1 Area 0.0.0.0, opt 0x33, OSPF3-Intf-Index 2 DR-ID 0.0.0.0, BDR-ID 0.0.0.0 Up 00:01:35, adjacent 00:01:31 Hello suppressed 00:01:31 ago 2001:db8:7000:3 st0.1 Full 128 - Neighbor-address 2001:db8::5668:ad10:fcd8:163c Area 0.0.0.0, opt 0x33, OSPF3-Intf-Index 2 DR-ID 0.0.0.0, BDR-ID 0.0.0.0 Up 00:01:41, adjacent 00:01:37 Hello suppressed 00:01:37 ago
辐条1:
user@host> show ospf3 neighbor detail ID Interface State Pri Dead 2001:db8:7000:1 st0.1 Full 128 - Neighbor-address 2001:db8::5668:ad10:fcd8:1946 Area 0.0.0.0, opt 0x33, OSPF3-Intf-Index 2 DR-ID 0.0.0.0, BDR-ID 0.0.0.0 Up 00:05:38, adjacent 00:05:38 Hello suppressed 00:05:34 ago
辐条2:
user@host> show ospf3 neighbor detail ID Interface State Pri Dead 2001:db8:7000:1 st0.1 Full 128 - Neighbor-address 2001:db8::5668:ad10:fcd8:1946 Area 0.0.0.0, opt 0x33, OSPF3-Intf-Index 2 DR-ID 0.0.0.0, BDR-ID 0.0.0.0 Up 00:04:44, adjacent 00:04:44 Hello suppressed 00:04:40 ago
示例:通过带有流量选择器的 AutoVPN 隧道转发流量
此示例说明如何配置流量选择器(而不是动态路由协议),以通过 AutoVPN 部署中的 VPN 隧道转发数据包。配置流量选择器时,安全隧道 (st0) 接口必须处于点对点模式。流量选择器在中心设备和分支设备上均配置。该示例使用基于证书的身份验证。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
在机箱群集中连接并配置的两个 SRX 系列防火墙。机箱群集是 AutoVPN 中枢。
配置为 AutoVPN 分支的 SRX 系列防火墙。
Junos OS 版本 12.3X48-D10 或更高版本。
在中心设备和分支设备中注册的数字证书,允许设备相互进行身份验证。
准备工作:
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
在每个设备中注册数字证书。请参阅 注册证书。
概述
在此示例中,流量选择器是在 AutoVPN 中心辐射型上配置的。只有符合已配置流量选择器的流量才会通过隧道转发。在集线器上,流量选择器配置了本地 IP 地址 192.0.0.0/8 和远程 IP 地址 172.0.0.0/8。在分支上,流量选择器配置了本地 IP 地址 172.0.0.0/8 和远程 IP 地址 192.0.0.0/8。
分支上配置的流量选择器 IP 地址可以是中枢上配置的流量选择器 IP 地址的子集。这称为 流量选择器灵活匹配。
在 AutoVPN 中心和分支上配置的某些第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 19 显示此示例中使用的值:
选项 |
value |
|---|---|
IKE 提案: |
|
身份验证方法 |
rsa-signatures |
Diffie-Hellman (DH) 组 |
group5 |
身份验证算法 |
sha-1 |
加密算法 |
aes-256-cbc |
IKE 策略: |
|
模式 |
主 |
证书 |
本地证书 |
IKE 网关: |
|
动态 |
可分辨名称通配符 DC=Common_component |
IKE 用户类型 |
组 IKE ID |
本地标识 |
可分辨名称 |
版本 |
仅限 v1 |
IPsec 提议: |
|
协议 |
esp |
身份验证算法 |
HMAC-SHA1-96 |
加密算法 |
AES-192-CBC |
辈子 |
3600 秒 150,000 KB |
IPsec 策略: |
|
完全向前保密 (PFS) 组 |
group5 |
配置
配置集线器
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/2 gigether-options redundant-parent reth1 set interfaces ge-0/0/3 gigether-options redundant-parent reth0 set interfaces ge-8/0/2 gigether-options redundant-parent reth1 set interfaces ge-8/0/3 gigether-options redundant-parent reth0 set interfaces lo0 unit 0 family inet address 10.100.1.100/24 set interfaces lo0 redundant-pseudo-interface-options redundancy-group 1 set interfaces reth0 redundant-ether-options redundancy-group 1 set interfaces reth0 unit 0 family inet address 192.168.81.1/8 set interfaces reth1 redundant-ether-options redundancy-group 1 set interfaces reth1 unit 0 family inet address 10.2.2.1/24 set interfaces st0 unit 1 family inet set security ike proposal prop_ike authentication-method rsa-signatures set security ike proposal prop_ike dh-group group5 set security ike proposal prop_ike authentication-algorithm sha1 set security ike proposal prop_ike encryption-algorithm aes-256-cbc set security ike policy ikepol1 mode main set security ike policy ikepol1 proposals prop_ike set security ike policy ikepol1 certificate local-certificate Hub_ID set security ike gateway HUB_GW ike-policy ikepol1 set security ike gateway HUB_GW dynamic distinguished-name wildcard DC=Domain_component set security ike gateway HUB_GW dynamic ike-user-type group-ike-id set security ike gateway HUB_GW local-identity distinguished-name set security ike gateway HUB_GW external-interface reth1 set security ike gateway HUB_GW version v1-only set security ipsec proposal prop_ipsec protocol esp set security ipsec proposal prop_ipsec authentication-algorithm hmac-sha1-96 set security ipsec proposal prop_ipsec encryption-algorithm aes-192-cbc set security ipsec proposal prop_ipsec lifetime-seconds 3600 set security ipsec proposal prop_ipsec lifetime-kilobytes 150000 set security ipsec policy ipsecpol1 perfect-forward-secrecy keys group5 set security ipsec policy ipsecpol1 proposals prop_ipsec set security ipsec vpn HUB_VPN bind-interface st0.1 set security ipsec vpn HUB_VPN ike gateway HUB_GW set security ipsec vpn HUB_VPN ike ipsec-policy ipsecpol1 set security ipsec vpn HUB_VPN traffic-selector ts1 local-ip 192.0.0.0/8 set security ipsec vpn HUB_VPN traffic-selector ts1 remote-ip 172.0.0.0/8 set security pki ca-profile rsa ca-identity rsa set security pki ca-profile rsa revocation-check disable set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces st0.1 set security zones security-zone trust interfaces reth0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces reth1.0 set security policies default-policy permit-all
您可以在[edit security ike gateway gateway-name dynamic] 层级配置 CLI 选项reject-duplicate-connection,以保留现有隧道会话,并拒绝使用相同 IKE ID 的新隧道的协商请求。默认情况下,当建立具有相同 IKE ID 的新隧道时,将拆除现有隧道。reject-duplicate-connection仅当为 IKE 网关配置 或 ike-user-type shared-ike-id 时ike-user-type group-ike-id,才支持该选项;此选项不支持该aaa access-profile profile-name配置。
仅当您确定应拒绝重新建立具有相同 IKE ID 的新隧道时,才使用 CLI 选项 reject-duplicate-connection 。
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅 CLI 用户指南中的在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
配置接口。
[edit interfaces] user@host# set ge-0/0/2 gigether-options redundant-parent reth1 user@host# set ge-0/0/3 gigether-options redundant-parent reth0 user@host# set ge-8/0/2 gigether-options redundant-parent reth1 user@host# set ge-8/0/3 gigether-options redundant-parent reth0 user@host# set lo0 unit 0 family inet address 10.100.1.100/24 user@host# set lo0 redundant-pseudo-interface-options redundancy-group 1 user@host# set reth0 redundant-ether-options redundancy-group 1 user@host# set reth0 unit 0 family inet address 192.168.81.1/8 user@host# set reth1 redundant-ether-options redundancy-group 1 user@host# set reth1 unit 0 family inet address 10.2.2.1/24 user@host# set st0 unit 1 family inet
配置第 1 阶段选项。
[edit security ike proposal prop_ike] user@host# set authentication-method rsa-signatures user@host# set dh-group group5 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-256-cbc [edit security ike policy ikepol1] user@host# set mode main user@host# set proposals prop_ike user@host# set certificate local-certificate Hub_ID [edit security ike gateway HUB_GW] user@host# set ike-policy ikepol1 user@host# set dynamic distinguished-name wildcard DC=Domain_component user@host# set dynamic ike-user-type group-ike-id user@host# set local-identity distinguished-name user@host# set external-interface reth1 user@host# set version v1-only
配置第 2 阶段选项。
[edit security ipsec proposal prop_ipsec] user@host# set protocol esp user@host# set authentication-algorithm hmac-sha1-96 user@host# set encryption-algorithm aes-192-cbc user@host# set lifetime-seconds 3600 user@host# set lifetime-kilobytes 150000 [edit security ipsec policy ipsecpol1] user@host# set perfect-forward-secrecy keys group5 user@host# set proposals prop_ipsec [edit security ipsec HUB_VPN] user@host# set bind-interface st0.1 user@host# set ike gateway HUB_GW user@host# set ike ipsec-policy ipsecpol1 user@host# set traffic-selector ts1 local-ip 192.0.0.0/8 user@host# set traffic-selector ts1 remote-ip 172.0.0.0/8
配置证书信息。
[edit security pki] user@host# set ca-profile rsa ca-identity rsa user@host# set ca-profile rsa revocation-check disable
配置安全区域。
[edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.1 user@host# set interfaces reth0.0 [edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces lo0.0 user@host# set interfaces reth1.0 [edit security policies] user@host# set default-policy permit-all
结果
在配置模式下,输入 show interfaces、 show security ike、 show security zonesshow security ipsecshow security pki、 和show security policies命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/2 {
gigether-options {
redundant-parent reth1;
}
}
ge-0/0/3 {
gigether-options {
redundant-parent reth0;
}
}
lo0 {
unit 0 {
family inet {
address 10.100.1.100/24;
}
}
redundant-pseudo-interface-options {
redundancy-group 1;
}
}
reth0 {
redundant-ether-options {
redundancy-group 1;
}
unit 0 {
family inet {
address 192.168.81.1/8;
}
}
}
reth1 {
redundant-ether-options {
redundancy-group 1;
}
unit 0 {
family inet {
address 10.2.2.1/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@host# show security ike
proposal prop_ike {
authentication-method rsa-signatures;
dh-group group5;
authentication-algorithm sha1;
encryption-algorithm aes-256-cbc;
}
policy ikepol1 {
mode main;
proposals prop_ike;
certificate {
local-certificate Hub_ID;
}
}
gateway HUB_GW {
ike-policy ikepol1;
dynamic distinguished-name wildcard DC=Domain_component;
dynamic ike-user-type group-ike-id;
local-identity distinguished-name;
external-interface reth1;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal prop_ipsec {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm aes-192-cbc;
lifetime-seconds 3600;
lifetime-kilobytes 150000;
}
policy ipsecpol1 {
perfect-forward-secrecy {
keys group5;
}
proposals prop_ipsec;
}
vpn HUB_VPN {
bind-interface st0.1;
ike {
gateway HUB_GW;
ipsec-policy ipsecpol1;
}
traffic-selector ts1 {
local-ip 192.0.0.0/8;
remote-ip 172.0.0.0/8;
}
}
[edit]
user@host# show security pki
ca-profile rsa {
ca-identity rsa;
revocation-check {
disable;
}
}
[edit]
user@host# show security zones
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.1;
reth0.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
lo0.0;
reth1.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
如果完成设备配置,请从配置模式输入 commit。
配置分支
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 172.16.1.1/24 set interfaces ge-0/0/3 unit 0 family inet address 10.2.2.253/24 set interfaces st0 unit 1 family inet set security ike proposal prop_ike authentication-method rsa-signatures set security ike proposal prop_ike dh-group group5 set security ike proposal prop_ike authentication-algorithm sha1 set security ike proposal prop_ike encryption-algorithm aes-256-cbc set security ike policy ikepol1 mode main set security ike policy ikepol1 proposals prop_ike set security ike policy ikepol1 certificate local-certificate Spoke1_ID set security ike gateway SPOKE_GW ike-policy ikepol1 set security ike gateway SPOKE_GW address 10.2.2.1 set security ike gateway SPOKE_GW local-identity distinguished-name set security ike gateway SPOKE_GW remote-identity distinguished-name container DC=Domain_component set security ike gateway SPOKE_GW external-interface ge-0/0/3.0 set security ike gateway SPOKE_GW version v1-only set security ipsec proposal prop_ipsec protocol esp set security ipsec proposal prop_ipsec authentication-algorithm hmac-sha1-96 set security ipsec proposal prop_ipsec encryption-algorithm aes-192-cbc set security ipsec proposal prop_ipsec lifetime-seconds 3600 set security ipsec proposal prop_ipsec lifetime-kilobytes 150000 set security ipsec policy ipsecpol1 perfect-forward-secrecy keys group5 set security ipsec policy ipsecpol1 proposals prop_ipsec set security ipsec vpn SPOKE_VPN bind-interface st0.1 set security ipsec vpn SPOKE_VPN ike gateway SPOKE_GW set security ipsec vpn SPOKE_VPN ike ipsec-policy ipsecpol1 set security ipsec vpn SPOKE_VPN traffic-selector ts1 local-ip 172.0.0.0/8 set security ipsec vpn SPOKE_VPN traffic-selector ts1 remote-ip 192.0.0.0/8 set security ipsec vpn SPOKE_VPN establish-tunnels immediately set security pki ca-profile rsa ca-identity rsa set security pki ca-profile rsa revocation-check disable set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces st0.1 set security zones security-zone trust interfaces ge-0/0/3.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security policies default-policy permit-all
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅 CLI 用户指南中的在配置模式下使用 CLI 编辑器。
要配置集线器,请执行以下操作:
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 172.16.1.1/24 user@host# set ge-0/0/3 unit 0 family inet address 10.2.2.253/24 user@host# set st0 unit 1 family inet
配置第 1 阶段选项。
[edit security ike proposal prop_ike] user@host# set authentication-method rsa-signatures user@host# set dh-group group5 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-256-cbc [edit security ike policy ikepol1] user@host# set mode main user@host# set proposals prop_ike user@host# set certificate local-certificate Spoke1_ID [edit security ike gateway SPOKE_GW] user@host# set ike-policy ikepol1 user@host# set address 10.2.2.1 user@host# set local-identity distinguished-name user@host# set remote-identity distinguished-name container DC=Domain_component user@host# set external-interface ge-0/0/3.0 user@host# set version v1-only
配置第 2 阶段选项。
[edit security ipsec proposal prop_ipsec] user@host# set protocol esp user@host# set authentication-algorithm hmac-sha1-96 user@host# set encryption-algorithm aes-192-cbc user@host# set lifetime-seconds 3600 user@host# set lifetime-kilobytes 150000 [edit security ipsec policy ipsecpol1] user@host# set perfect-forward-secrecy keys group5 user@host# set proposals prop_ipsec [edit security ipsec SPOKE_VPN] user@host# set bind-interface st0.1 user@host# set ike gateway SPOKE_GW user@host# set ike ipsec-policy ipsecpol1 user@host# set traffic-selector ts1 local-ip 172.0.0.0/8 user@host# set traffic-selector ts1 remote-ip 192.0.0.0/8 user@host# set establish-tunnels immediately
配置证书信息。
[edit security pki] user@host# set ca-profile rsa ca-identity rsa user@host# set ca-profile rsa revocation-check disable
配置安全区域。
[edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.1 user@host# set interfaces ge-0/0/3.0 [edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces ge-0/0/1.0 [edit security policies] user@host# set default-policy permit-all
结果
在配置模式下,输入 show interfaces、 show security ike、 show security zonesshow security ipsecshow security pki、 和show security policies命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 172.16.1.1/24;
}
}
}
ge-0/0/3 {
unit 0 {
family inet {
address 10.2.2.253/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@host# show security ike
proposal prop_ike {
authentication-method rsa-signatures;
dh-group group5;
authentication-algorithm sha1;
encryption-algorithm aes-256-cbc;
}
policy ikepol1 {
mode main;
proposals prop_ike;
certificate {
local-certificate Spoke1_ID;
}
}
gateway SPOKE_GW {
ike-policy ikepol1;
address 10.2.2.1;
local-identity distinguished-name;
remote-identity distinguished-name container DC=Domain_component;
external-interface ge-0/0/3.0;
version v1-only;
}
[edit]
user@host# show security ipsec
proposal prop_ipsec {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm aes-192-cbc;
lifetime-seconds 3600;
lifetime-kilobytes 150000;
}
policy ipsecpol1 {
perfect-forward-secrecy {
keys group5;
}
proposals prop_ipsec;
}
vpn SPOKE_VPN {
bind-interface st0.1;
ike {
gateway SPOKE_GW;
ipsec-policy ipsecpol1;
}
traffic-selector ts1 {
local-ip 172.0.0.0/8;
remote-ip 192.0.0.0/8;
}
establish-tunnels immediately;
}
[edit]
user@host# show security pki
ca-profile rsa {
ca-identity rsa;
revocation-check {
disable;
}
}
[edit]
user@host# show security zones
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.1;
ge-0/0/3.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
如果完成设备配置,请从配置模式输入 commit。
验证
确认配置工作正常。
验证隧道
目的
验证是否已在 AutoVPN 中心和分支之间建立隧道。
操作
在操作模式下,在中枢上输入 show security ike security-associations 和 show security ipsec security-associations 命令。
user@host> show security ike security-associations
node0:
--------------------------------------------------------------------------
Index State Initiator cookie Responder cookie Mode Remote Address
1350248074 UP d195bce6ccfcf9af 8f1569c6592c8408 Main 10.2.2.253
user@host> show security ipsec security-associations
node0:
--------------------------------------------------------------------------
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<77594650 ESP:aes-cbc-192/sha1 ac97cb1 2799/ 150000 - root 500 10.2.2.253
>77594650 ESP:aes-cbc-192/sha1 828dc013 2798/ 150000 - root 500 10.2.2.253
user@host> show security ipsec security-associations detail
node0:
--------------------------------------------------------------------------
ID: 77594650 Virtual-system: root, VPN Name: HUB_VPN
Local Gateway: 10.2.2.1, Remote Gateway: 10.2.2.253
Traffic Selector Name: ts1
Local Identity: ipv4(192.0.0.0-192.255.255.255)
Remote Identity: ipv4(172.0.0.0-172.255.255.255)
Version: IKEv1
DF-bit: clear, Bind-interface: st0.1
Port: 500, Nego#: 2, Fail#: 0, Def-Del#: 0 Flag: 0x24608b29
Tunnel events:
Tue Dec 30 2014 11:30:21 -0800: IPSec SA negotiation successfully completed (1 times)
Tue Dec 30 2014 11:30:20 -0800: Tunnel is ready. Waiting for trigger event or peer to trigger negotiation (1 times)
Tue Dec 30 2014 11:30:20 -0800: IKE SA negotiation successfully completed (3 times)
Location: FPC 5, PIC 0, KMD-Instance 1
Direction: inbound, SPI: ac97cb1, AUX-SPI: 0
Hard lifetime: Expires in 2796 seconds
Lifesize Remaining: 150000 kilobytes
Soft lifetime: Expires in 2211 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Location: FPC 5, PIC 0, KMD-Instance 1
Direction: outbound, SPI: 828dc013, AUX-SPI: 0
Hard lifetime: Expires in 2796 seconds
Lifesize Remaining: 150000 kilobytes
Soft lifetime: Expires in 2211 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
在操作模式下,在分支上输入 show security ike security-associations 和 show security ipsec security-associations 命令。
user@host> show security ike security-associations
Index State Initiator cookie Responder cookie Mode Remote Address
276505646 UP d195bce6ccfcf9af 8f1569c6592c8408 Main 10.2.2.1
user@host> show security ipsec security-associations
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<69206018 ESP:aes-cbc-192/sha1 828dc013 2993/ 150000 - root 500 10.2.2.1
>69206018 ESP:aes-cbc-192/sha1 ac97cb1 2993/ 150000 - root 500 10.2.2.1
user@host> show security ipsec security-associations detail
ID: 69206018 Virtual-system: root, VPN Name: SPOKE_VPN
Local Gateway: 10.2.2.253, Remote Gateway: 10.2.2.1
Traffic Selector Name: ts1
Local Identity: ipv4(172.0.0.0-172.255.255.255)
Remote Identity: ipv4(192.0.0.0-192.255.255.255)
Version: IKEv1
DF-bit: clear, Bind-interface: st0.1
Port: 500, Nego#: 0, Fail#: 0, Def-Del#: 0 Flag: 0x2c608b29
Tunnel events:
Tue Dec 30 2014 11:30:20 -0800: IPSec SA negotiation successfully completed (1 times)
Tue Dec 30 2014 11:30:20 -0800: IKE SA negotiation successfully completed (1 times)
Tue Dec 30 2014 11:26:11 -0800: Tunnel is ready. Waiting for trigger event or peer to trigger negotiation (1 times)
Location: FPC 1, PIC 0, KMD-Instance 1
Direction: inbound, SPI: 828dc013, AUX-SPI: 0
Hard lifetime: Expires in 2991 seconds
Lifesize Remaining: 150000 kilobytes
Soft lifetime: Expires in 2369 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Location: FPC 1, PIC 0, KMD-Instance 1
Direction: outbound, SPI: ac97cb1, AUX-SPI: 0
Hard lifetime: Expires in 2991 seconds
Lifesize Remaining: 150000 kilobytes
Soft lifetime: Expires in 2369 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。中心显示一个到分支的活动隧道,而分支显示一个到中心的活动隧道。
如果未列出 IKE 第 1 阶段的 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在中心辐射上匹配。
如果未列出 IKE 第 2 阶段的 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在中心辐射上匹配。
验证流量选择器
目的
验证流量选择器。
操作
在操作模式下,在中枢上输入 show security ipsec traffic-selector interface-name st0.1 命令。
user@host> show security ipsec traffic-selector interface-name st0.1 node0: -------------------------------------------------------------------------- Source IP Destination IP Interface Tunnel-id IKE-ID 192.0.0.0-192.255.255.255 172.0.0.0-172.255.255.255 st0.1 77594650 DC=Domain_component, CN=Spoke1_ID, OU=Sales, O=XYZ, L=Sunnyvale, ST=CA, C=US
在操作模式下,在分支上输入 show security ipsec traffic-selector interface-name st0.1 命令。
user@host> show security ipsec traffic-selector interface-name st0.1 Source IP Destination IP Interface Tunnel-id IKE-ID 172.0.0.0-172.255.255.255 192.0.0.0-192.255.255.255 st0.1 69206018 DC=Domain_component, CN=Hub_ID, OU=Sales, O=XYZ, L=Sunnyvale, ST=CA, C=US
意义
流量选择器是 IKE 对等方之间的协议,如果流量与指定的本地和远程地址对匹配,则允许流量通过隧道。仅允许符合流量选择器的流量通过 SA。流量选择器在发起方和响应方(SRX 系列集线器)之间进行协商。
示例:通过 AutoVPN 和流量选择器确保 VPN 隧道可用性
地理冗余是指部署多个地理位置相距较远的站点,以便即使发生停电、自然灾害或其他影响站点的灾难性事件,流量也可以继续流经提供商网络。在移动提供商网络中,多个演进节点 B (eNodeB) 设备可以通过 SRX 系列防火墙上的地理冗余 IPsec VPN 网关连接到核心网络。到 eNodeB 设备的备用路由使用动态路由协议分发到核心网络。
此示例在 SRX 系列防火墙上配置具有多个流量选择器的 AutoVPN 中心,以确保 eNodeB 设备存在异地冗余 IPsec VPN 网关。自动路由插入 (ARI) 用于在集线器上的路由表中自动插入指向 eNodeB 设备的路由。然后,ARI 路由通过 BGP 分发到提供商的核心网络。该示例使用基于证书的身份验证。要使用预共享密钥进行身份验证,请设置示例中 所示的类似配置:使用 iBGP 配置基本 AutoVPN。
要求
此示例使用以下硬件和软件组件:
-
在机箱群集中连接并配置的两个 SRX 系列防火墙。机箱群集是 AutoVPN 集线器 A。
-
配置为 AutoVPN 中心 B 的 SRX 系列防火墙。
-
Junos OS 版本 12.3X48-D10 或更高版本。
-
eNodeB 设备,可通过 AutoVPN 集线器建立 IPsec VPN 隧道。eNodeB 设备是使用 AutoVPN 集线器启动 VPN 隧道的第三方网络设备提供商。
-
在集线器和 eNodeB 设备中注册的数字证书,允许设备相互进行身份验证。
准备工作:
-
提交本地证书请求时,获取证书颁发机构 (CA) 的地址及其所需的信息(例如质询密码)。
-
在每个设备中注册数字证书。请参阅 注册证书。
此示例使用 BGP 动态路由协议将发向 eNodeB 设备的路由播发至核心网络。
概述
在此示例中,两个 AutoVPN 中心在 SRX 系列防火墙上配置了多个流量选择器,以便为 eNodeB 设备提供地理冗余 IPsec VPN 网关。ARI 会自动在集线器上的路由表中插入到 eNodeB 设备的路由。然后,ARI 路由通过 BGP 分发到提供商的核心网络。
在 AutoVPN 集线器和 eNodeB 设备上配置的某些第 1 阶段和第 2 阶段 IKE 隧道选项必须具有相同的值。 表 20 显示此示例中使用的值:
|
选项 |
value |
|---|---|
|
IKE 提案: |
|
|
身份验证方法 |
rsa-signatures |
|
Diffie-Hellman (DH) 组 |
group5 |
|
身份验证算法 |
sha-1 |
|
加密算法 |
aes-256-cbc |
|
IKE 策略: |
|
|
证书 |
本地证书 |
|
IKE 网关: |
|
|
动态 |
可分辨名称通配符 DC=Common_component |
|
IKE 用户类型 |
组 IKE ID |
|
失效对等体检测 |
探测器-空闲-隧道 |
|
本地标识 |
可分辨名称 |
|
版本 |
仅 v2 |
|
IPsec 提议: |
|
|
协议 |
esp |
|
身份验证算法 |
HMAC-SHA1-96 |
|
加密算法 |
aes-256-cbc |
|
IPsec 策略: |
|
|
完全向前保密 (PFS) 组 |
group5 |
在此示例中,允许所有流量的默认安全策略用于所有设备。应为生产环境配置更严格的安全策略。请参阅 安全策略概述。为简单起见,SRX 系列防火墙上的配置允许所有类型的入站流量;不建议将此配置用于生产部署。
配置
配置中心 A
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/2 gigether-options redundant-parent reth1 set interfaces ge-0/0/3 gigether-options redundant-parent reth0 set interfaces ge-8/0/2 gigether-options redundant-parent reth1 set interfaces ge-8/0/3 gigether-options redundant-parent reth0 set interfaces lo0 unit 0 family inet address 10.100.1.100/24 set interfaces lo0 redundant-pseudo-interface-options redundancy-group 1 set interfaces reth0 redundant-ether-options redundancy-group 1 set interfaces reth0 unit 0 family inet address 172.16.2.1/24 set interfaces reth1 redundant-ether-options redundancy-group 1 set interfaces reth1 unit 0 family inet address 10.2.2.1/24 set interfaces st0 unit 1 family inet set security ike proposal prop_ike authentication-method rsa-signatures set security ike proposal prop_ike dh-group group5 set security ike proposal prop_ike authentication-algorithm sha1 set security ike proposal prop_ike encryption-algorithm aes-256-cbc set security ike policy ph1_ike_policy proposals prop_ike set security ike policy ph1_ike_policy certificate local-certificate HubA_certificate set security ike gateway HUB_GW ike-policy ph1_ike_policy set security ike gateway HUB_GW dynamic distinguished-name wildcard DC=Common_component set security ike gateway HUB_GW dynamic ike-user-type group-ike-id set security ike gateway HUB_GW dead-peer-detection probe-idle-tunnel set security ike gateway HUB_GW local-identity distinguished-name set security ike gateway HUB_GW external-interface reth1 set security ike gateway HUB_GW version v2-only set security ipsec proposal prop_ipsec protocol esp set security ipsec proposal prop_ipsec authentication-algorithm hmac-sha1-96 set security ipsec proposal prop_ipsec encryption-algorithm aes-256-cbc set security ipsec policy ph2_ipsec_policy perfect-forward-secrecy keys group5 set security ipsec policy ph2_ipsec_policy proposals prop_ipsec set security ipsec vpn HUB_VPN bind-interface st0.1 set security ipsec vpn HUB_VPN ike gateway HUB_GW set security ipsec vpn HUB_VPN ike ipsec-policy ph2_ipsec_policy set security ipsec vpn HUB_VPN traffic-selector ts1 local-ip 172.16.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts1 remote-ip 10.50.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts2 local-ip 172.16.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts2 remote-ip 10.30.0.0/16 set protocols bgp group internal-peers type internal set protocols bgp group internal-peers local-address 172.16.2.1 set protocols bgp group internal-peers export inject_ts1_routes set protocols bgp group internal-peers export inject_ts2_routes set protocols bgp group internal-peers export inject_up_routes set protocols bgp group internal-peers neighbor 172.16.2.4 set policy-options policy-statement inject_ts1_routes term cp_allow from protocol static set policy-options policy-statement inject_ts1_routes term cp_allow from route-filter 10.30.1.0/24 orlonger set policy-options policy-statement inject_ts1_routes term cp_allow from route-filter 10.30.1.0/24 orlonger set policy-options policy-statement inject_ts1_routes term cp_allow then next-hop self set policy-options policy-statement inject_ts1_routes term cp_allow then accept set policy-options policy-statement inject_ts2_routes term mp_allow from protocol static set policy-options policy-statement inject_ts2_routes term mp_allow from route-filter 10.50.1.0/24 orlonger set policy-options policy-statement inject_ts2_routes term mp_net_allow from route-filter 10.50.2.0/24 orlonger set policy-options policy-statement inject_ts2_routes term mp_net_allow then next-hop self set policy-options policy-statement inject_ts2_routes term mp_net_allow then accept set policy-options policy-statement inject_up_routes term up_allow from protocol static set policy-options policy-statement inject_up_routes term up_allow from route-filter 172.16.1.0/24 orlonger set policy-options policy-statement inject_up_routes term up_allow from route-filter 172.16.2.0/24 orlonger set policy-options policy-statement inject_up_routes term up_allow then next-hop self set policy-options policy-statement inject_up_routes term up_allow then accept set security pki ca-profile csa ca-identity csa set security pki ca-profile csa revocation-check disable set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces st0.1 set security zones security-zone trust interfaces reth0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces reth1.0 set security policies default-policy permit-all
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅 CLI 用户指南中的在配置模式下使用 CLI 编辑器。
要配置中心 A,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/2 gigether-options redundant-parent reth1 user@host# set ge-0/0/3 gigether-options redundant-parent reth0 user@host# set ge-8/0/2 gigether-options redundant-parent reth1 user@host# set ge-8/0/3 gigether-options redundant-parent reth0 user@host# set lo0 unit 0 family inet address 10.100.1.100/24 user@host# set lo0 redundant-pseudo-interface-options redundancy-group 1 user@host# set reth0 redundant-ether-options redundancy-group 1 user@host# set reth0 unit 0 family inet address 172.16.2.1/24 user@host# set reth1 redundant-ether-options redundancy-group 1 user@host# set reth1 unit 0 family inet address 10.2.2.1/24 user@host# set st0 unit 1 family inet
-
配置第 1 阶段选项。
[edit security ike proposal prop_ike] user@host# set authentication-method rsa-signatures user@host# set dh-group group5 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-256-cbc [edit security ike policy ph1_ike_policy] user@host# set proposals prop_ike user@host# set certificate local-certificate HubA_certificate [edit security ike gateway HUB_GW] user@host# set ike-policy ph1_ike_policy user@host# set dynamic distinguished-name wildcard DC=Common_component user@host# set dynamic ike-user-type group-ike-id user@host# set dead-peer-detection probe-idle-tunnel user@host# set local-identity distinguished-name user@host# set external-interface reth1 user@host# set version v2-only
-
配置第 2 阶段选项。
[edit security ipsec proposal prop_ipsec] user@host# set protocol esp user@host# set authentication-algorithm hmac-sha1-96 user@host# set encryption-algorithm aes-256-cbc [edit security ipsec policy ph2_ipsec_policy] user@host# set perfect-forward-secrecy keys group5 user@host# set proposals prop_ipsec [edit security ipsec vpn HUB_VPN] user@host# set bind-interface st0.1 user@host# set ike gateway HUB_GW user@host# set ike ipsec-policy ph2_ipsec_policy user@host# set traffic-selector ts1 local-ip 172.16.0.0/16 user@host# set traffic-selector ts1 remote-ip 10.50.0.0/16 user@host# set traffic-selector ts2 local-ip 172.16.0.0/16 user@host# set traffic-selector ts2 remote-ip 10.30.0.0/16
-
配置 BGP 路由协议。
[edit protocols bgp group internal-peers] user@host# set type internal user@host# set local-address 172.16.2.1 user@host# set export inject_ts1_routes user@host# set export inject_ts2_routes user@host# set export inject_up_routes user@host# set neighbor 172.16.2.4
-
配置路由选项。
[edit policy-options policy-statement inject_ts1_routes] user@host# set term cp_allow from protocol static user@host# set term cp_allow from route-filter 10.30.2.0/24 orlonger user@host# set term cp_allow from route-filter 10.30.1.0/24 orlonger user@host# set term cp_allow then next-hop self user@host# set term cp_allow then accept [edit policy-options policy-statement inject_ts2_routes] user@host# set term mp_allow from protocol static user@host# set term mp_allow from route-filter 10.50.1.0/24 orlonger user@host# set term mp_allow from route-filter 10.50.2.0/24 orlonger user@host# set term mp_allow then next-hop self user@host# set term mp_allow then accept [edit policy-options policy-statement inject_up_routes] user@host# set term up_allow from protocol static user@host# set term up_allow from route-filter 172.16.1.0/24 orlonger user@host# set term up_allow from route-filter 172.16.2.0/24 orlonger user@host# set term up_allow then next-hop self user@host# set term up_allow then accept
-
配置证书信息。
[edit security pki] user@host# set ca-profile csa ca-identity csa user@host# set ca-profile csa revocation-check disable
-
配置安全区域。
[edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.1 user@host# set interfaces reth0.0 [edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces lo0.0 user@host# set interfaces reth1.0 [edit security policies] user@host# set default-policy permit-all
结果
在配置模式下,输入 show interfaces show security ike、 show security ipsec、 show security pkishow security zonesshow protocols bgpshow policy-options和 show security policies 命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/2 {
gigether-options {
redundant-parent reth1;
}
}
ge-0/0/3 {
gigether-options {
redundant-parent reth0;
}
}
ge-8/0/2 {
gigether-options {
redundant-parent reth1;
}
}
ge-8/0/3 {
gigether-options {
redundant-parent reth0;
}
}
lo0 {
unit 0 {
family inet {
address 10.100.1.100/24;
}
}
redundant-pseudo-interface-options {
redundancy-group 1;
}
}
reth0 {
redundant-ether-options {
redundancy-group 1;
}
unit 0 {
family inet {
address 172.16.2.1/16;
}
}
}
reth1 {
redundant-ether-options {
redundancy-group 1;
}
unit 0 {
family inet {
address 10.2.2.1/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@host# show security ike
proposal prop_ike {
authentication-method rsa-signatures;
dh-group group5;
authentication-algorithm sha1;
encryption-algorithm aes-256-cbc;
}
policy ph1_ike_policy {
proposals prop_ike;
certificate {
local-certificate HubA_certificate;
}
}
gateway HUB_GW {
ike-policy ph1_ike_policy;
dynamic {
distinguished-name {
wildcard DC=Common_component;
}
ike-user-type group-ike-id;
}
dead-peer-detection {
probe-idle-tunnel;
}
local-identity distinguished-name;
external-interface reth1;
version v2-only;
}
[edit]
user@host# show security ipsec
proposal prop_ipsec {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm aes-256-cbc;
}
policy ph2_ipsec_policy {
perfect-forward-secrecy {
keys group5;
}
proposals prop_ipsec;
}
vpn HUB_VPN {
bind-interface st0.1;
ike {
gateway HUB_GW;
ipsec-policy ph2_ipsec_policy;
}
traffic-selector ts1 {
local-ip 172.16.0.0/16;
remote-ip 10.50.0.0/16;
}
traffic-selector ts2 {
local-ip 172.16.0.0/16;
remote-ip 10.30.0.0/16;
}
}
[edit]
user@host# show protocols bgp
group internal-peers {
type internal;
local-address 172.16.2.1;
export [ inject_ts1_routes inject_ts2_routes inject_up_routes ];
neighbor 172.16.2.4;
}
[edit]
user@host# show policy-options
policy-statement inject_ts1_routes {
term cp_allow {
from {
protocol static;
route-filter 10.30.2.0/24 orlonger;
route-filter 10.30.1.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
policy-statement inject_ts2_routes {
term mp_allow {
from {
protocol static;
route-filter 10.50.1.0/24 orlonger;
route-filter 10.50.2.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
policy-statement inject_up_routes {
term up_allow {
from {
protocol static;
route-filter 172.16.1.0/24 orlonger;
route-filter 172.16.2.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
[edit]
user@host# show security pki
ca-profile csa {
ca-identity csa;
revocation-check {
disable;
}
}
[edit]
user@host# show security zones
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.1;
reth0.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
lo0.0;
reth1.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
如果完成设备配置,请从配置模式输入 commit。
配置中心 B
CLI 快速配置
要快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改详细信息,以便与网络配置匹配,将命令复制并粘贴到 [edit] 层级的 CLI 中,然后从配置模式进入 commit 。
set interfaces ge-0/0/1 unit 0 family inet address 10.4.4.1/24 set interfaces ge-0/0/2 unit 0 family inet address 172.16.1.1/16 set interfaces lo0 unit 0 family inet address 10.100.1.101/24 set interfaces st0 unit 1 family inet set security ike proposal prop_ike authentication-method rsa-signatures set security ike proposal prop_ike dh-group group5 set security ike proposal prop_ike authentication-algorithm sha1 set security ike proposal prop_ike encryption-algorithm aes-256-cbc set security ike policy ph1_ike_policy proposals prop_ike set security ike policy ph1_ike_policy certificate local-certificate HubB_certificate set security ike gateway HUB_GW ike-policy ph1_ike_policy set security ike gateway HUB_GW dynamic distinguished-name wildcard DC=Common_component set security ike gateway HUB_GW dynamic ike-user-type group-ike-id set security ike gateway HUB_GW dead-peer-detection probe-idle-tunnel set security ike gateway HUB_GW local-identity distinguished-name set security ike gateway HUB_GW external-interface ge-0/0/1 set security ike gateway HUB_GW version v2-only set security ipsec proposal prop_ipsec protocol esp set security ipsec proposal prop_ipsec authentication-algorithm hmac-sha1-96 set security ipsec proposal prop_ipsec encryption-algorithm aes-256-cbc set security ipsec policy ph2_ipsec_policy perfect-forward-secrecy keys group5 set security ipsec policy ph2_ipsec_policy proposals prop_ipsec set security ipsec vpn HUB_VPN bind-interface st0.1 set security ipsec vpn HUB_VPN ike gateway HUB_GW set security ipsec vpn HUB_VPN ike ipsec-policy ph2_ipsec_policy set security ipsec vpn HUB_VPN traffic-selector ts1 local-ip 172.16.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts1 remote-ip 10.50.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts2 local-ip 172.16.0.0/16 set security ipsec vpn HUB_VPN traffic-selector ts2 remote-ip 10.30.0.0/8 set protocols bgp group internal-peers type internal set protocols bgp group internal-peers local-address 172.16.1.1 set protocols bgp group internal-peers export inject_ts1_routes set protocols bgp group internal-peers export inject_ts2_routes set protocols bgp group internal-peers export inject_up_routes set policy-options policy-statement inject_ts1_routes term cp_allow from protocol static set policy-options policy-statement inject_ts1_routes term cp_allow from route-filter 10.30.2.0/24 orlonger set policy-options policy-statement inject_ts1_routes term cp_allow from route-filter 10.30.1.0/24 orlonger set policy-options policy-statement inject_ts1_routes term cp_allow then next-hop self set policy-options policy-statement inject_ts1_routes term cp_allow then accept set policy-options policy-statement inject_ts2_routes term mp_allow from protocol static set policy-options policy-statement inject_ts2_routes term mp_allow from route-filter 10.50.1.0/24 orlonger set policy-options policy-statement inject_ts2_routes term mp_net_allow from route-filter 10.50.2.0/24 orlonger set policy-options policy-statement inject_ts2_routes term mp_net_allow then next-hop self set policy-options policy-statement inject_ts2_routes term mp_net_allow then accept set policy-options policy-statement inject_up_routes term up_allow from protocol static set policy-options policy-statement inject_up_routes term up_allow from route-filter 172.16.1.0/24 orlonger set policy-options policy-statement inject_up_routes term up_allow from route-filter 172.16.2.0/24 orlonger set policy-options policy-statement inject_up_routes term up_allow then next-hop self set policy-options policy-statement inject_up_routes term up_allow then accept set security pki ca-profile csa ca-identity csa set security pki ca-profile csa revocation-check disable set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces st0.1 set security zones security-zone trust interfaces ge-0/0/2.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces ge-0/0/1.0 set security policies default-policy permit-all
分步过程
下面的示例要求您在各个配置层级中进行导航。有关操作说明,请参阅 CLI 用户指南中的在配置模式下使用 CLI 编辑器。
要配置中心 B,请执行以下操作:
-
配置接口。
[edit interfaces] user@host# set ge-0/0/1 unit 0 family inet address 10.4.4.1/24 user@host# set ge-0/0/2 unit 0 family inet address 172.16.1.1/16 user@host# set lo0 unit 0 family inet address 10.100.1.101/24 user@host# set st0 unit 1 family inet
-
配置第 1 阶段选项。
[edit security ike proposal prop_ike] user@host# set authentication-method rsa-signatures user@host# set dh-group group5 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-256-cbc [edit security ike policy ph1_ike_policy] user@host# set proposals prop_ike user@host# set certificate local-certificate HubB_certificate [edit security ike gateway HUB_GW] user@host# set ike-policy ph1_ike_policy user@host# set dynamic distinguished-name wildcard DC=Common_component user@host# set dynamic ike-user-type group-ike-id user@host# set dead-peer-detection probe-idle-tunnel user@host# set local-identity distinguished-name user@host# set external-interface ge-0/0/1 user@host# set version v2-only
-
配置第 2 阶段选项。
[edit security ipsec proposal prop_ipsec] user@host# set protocol esp user@host# set authentication-algorithm hmac-sha1-96 user@host# set encryption-algorithm aes-256-cbc [edit security ipsec policy ph2_ipsec_policy] user@host# set perfect-forward-secrecy keys group5 user@host# set proposals prop_ipsec [edit security ipsec vpn HUB_VPN] user@host# set bind-interface st0.1 user@host# set ike gateway HUB_GW user@host# set ike ipsec-policy ph2_ipsec_policy user@host# set traffic-selector ts1 local-ip 172.16.0.0/16 user@host# set traffic-selector ts1 remote-ip 10.50.0.0/16 user@host# set traffic-selector ts2 local-ip 172.16.0.0/16 user@host# set traffic-selector ts2 remote-ip 10.30.0.0/16
-
配置 BGP 路由协议。
[edit protocols bgp group internal-peers] user@host# set type internal user@host# set local-address 172.16.1.1 user@host# set export inject_ts1_routes user@host# set export inject_ts2_routes user@host# set export inject_up_routes user@host# set neighbor 172.16.1.2
-
配置路由选项。
[edit policy-options policy-statement inject_ts1_routes] user@host# set term cp_allow from protocol static user@host# set term cp_allow from route-filter 10.30.2.0/24 orlonger user@host# set term cp_allow from route-filter 10.30.1.0/24 orlonger user@host# set term cp_allow then next-hop self user@host# set term cp_allow then accept [edit policy-options policy-statement inject_ts2_routes] user@host# set term mp_allow from protocol static user@host# set term mp_allow from route-filter 10.50.1.0/24 orlonger user@host# set term mp_allow from route-filter 10.50.2.0/24 orlonger user@host# set term mp_allow then next-hop self user@host# set term mp_allow then accept [edit policy-options policy-statement inject_up_routes] user@host# set term up_allow from protocol static user@host# set term up_allow from route-filter 172.16.1.0/24 orlonger user@host# set term up_allow from route-filter 172.16.2.0/24 orlonger user@host# set term up_allow then next-hop self user@host# set term up_allow then accept
-
配置证书信息。
[edit security pki] user@host# set ca-profile csa ca-identity csa user@host# set ca-profile csa revocation-check disable
-
配置安全区域。
[edit security zones security-zone trust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces st0.1 user@host# set interfaces ge-0/0/2.0 [edit security zones security-zone untrust] user@host# set host-inbound-traffic system-services all user@host# set host-inbound-traffic protocols all user@host# set interfaces lo0.0 user@host# set interfaces ge-0/0/1.0 [edit security policies] user@host# set default-policy permit-all
结果
在配置模式下,输入 show interfaces show security ike、 show security ipsec、 show security zonesshow protocols bgpshow security pki、 和show security policies命令,以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host# show interfaces
ge-0/0/1 {
unit 0 {
family inet {
address 10.4.4.1/24;
}
}
}
ge-0/0/2 {
unit 0 {
family inet {
address 172.16.1.1/16;
}
}
}
lo0 {
unit 0 {
family inet {
address 10.100.1.101/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@host# show security ike
proposal prop_ike {
authentication-method rsa-signatures;
dh-group group5;
authentication-algorithm sha1;
encryption-algorithm aes-256-cbc;
}
policy ph1_ike_policy {
proposals prop_ike;
certificate {
local-certificate HubB_certificate;
}
}
gateway HUB_GW {
ike-policy ph1_ike_policy;
dynamic {
distinguished-name {
wildcard DC=Common_component;
}
ike-user-type group-ike-id;
}
dead-peer-detection {
probe-idle-tunnel;
}
local-identity distinguished-name;
external-interface reth1;
version v2-only;
}
[edit]
user@host# show security ipsec
proposal prop_ipsec {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm aes-256-cbc;
}
policy ph2_ipsec_policy {
perfect-forward-secrecy {
keys group5;
}
proposals prop_ipsec;
}
vpn HUB_VPN {
bind-interface st0.1;
ike {
gateway HUB_GW;
ipsec-policy ph2_ipsec_policy;
}
traffic-selector ts1 {
local-ip 172.16.0.0/16;
remote-ip 10.50.0.0/16;
}
traffic-selector ts2 {
local-ip 172.16.0.0/16;
remote-ip 10.30.0.0/16;
}
}
[edit]
user@host# show protocols bgp
group internal-peers {
type internal;
local-address 172.16.1.1;
export [ inject_ts1_routes inject_ts2_routes inject_up_routes ];
neighbor 172.16.1.2;
}
user@host# show policy-options
policy-statement inject_ts1_routes {
term cp_allow {
from {
protocol static;
route-filter 10.30.2.0/24 orlonger;
route-filter 10.30.1.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
policy-statement inject_ts2_routes {
term mp_allow {
from {
protocol static;
route-filter 10.50.1.0/24 orlonger;
route-filter 10.50.2.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
policy-statement inject_up_routes {
term up_allow {
from {
protocol static;
route-filter 172.16.1.0/24 orlonger;
route-filter 172.16.2.0/24 orlonger;
}
then {
next-hop self;
accept;
}
}
}
[edit]
user@host# show security pki
ca-profile csa {
ca-identity csa;
revocation-check {
disable;
}
}
[edit]
user@host# show security zones
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
st0.1;
ge-0/0/2.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
lo0.0;
}
}
[edit]
user@host# show security policies
default-policy {
permit-all;
}
如果完成设备配置,请从配置模式输入 commit。
配置 eNodeB(示例配置)
分步过程
-
本示例中的 eNodeB 配置仅供参考。详细的 eNodeB 配置信息超出了本文档的范围。eNodeB 配置必须包含以下信息:
-
本地证书 (X.509v3) 和 IKE 身份信息
-
SRX 系列 IKE 身份信息和公有 IP 地址
-
与 SRX 系列集线器上的配置匹配的第 1 阶段和第 2 阶段提议
-
结果
此示例中的 eNodeB 设备使用 strongSwan 开源软件进行基于 IPsec 的 VPN 连接:
config setup
plutostart=yes
plutodebug=all
charondebug="ike 4, cfg 4, chd 4, enc 1"
charonstart=yes #ikev2 deamon"
nat_traversal=yes #<======= need to enable even no nat_t
conn %default
ikelifetime=60m
keylife=45m
rekeymargin=2m
keyingtries=4
mobike=no
conn Hub_A
keyexchange=ikev2
authby=pubkey
ike=aes256-sha-modp1536
esp=aes256-sha1-modp1536
leftcert=/usr/local/etc/ipsec.d/certs/fight02Req.pem.Email.crt
left=10.5.5.1 # self if
leftsubnet=10.1.1.0/24 # left subnet
leftid="CN=fight02, DC=Common_component, OU=Dept, O=Company, L=City, ST=CA, C=US " # self id
right=10.2.2.1 # peer if
rightsubnet=10.1.1.0/24 # peer net for proxy id
rightid="DC=Domain_component, CN=HubA_certificate, OU=Dept, O=Company, L=City, ST=CA, C=US " # peer id
auto=add
leftfirewall=yes
dpdaction=restart
dpddelay=10
dpdtimeout=120
rekeyfuzz=10%
reauth=no
conn Hub_B
keyexchange=ikev2
authby=pubkey
ike=aes256-sha-modp1536
esp=aes192-sha1-modp1536
leftcert=/usr/local/etc/ipsec.d/certs/fight02Req.pem.Email.crt
left=10.5.5.1 # self if
leftsubnet=10.1.1.0/24 # self net for proxy id
leftid="CN=fight02, DC=Common_component, OU=Dept, O=Company, L=City, ST=CA, C=US " # self id
right=10.4.4.1 # peer if
rightsubnet=10.1.1.0/24 # peer net for proxy id
rightid="DC=Domain_component, CN=HubB_certificate, OU=Dept, O=Company, L=City, ST=CA, C=US " # peer id
auto=add
leftfirewall=yes
dpdaction=restart
dpddelay=10
dpdtimeout=120
rekeyfuzz=10%
reauth=no
验证
确认配置工作正常。
验证 AutoVPN 中枢上的隧道
目的
验证是否已在 AutoVPN 集线器和 eNodeB 设备之间建立隧道。
操作
在操作模式下,在中枢上输入 show security ike security-associations 和 show security ipsec security-associations 命令。
user@host> show security ike security-associations node0: -------------------------------------------------------------------------- Index State Initiator cookie Responder cookie Mode Remote Address 276505706 UP 16d6e53f0866b5cc ccd8ca944da7b63e IKEv2 10.5.5.1 1350247532 UP d5f0cb3a3b18cb92 91269f05527217a0 IKEv2 10.1.1.1 user@host> show security ipsec security-associations node0: -------------------------------------------------------------------------- Total active tunnels: 2 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <77594626 ESP:aes-cbc-192/sha1 a82bbc3 3600/ 64 - root 500 10.1.1.1 >77594626 ESP:aes-cbc-192/sha1 c930a858 3600/ 64 - root 500 10.1.1.1 <69206018 ESP:aes-cbc-192/sha1 2b437fc 3600/ 64 - root 500 10.5.5.1 >69206018 ESP:aes-cbc-192/sha1 c6e02755 3600/ 64 - root 500 10.5.5.1
意义
该 show security ike security-associations 命令会列出所有活动的 IKE 第 1 阶段 SA。该 show security ipsec security-associations 命令将列出所有活动的 IKE 第 2 阶段 SA。集线器显示两个活动隧道,每个 eNodeB 设备一个。
如果未列出 IKE 第 1 阶段的 SA,则第 1 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 1 阶段提议参数必须在集线器和 eNodeB 设备上匹配。
如果未列出 IKE 第 2 阶段的 SA,则第 2 阶段建立存在问题。检查配置中的 IKE 策略参数和外部接口设置。第 2 阶段提议参数必须在集线器和 eNodeB 设备上匹配。
验证流量选择器
目的
验证流量选择器。
操作
在操作模式下,输入 show security ipsec traffic-selector interface-name st0.1 命令。
user@host> show security ipsec traffic-selector interface-name st0.1 node0: -------------------------------------------------------------------------- Source IP Destination IP Interface Tunnel-id IKE-ID 10.1.1.0-10.1.1.255 10.1.1.0-10.1.1.255 st0.1 69206018 DC=Common_component, CN=enodebA, OU=Dept, O=Company, L=City, ST=CA, C=US 10.1.1.0-10.1.1.255 10.1.1.0-10.1.1.255 st0.1 77594626 DC=Common_component, CN=enodebB, OU=Dept, O=Company, L=City, ST=CA, C=US
意义
流量选择器是 IKE 对等方之间的协议,如果流量与指定的本地和远程地址对匹配,则允许流量通过隧道。仅允许符合流量选择器的流量通过 SA。流量选择器在发起方和响应方(SRX 系列集线器)之间进行协商。
验证 ARI 路由
目的
验证 ARI 路由是否已添加到路由表中。
操作
在操作模式下,输入 show route 命令。
user@host> show route
inet.0: 23 destinations, 23 routes (22 active, 0 holddown, 1 hidden)
+ = Active Route, - = Last Active, * = Both
10.1.0.0/16 *[Static/5] 02:57:57
> to 2.2.2.253 via reth1.0
10.2.2.0/24 *[Direct/0] 02:58:43
> via reth1.0
10.2.2.1/32 *[Local/0] 02:59:25
Local via reth1.0
10.5.0.0/16 *[Static/5] 02:57:57
> to 2.2.2.253 via reth1.0
10.157.64.0/19 *[Direct/0] 21:54:52
> via fxp0.0
10.157.75.117/32 *[Local/0] 21:54:52
Local via fxp0.0
10.254.75.117/32 *[Direct/0] 21:54:52
> via lo0.0
10.30.1.0/24 *[ARI-TS/5] 02:28:10 [ARI route added based on TSi]
> via st0.1
10.50.1.0/24 *[ARI-TS/5] 02:28:26
> via st0.1
10.80.0.0/16 *[Direct/0] 02:57:57
> via reth0.0
10.80.1.1/32 *[Local/0] 02:57:57
Local via reth0.0
10.100.1.0/24 *[Direct/0] 02:57:57
> via lo0.0
10.100.1.100/32 *[Local/0] 02:57:57
Local via lo0.0
10.102.1.0/24 *[Static/5] 02:57:57
> to 10.2.2.253 via reth1.0
10.104.1.0/24 *[Static/5] 02:57:57
> to 10.2.2.253 via reth1.0
172.16.0.0/12 *[Static/5] 21:54:52
意义
自动路由插入 (ARI) 会自动为受远程隧道端点保护的远程网络和主机插入静态路由。将根据流量选择器中配置的远程 IP 地址创建路由。对于流量选择器,配置的远程地址将作为路由插入到与绑定到 VPN 的 st0 接口关联的路由实例中。
到 eNodeB 目的地 10 的静态路由。30.1.0/24 和 10.50.1.0/24 已添加到 SRX 系列集线器上的路由表中。这些路由可通过 st0.1 接口访问。
示例:使用预共享密钥配置 AutoVPN
此示例说明如何配置 VPN 网关用于对远程对等方进行身份验证的不同 IKE 预共享密钥。同样,要配置 VPN 网关用于验证远程对等方的相同 IKE 预共享密钥。
有关 AutoVPN 的端到端配置,请参阅本主题中的其他示例。
要求
此示例使用以下硬件和软件组件:
- MX240、MX480 和 MX960 以及支持 AutoVPN 的 MX-SPC3 和 Junos OS 21.1R1 版
- 或与支持 AutoVPN 的 SPC3 和 Junos OS 21.2R1 版SRX5000线路
- 或运行 iked 进程(带软件包
junos-ike) 和支持 AutoVPN 的 Junos OS 21.2R1 版的 vSRX 虚拟防火墙
配置不同的 IKE 预共享密钥
要配置 VPN 网关用于验证远程对等方的不同 IKE 预共享密钥,请执行以下操作。
- 使用 AutoVPN 中心在设备中配置 IKE 策略的种子预共享。
[edit] user@host# set security ike policy IKE_POL seeded-pre-shared-key ascii-text ascii-text
(也称为数字签名
user@host# set security ike policy IKE_POL seeded-pre-shared-key hexadecimal hexadecimal
例如:
user@host# set security ike policy IKE_POL seeded-pre-shared-key ascii-text ThisIsMySecretPreSharedkey
(也称为数字签名
user@host# set security ike policy IKE_POL seeded-pre-shared-key hexadecimal 5468697349734d79536563726563745072655368617265646b6579
- 使用网关名称和用户 ID 显示远程对等方的。
pre-shared key[edit] user@host> show security ike pre-shared-key gateway gateway-name user-id user-id
例如:
user@host> show security ike pre-shared-key gateway-name HUB_GW user-id user1@juniper.net
Pre-shared key: 79e4ea39f5c06834a3c4c031e37c6de24d46798a - 在远程对等设备上的 IKE 策略中配置生成的 PSK(“79e4ea39f5c06834a3c4c031e37c6de24d46798a”在 步骤 2 中)。
[edit] user@peer# set security ike policy IKE_POL pre-shared-key ascii-text generated-psk
例如:
user@peer# set security ike policy IKE_POL pre-shared-key ascii-text 79e4ea39f5c06834a3c4c031e37c6de24d46798a
- (可选)要绕过 IKE ID 验证并允许所有 IKE ID 类型,请在网关的 [编辑安全 IKE 网关gateway_name动态] 层次结构级别下配置
general-ikeid配置语句。[edit] user@host# set security ike gateway HUB_GW dynamic general-ikeid
结果
在配置模式下,输入 show security 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host> show security
ike {
proposal IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 750;
}
policy IKE_POL {
proposals IKE_PROP;
seeded-pre-shared-key ascii-text "$9$zoDln9pIEyWLN0BLNdboaFn/C0BRhSeM8"; ##SECRET-DATA
}
gateway HUB_GW {
ike-policy IKE_POL;
dynamic {
general-ikeid;
ike-user-type group-ike-id;
}
local-identity hostname hub.juniper.net;
external-interface lo0.0;
local-address 11.0.0.1;
version v2-only;
}
}
配置相同的 IKE 预共享密钥
要配置 VPN 网关用于验证远程对等方的相同 IKE 预共享密钥,请执行以下操作。
- 使用 AutoVPN 集线器在设备中配置 IKE 策略的通用
pre-shared-key。[edit] user@host# set security ike policy IKE_POL pre-shared-key ascii-text ascii text
例如:
user@host# # set security ike policy IKE_POL pre-shared-key ascii-text ThisIsMySecretPreSharedkey
- 为远程对等设备配置 IKE 上的通用
pre-shared-key策略。[edit] user@peer# set security ike policy IKE_POL pre-shared-key ascii-text ascii text
例如:
user@peer# set security ike policy IKE_POL pre-shared-key ascii-text ThisIsMySecretPreSharedkey
- (可选)要绕过 IKE ID 验证并允许所有 IKE ID 类型,请在网关的 [编辑安全 IKE 网关gateway_name动态] 层次结构级别下配置
general-ikeid配置语句。[edit] user@host# set security ike gateway HUB_GW dynamic general-ikeid
结果
在配置模式下,输入 show security 命令以确认您的配置。如果输出未显示预期的配置,请重复此示例中的说明,以便进行更正。
[edit]
user@host> show security
ike {
proposal IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 750;
}
policy IKE_POL {
proposals IKE_PROP;
pre-shared-key ascii-text "$9$wo2oGk.569pDi9p0BSys24"; ## SECRET-DATA
}
gateway HUB_GW {
ike-policy IKE_POL;
dynamic {
general-ikeid;
ike-user-type group-ike-id;
}
local-identity user-at-hostname user1@juniper.net;
external-interface lo0;
local-address 11.0.0.1;
version v2-only;
}
}在 P2MP 基础架构上配置组播支持
在启用多播支持之前,请确保满足 使用 PIM 的多播支持中列出的注意事项。
请参阅以下部分以配置和验证组播支持。
配置 组播接口
-
要在 st0.0 接口上启用 PIM,请使用
set protocols pim interface interface-name command:[edit] user@host# set protocols pim interface st0.0
这里介绍
st0.0的是安全隧道接口。 -
要在 st0.0 接口上为 P2MP 模式启用多点,请使用
set interfaces interface-name unit unit-number multipoint命令:[edit] user@host# set interfaces st0.0 unit 0 multipoint
-
要设置 st0.0 接口的 IPv4 地址,请使用
set interfaces interface-name unit unit-number family inet address IPv4 address以下命令:[edit] user@host# set interfaces st0.0 unit 0 family inet address 192.168.1.3/24
此处,192.168.1.3/24 是接口的 IP 地址。
-
要在 st0.0 接口上禁用 PIM,请使用选项
disable:[edit] user@host# set protocols pim interface st0.0 disable
用于验证组播配置的 CLI 命令
您可以使用以下命令验证组播配置。
-
若要列出 PIM 接口,请使用
show pim interfaces命令。 -
要列出已加入组播组的邻接方,请使用命令
show pim join extensive。 -
要查看 IP 组播转发表中的条目,请使用
show multicast route命令。 -
要查看组播下一跃点详细信息,请使用
show multicast next-hops detail命令。 -
要查看 IP 组播统计信息,请使用
show multicast statistics命令。 -
要查看转发表条目,请使用
show route forwarding-table extensive命令。
另请参阅
特定于平台的 AutoVPN 行为
使用 功能资源管理器 确认平台和版本对特定功能的支持。
使用下表查看您的平台特定于平台的行为。
特定于平台的 身份验证 行为
|
平台 |
差异 |
|---|---|
|
SRX 系列 |
|
特定于平台的 组播 行为
|
平台 |
差异 |
|---|---|
|
SRX 系列 |
|
变更历史表
是否支持某项功能取决于您使用的平台和版本。 使用 Feature Explorer 查看您使用的平台是否支持某项功能。
edit security ike gateway gateway-name dynamic] 层次结构级别配置 CLI 选项reject-duplicate-connection,以保留现有隧道会话并拒绝具有相同 IKE ID 的新隧道的协商请求。



