Configure Authentication Policy
Create authentication policies to control which users can access which resources on your network.
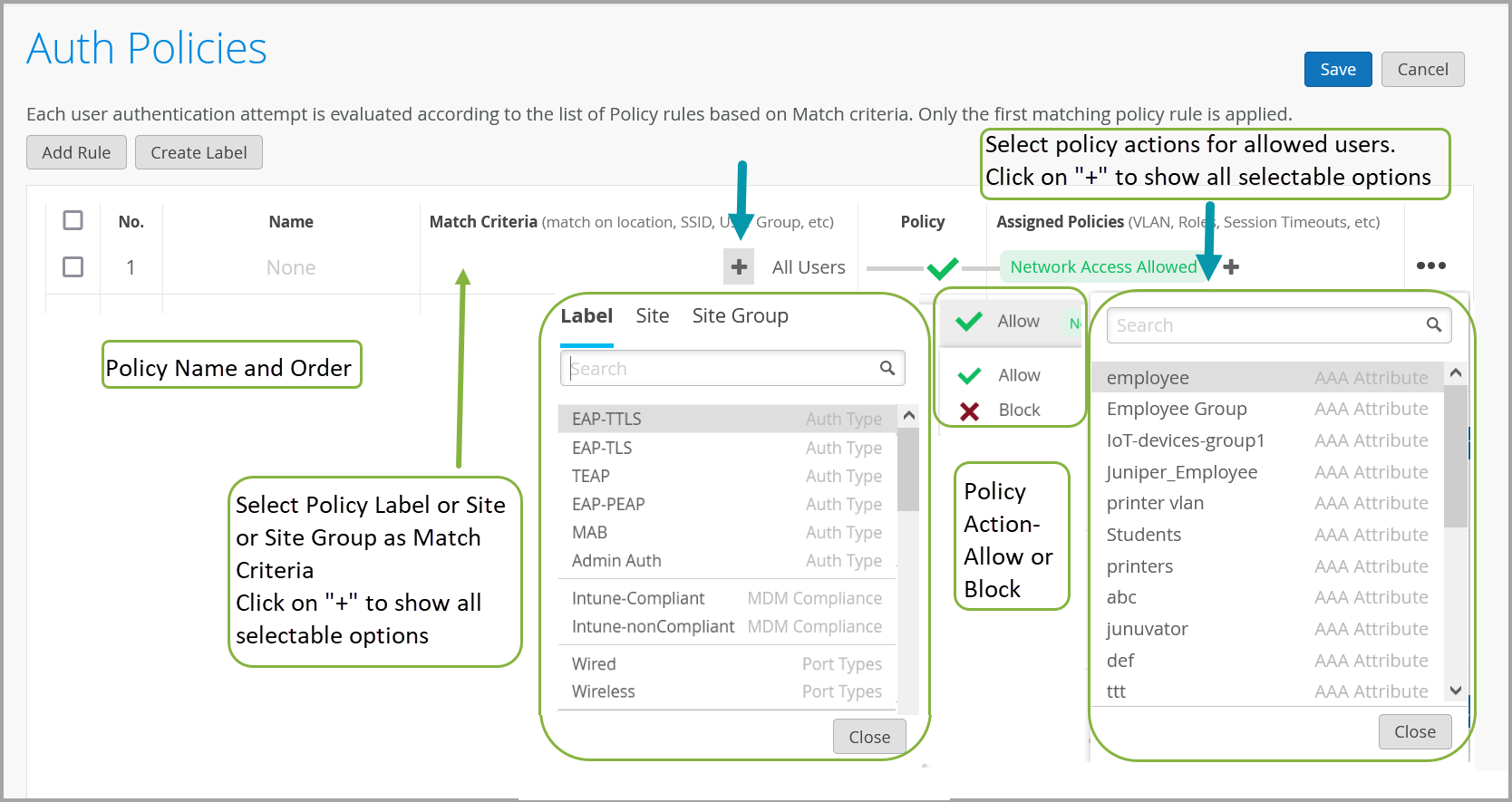
You must configure Juniper Mist Access Assurance with an authentication policy to authenticate end users or devices that attempt to access the network or applications.
The policy consists of a set of rules that devices and users must fulfill to get access to the network and use the network resources. Juniper Mist Access Assurance evaluates the authentication requests based on the specified policy conditions. If a user or device satisfies the conditions, Juniper Mist Access Assurance applies actions that either allow or deny access to the user or the device. These actions also apply attributes (VLAN. role) to the allowed users.
Juniper Mist Access Assurance uses "labels" as the policy matching criteria and also as a policy action for allowed users. You can create labels on the Authentication Policy Labels page or on the Authentication Policy page. See Configure Authentication Policy Labels for details.
Create Authentication Policy
To create an authentication policy: